X509
Summary #
In Cryptography, X.509 is an International Telecommunication Union (ITU) standard defining the format of public key certificates of Asymmetric Cryptography
wikipedia
overview of X509 certificate PDF by IBM #
An electronic document used to identify an individual, server, company or some other entity.
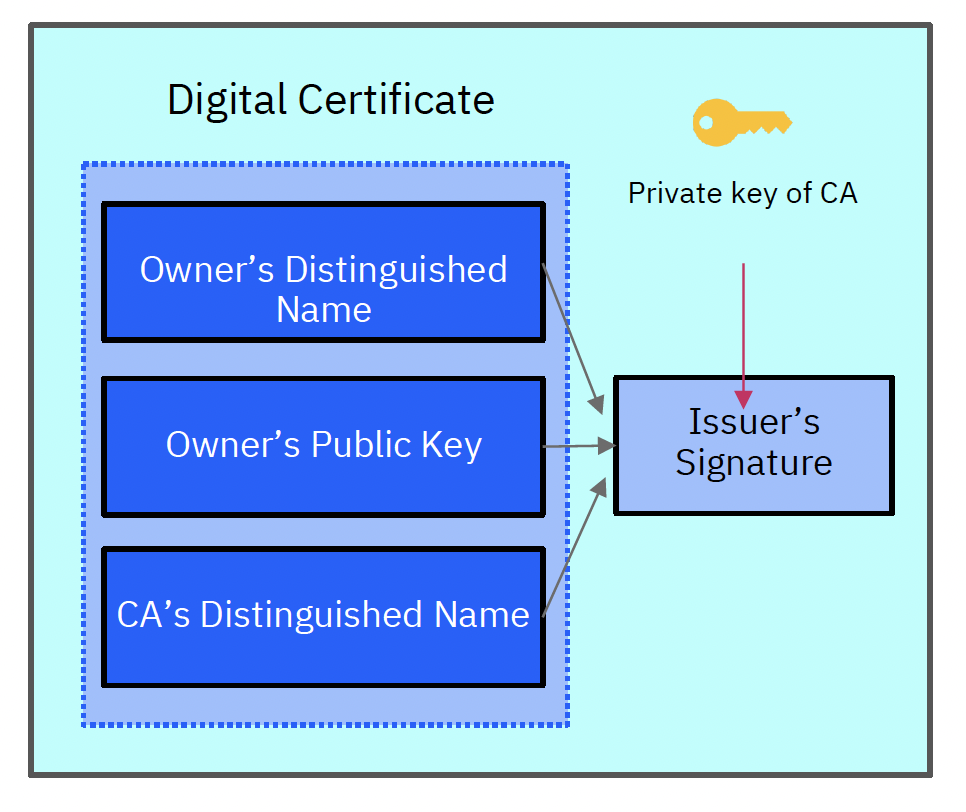
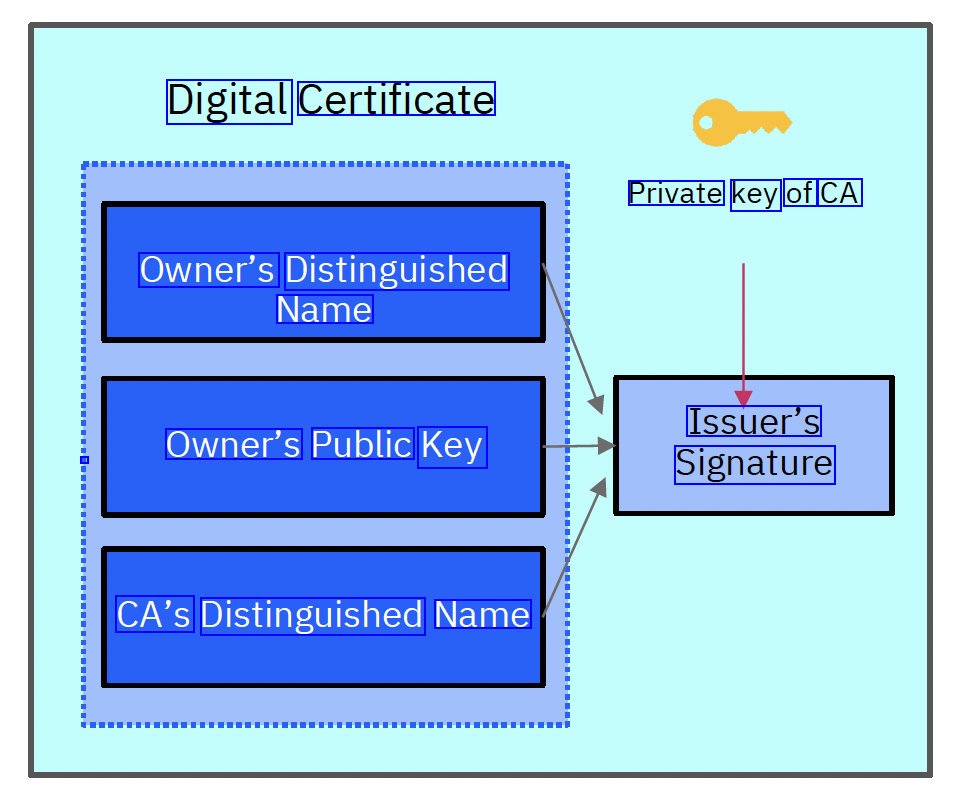
It contains the: #
- Public Key and
- is signed, by e.g. CA , with the private key to verify that it belongs to the sender.
Two purposes: #
- Establishes the owner’s identity
- Makes the owner’s public key available
Contains specific pieces of information #
about
- the identify of the certificate owner and,
- if applicable, the CA: Owner’s distinguished name of the owner
- Owner’s distinguished name of the owner of the public key, aka subject’s name
- subject’s name Issuer’s distinguished name, aka issuer’s name
- Owner’s public key itself•
- The time period during which the certificate is valid, aka the validity period
- Certificate’s serial number
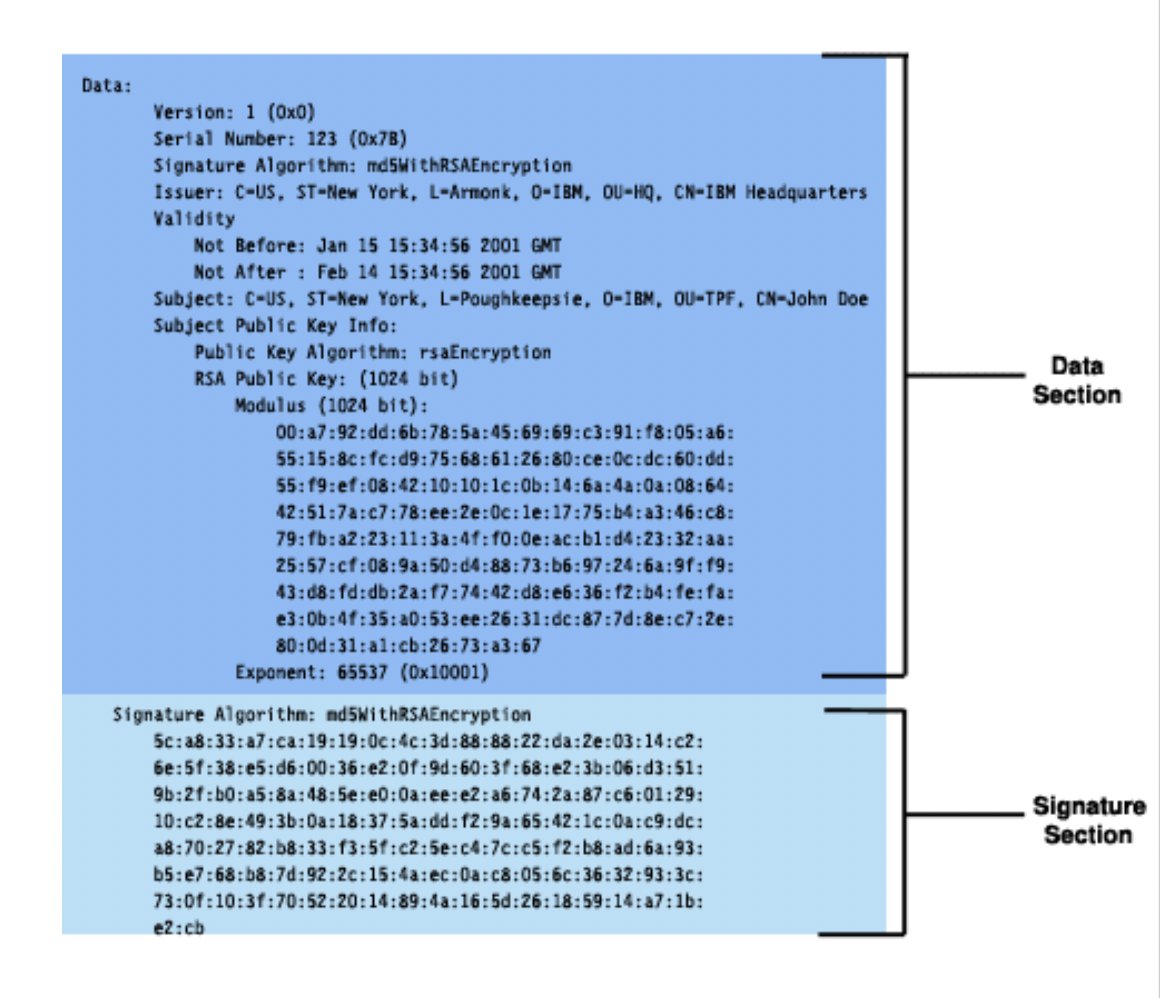
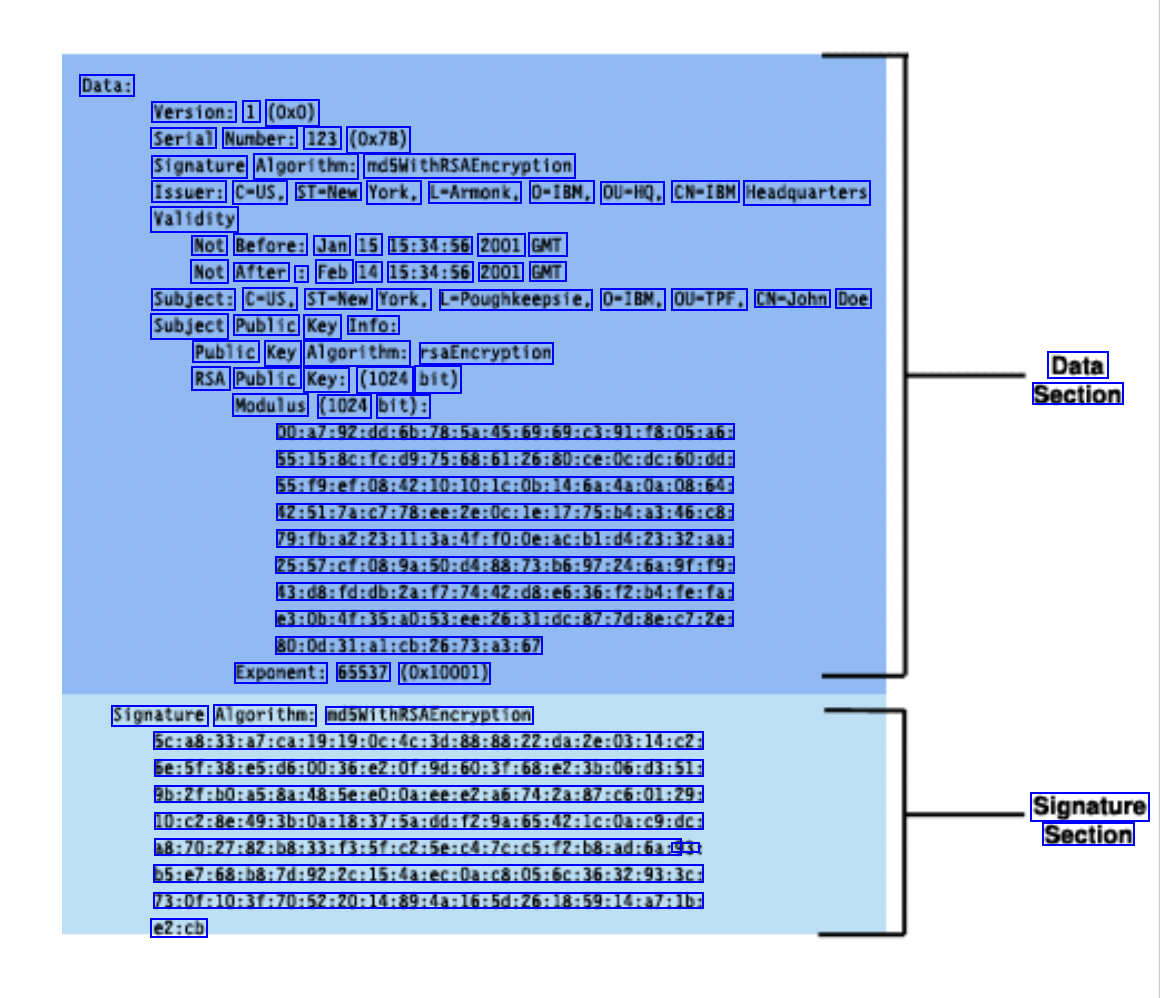
Certificate Structure #
Certificates include:
- X.509 version: specifies the version of the certificate
- Serial number: assigned by the issuing entity to distinguish the certificate
- Algorithm information: indicates the algorithm used for signing the certificate
- Issuer distinguished name: name of the entity issuing the certificate (typically a CA)
- Validity period: indicates the start and end date and time of the certificate’s validity
- Subject distinguished name: identity to which the certificate is issued
- Subject public key information: associated public key
Signature section includes:
- Cipher algorithm: algorithm used by the issuer to create a digital signature
- Digital signature for the CA: hash of all the information in the certificate
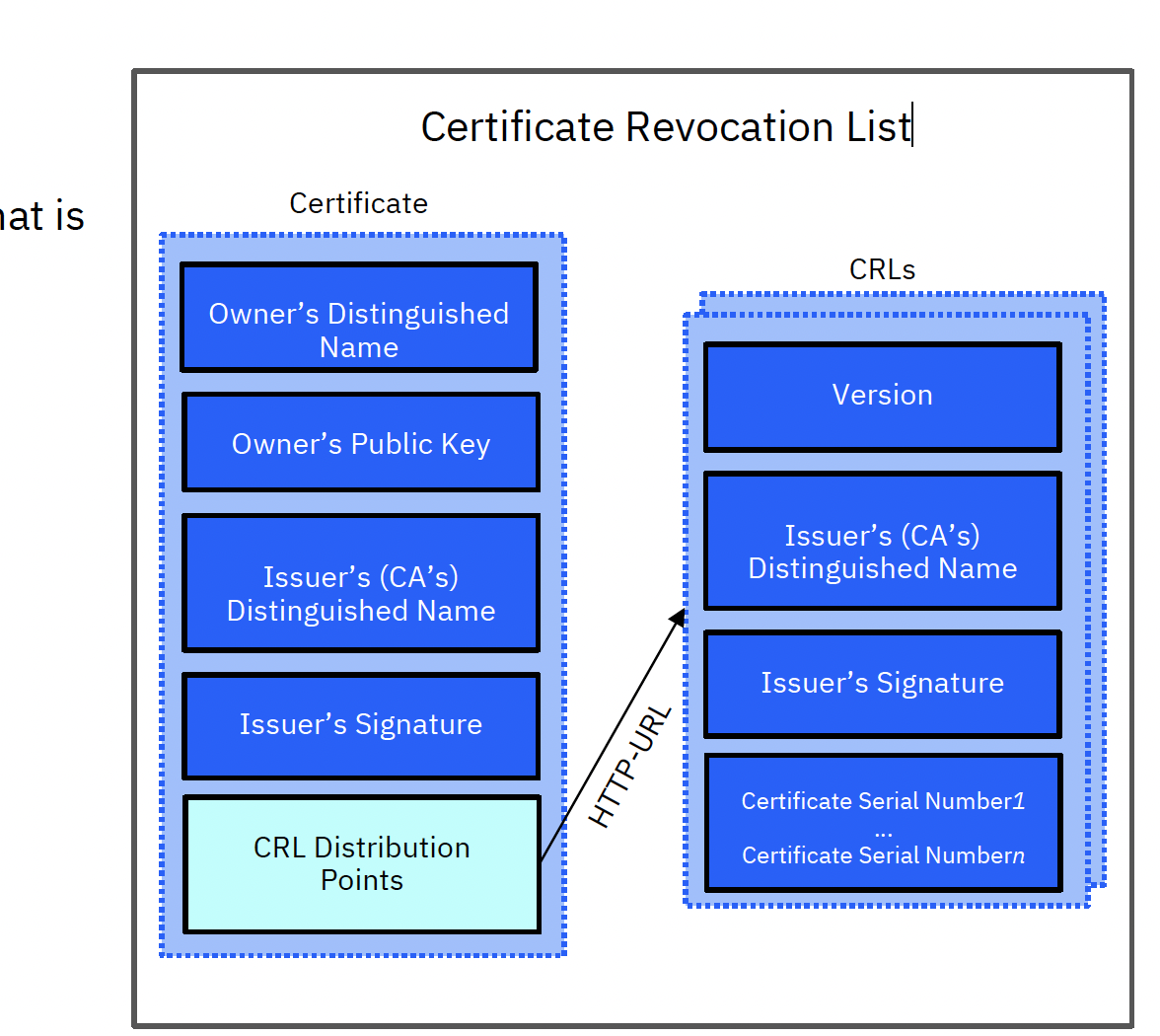
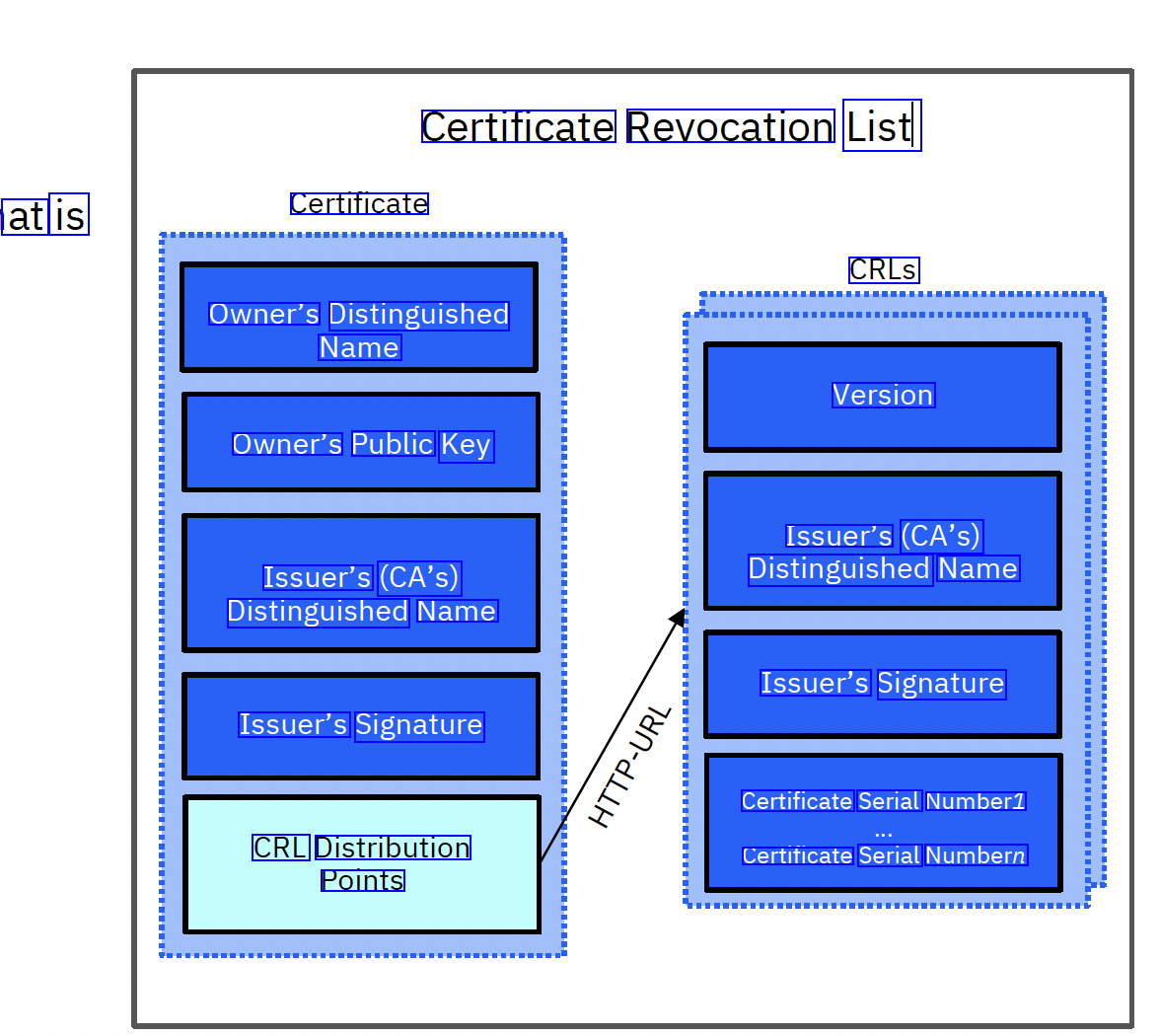
Certificate Revocation List #
Binds public key to an identity #
An X.509 certificate binds an identity to a public key using a digital signature. A certificate contains
- An identity (a hostname, or an organization, or an individual) and
- A public key (RSA, DSA, ECDSA, ed25519, etc.), and
- Is either signed by a CA or is self-signed.
When a certificate is signed by a trusted certificate authority #
- Someone holding that certificate can use the public key it contains to establish secure communications with another party, or
- Validate documents digitally signed by the corresponding private key.
X.509 v3 #
An X.509 v3 certificate contains an extension field that permits any number of additional fields to be added to the certificate. Certificate extensions provide a way of adding information such as alternative subject names and usage restrictions to certificates. Older Netscape servers, such as Red Hat Directory Server and Red Hat Certificate System, that were developed before PKIX part 1 standards were defined require Netscape-specific extensions. ref
Verification #
- Each X.509 certificate is signed with the private key of the issuer of the certificate. CSR includes public key and identity and CA verifies the CSR request and
- The signature can be checked using the associated public key.
- If the signature verification fails, the document was a. never signed or b. the document has been modified since the signature.
Use Cases #
Overview of Common Uses for Certificates in Internet Applications #
- Certificates play a key role in the following areas:
- Establishing secure connections: Used to establish a secure channel between parties.
- Ensuring authentication: Verifies the identity of the communicating parties.
- Enabling encryption: Secures the data being transferred.
Specific Applications #
- In addition to SSL/TLS for secure server-client connections, certificates are also used in the following:
- PEM/S/MIME for secure email
- Virtual Private Networks (VPNs)
- Secure electronic transactions
Additional Notes #
- This is just a subset of certificate usage. There are many other applications where certificates are utilized for various security purposes.
OCR of Images #
2023-09-12_11-30-50_screenshot.png #
Digital Certificate Private key of CA Owner's Distinguished Name Issuer's Signature Owner's Public L Key CA's Distinguished Name
2023-09-12_12-21-29_screenshot.png #
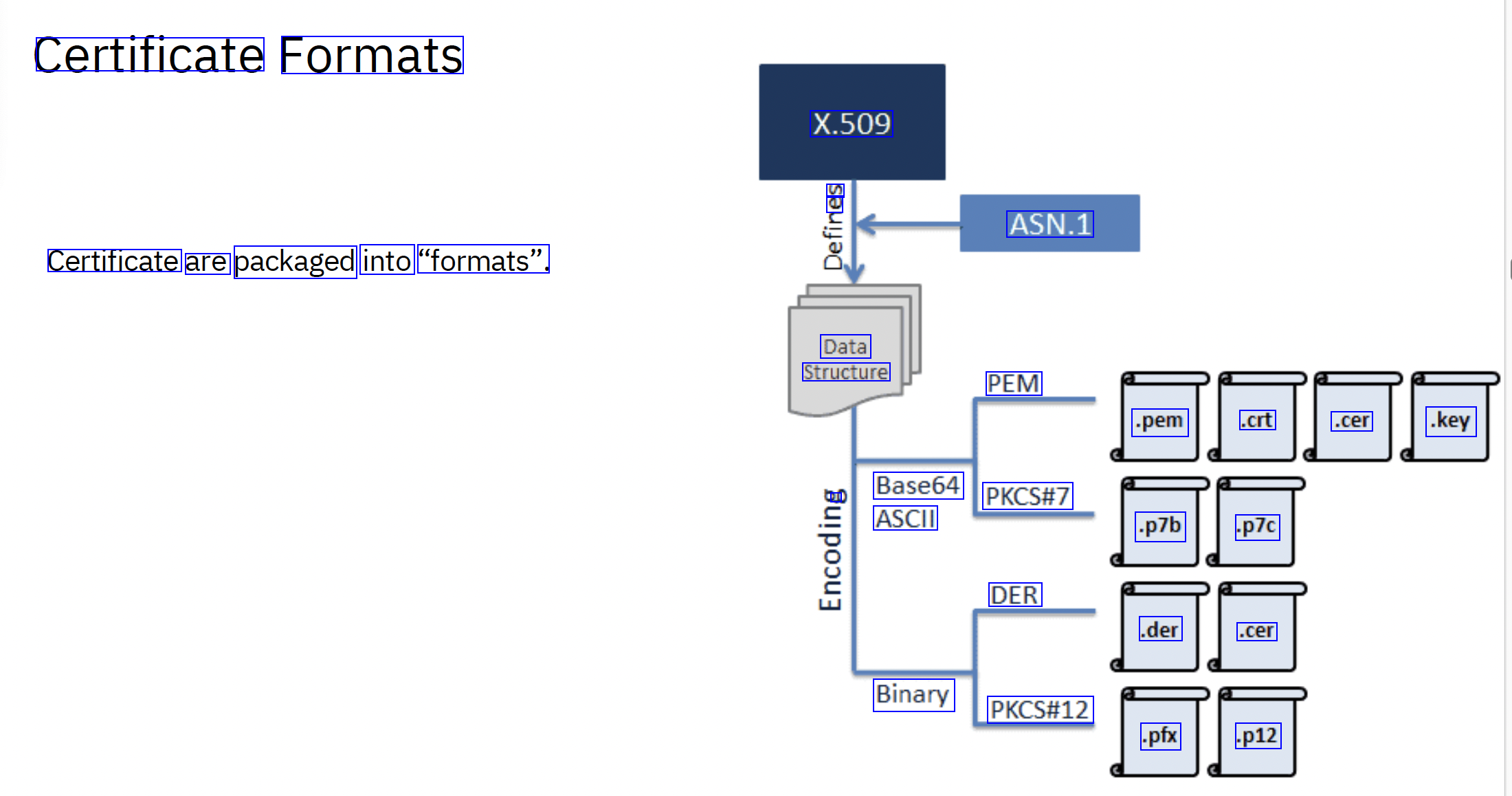
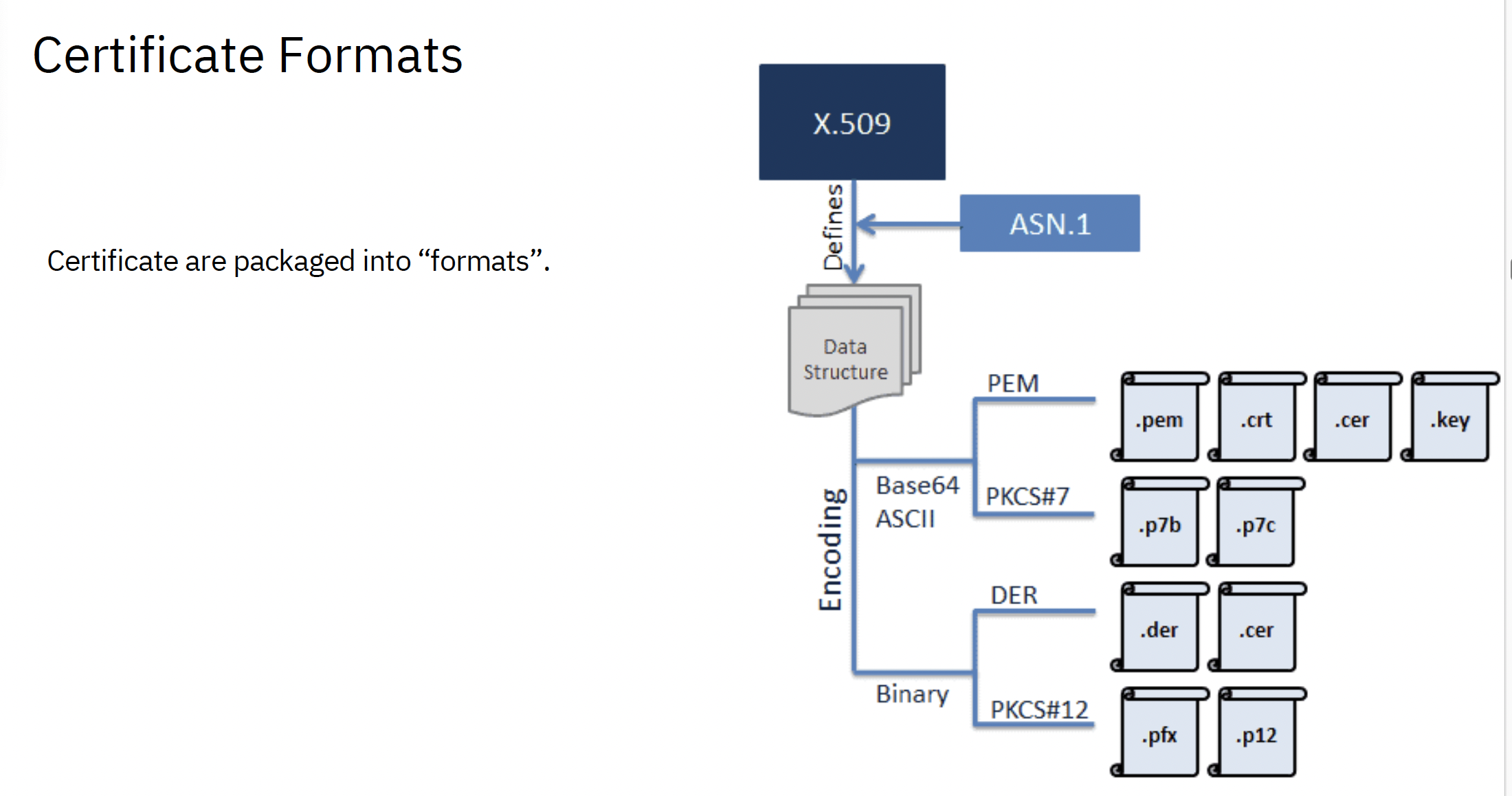
Certiticate Formats X.509 5 a ASN.1 Certificate are packaged into "formats". Data Structure PEM .pem .crt .cer .key - Base64 PKCS#7 ASCII .p7b .p7c DER .der .cer Binary PKCS#12 .pfx .p12
2023-09-12_12-26-02_screenshot.png #
Data: Version: 1 (0x0) Serial Number: 123 (0x7B) Signature Algorithm: mdswithRSAEncryption Issuer: C-US, ST-New York, L-Armonk, 0-IBM, OU-HQ, CN-IBM Headquarters Validity Not Before: Jan 15 15:34:56 2001 GMT Not After : Feb 14 15:34:56 2001 GMT Subject: C-US, ST-New York, L-Poughkeepsie, 0-IBM, OU-TPF, CN-John Doe Subject Public Key Info: Public Key Algorithm: rsaEncryption RSA Public Key: (1024 bit) Modulus (1024 bit): Data Section 00:a7:92:dd:6b:78:5a:45:69:69:c3:91:f8:05:a6: 55:15:8c:fc:d9:75:68:61:26:80:ce:0c:Oc:dc:60:dd: 55:f9:ef:08:42:10:10:1c:0b:14:6a:4a:4a:0a:08:64: 12:51:7a:c7:78:ee:2e:0c:le:17:75:b4:a3:46:C8: 79:fb:a2:23:11:3a:4f:f0:0e:ac:bl:d4:23:32:aa: 25:57:cf:08:9a:50:04:88:73:b6:97:24:6a:91:19: 43:d8:fd:db:2a:f7:74:42:d8:e6:36:f2:b4:fe:fa: e3:0b:4f:35:a0:53:ee:26:31:dC:87:7d:8e:c7:2e: 80:0d:31:al:cb:26:73:a3:67 Exponent: 65537 (Ox10001) Signature Algorithm: nd5WIthRSAEncryption 5c:a8:33:a7:ca:19:19:0c:0c:4c:3d:88:88:22:da:2e:2e:03:14:c2: 6e:5f:38:e5:d6:00:36:e2:0f:9d:60:3f:68:e2:3b:06:d3:51: 9b:2f:b0:a5:8a:48:5e:e0:0a:ee:e2:a6:74:2a:87:c6:01:29: 10:c2:8e:49:3b:0a:18:37:5a:dd:12:9a:65:42:1c:lc:0a:c9:dc: a8:70:27:82:b8:33:f3:5f:c2:5e:C4:C4:7c:c5:f2:b8:ad:6a:5 : b5:e7:68:b8:7d:92:2c:15:15:4a:ec:0a:c8:05:6c:36:36:32:93:3c: 73:0f:10:3f:70:52:20:14:89:4a:16:5d:26:18:59:59:14:a7:1b: Signature Section e2:cb
2023-09-12_11-39-59_screenshot.png #
Certificate Revocation List Certiticate at is CRLS Owner's Distinguished Name Version Owner's Public Key Issuer's (CA's) Distinguished Name Issuer's (CA's) Distinguished Name Issuer's Signature Issuer's Signature Certificate Serial Numberl Certificate Serial Numbern CRL Distribution Points