Security in OCI
tags :
Security #
 Security in the cloud is responsibility of tenant, similar to tenant is responsibility of
security inside house where as landlord is responsible for infrastructure security and reliability
Security in the cloud is responsibility of tenant, similar to tenant is responsibility of
security inside house where as landlord is responsible for infrastructure security and reliability
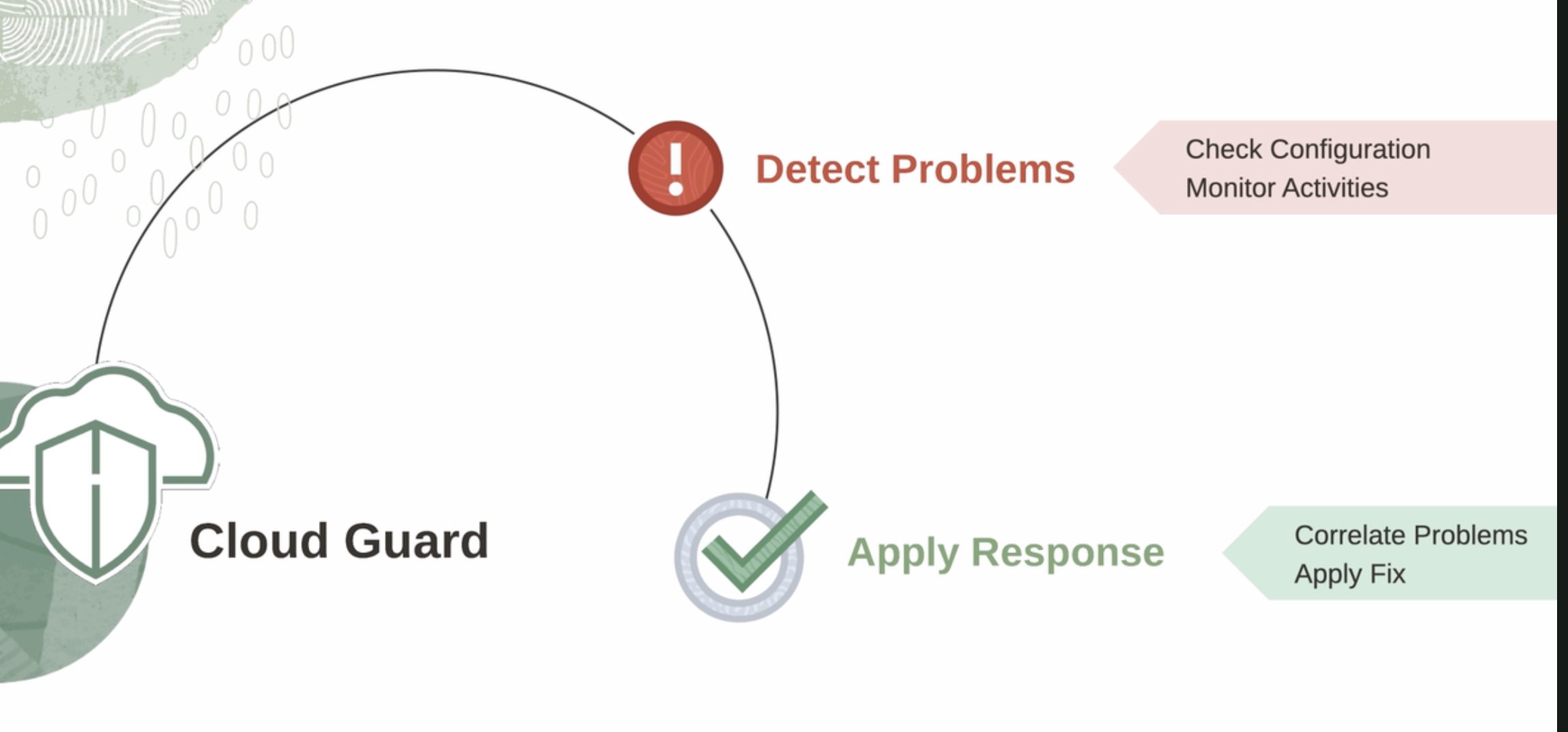
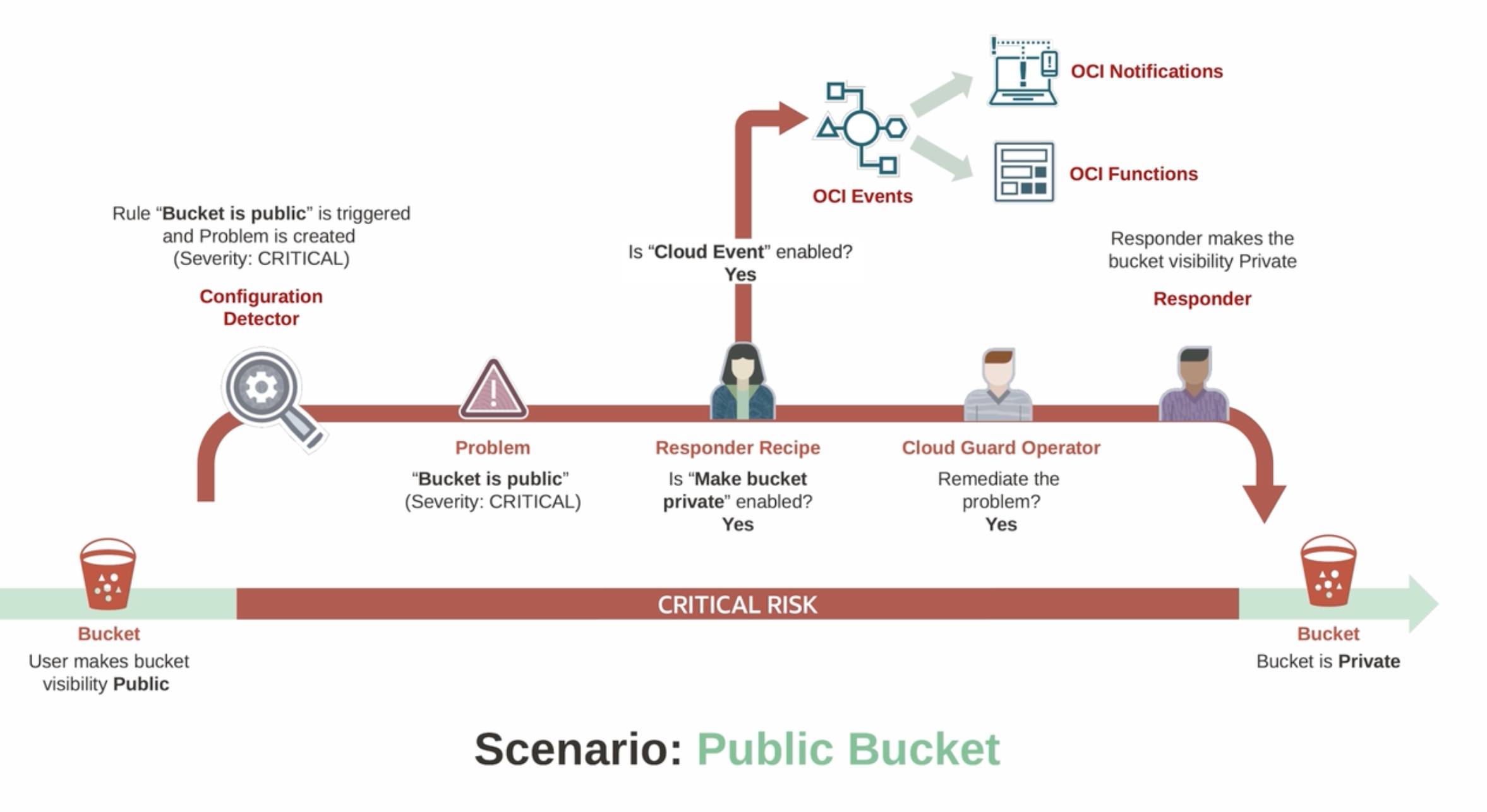
Example of Cloud Guard working
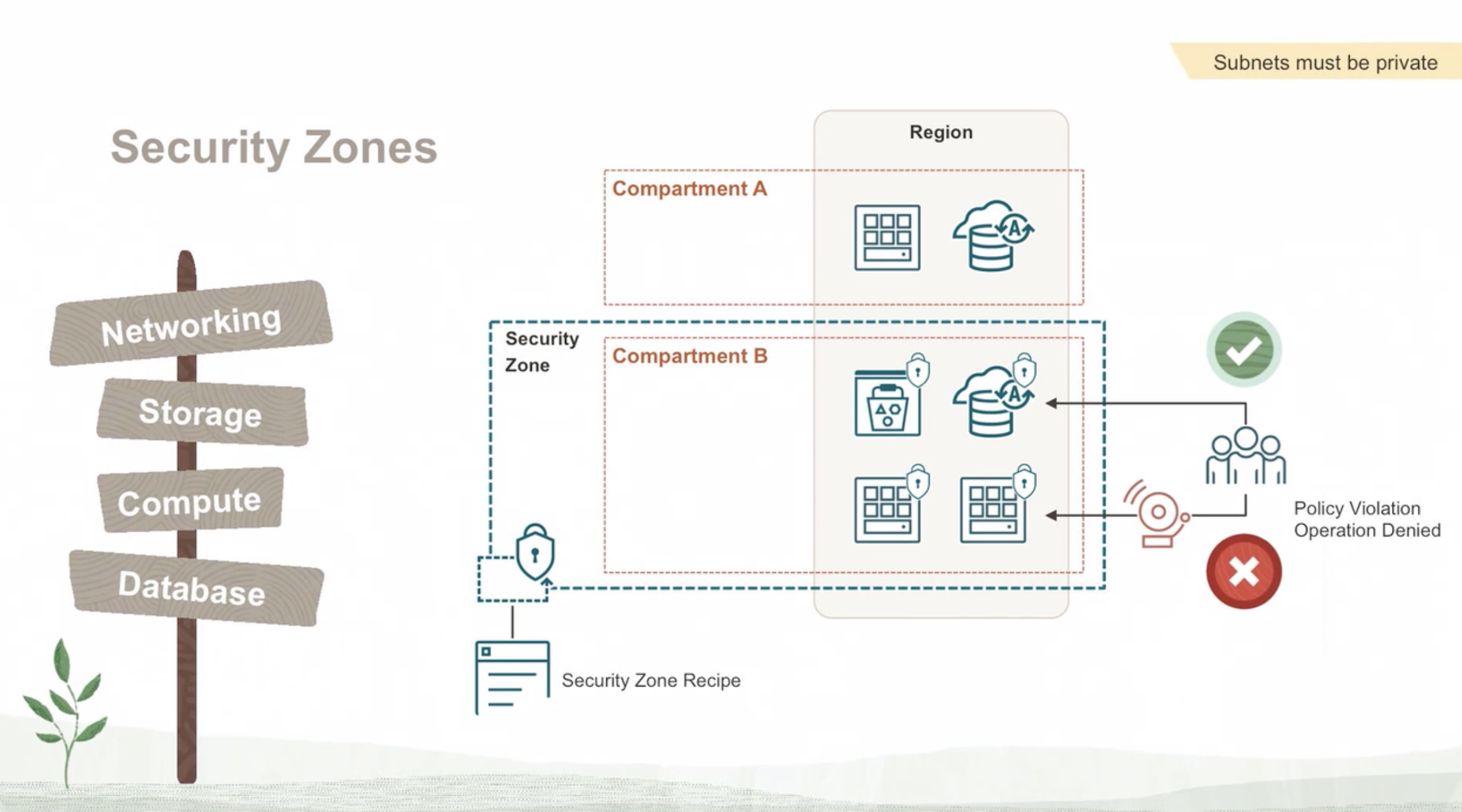
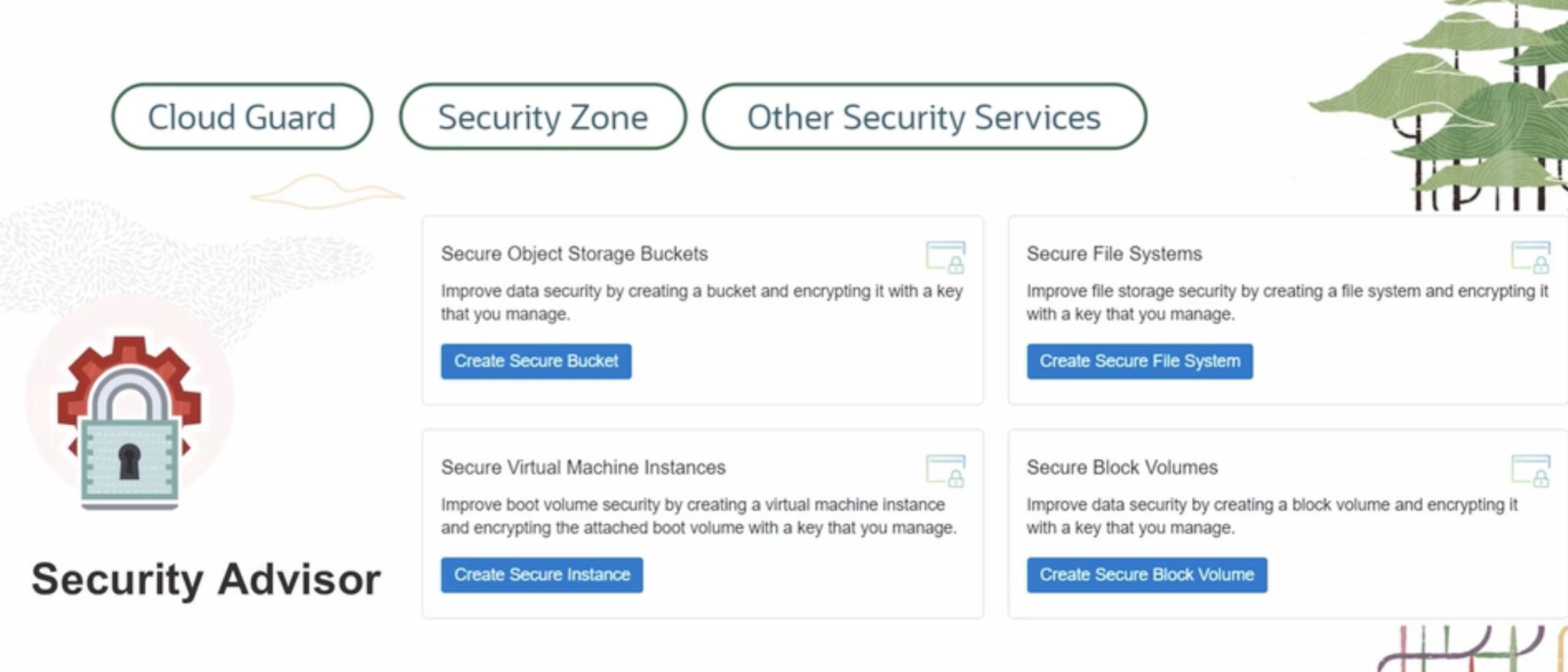
Security zone and security advisor #
Security Advisor #

Demo #
Encryption #
Symmetric Encryption #
Asymmetric key encryption #
Hardware Security #
OCI Vault #

Demo Vault #
OCR of Images #
2023-09-26_21-47-01_screenshot.png #
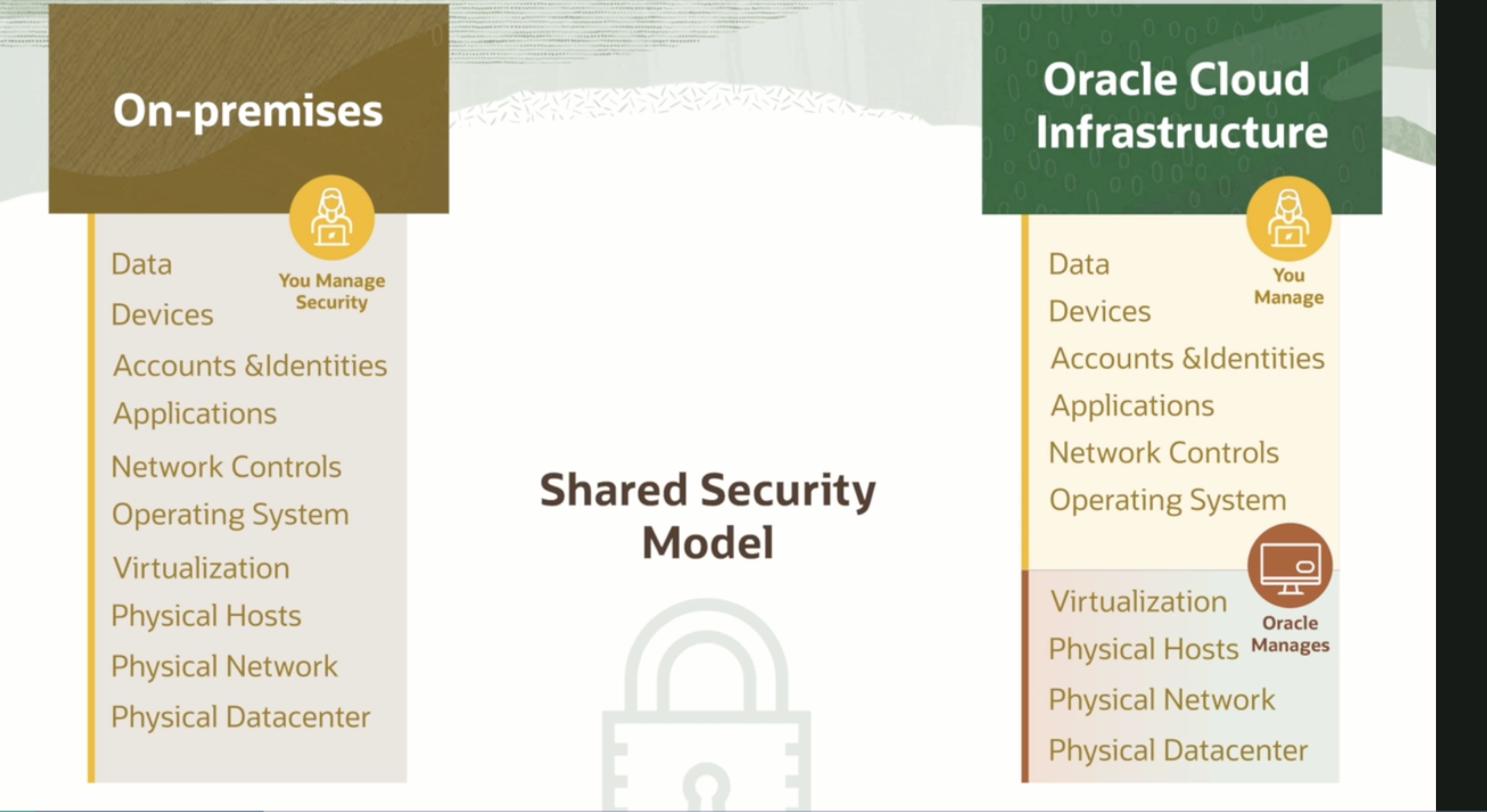
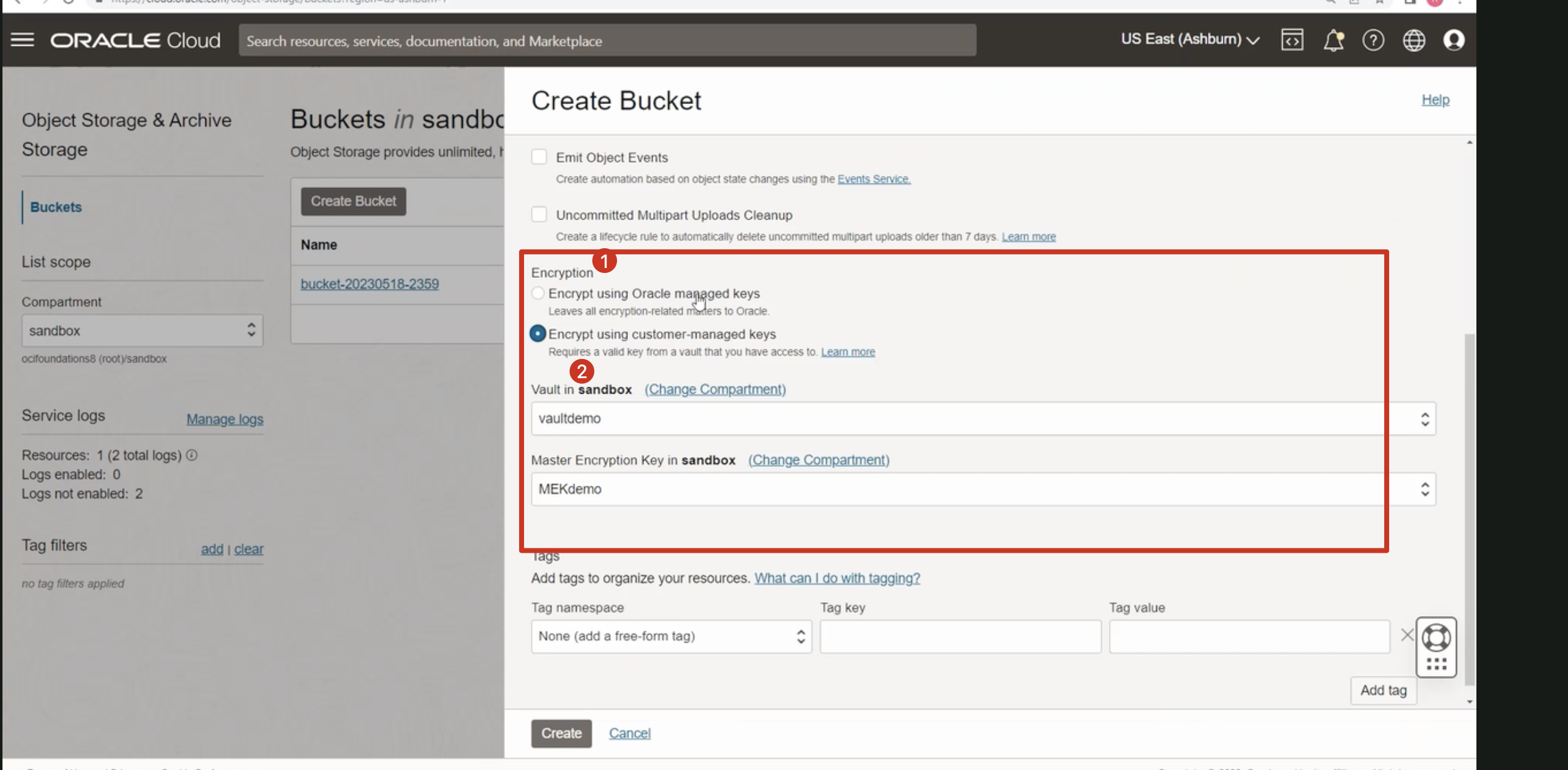
Oracle Cloud On-premises Infrastructure Data Data Devices You Manage Security You Manage Devices Accounts &ldentities Applications Accounts &ldentities Applications Network Controls Operating System Network Controls Operating System Virtualization Physical Hosts Shared Security Model O - Oracle Virtualization Physical Hosts Manages Physical Network Physical Network Physical Datacenter Physical Datacenter
2023-09-26_21-52-37_screenshot.png #
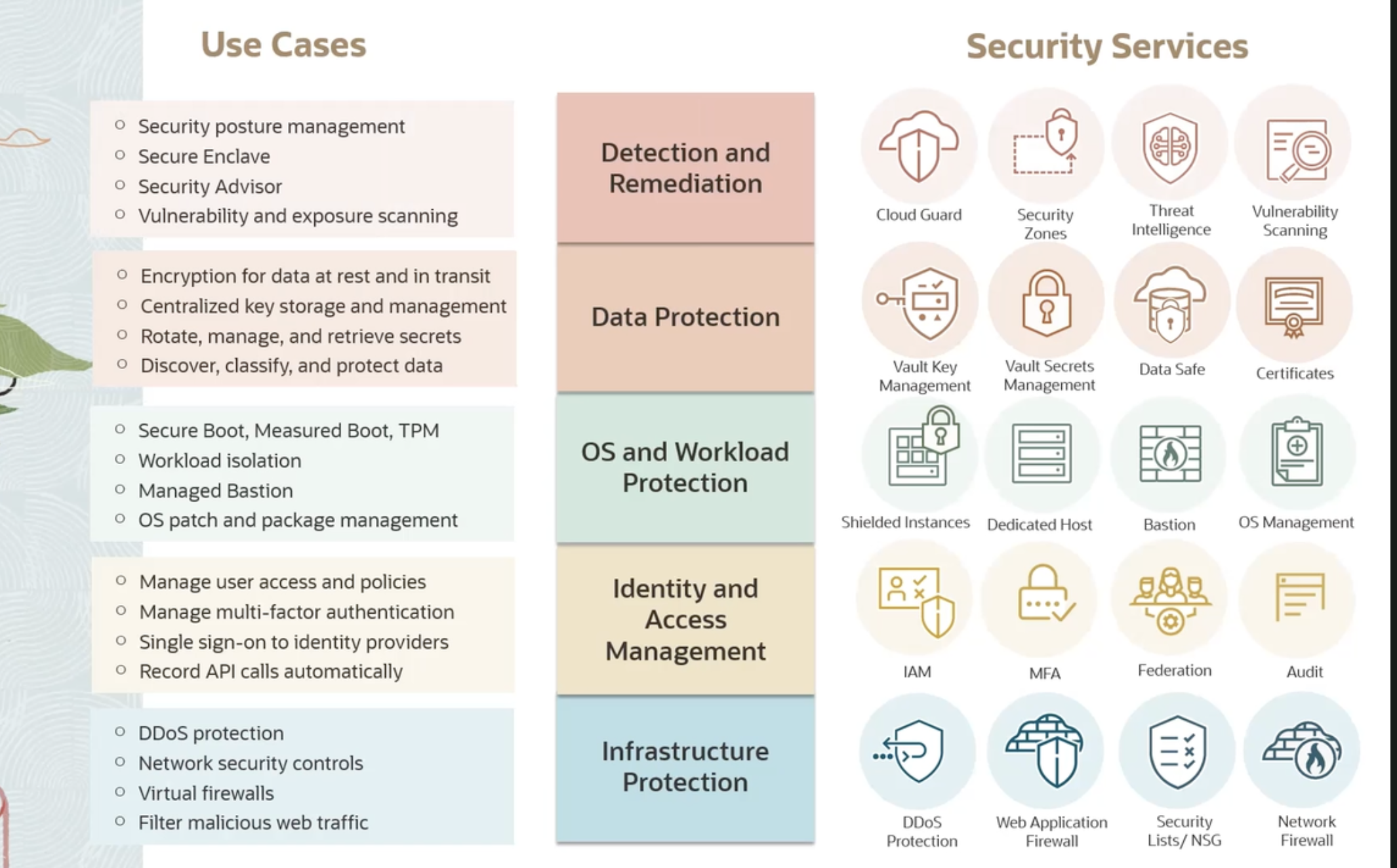
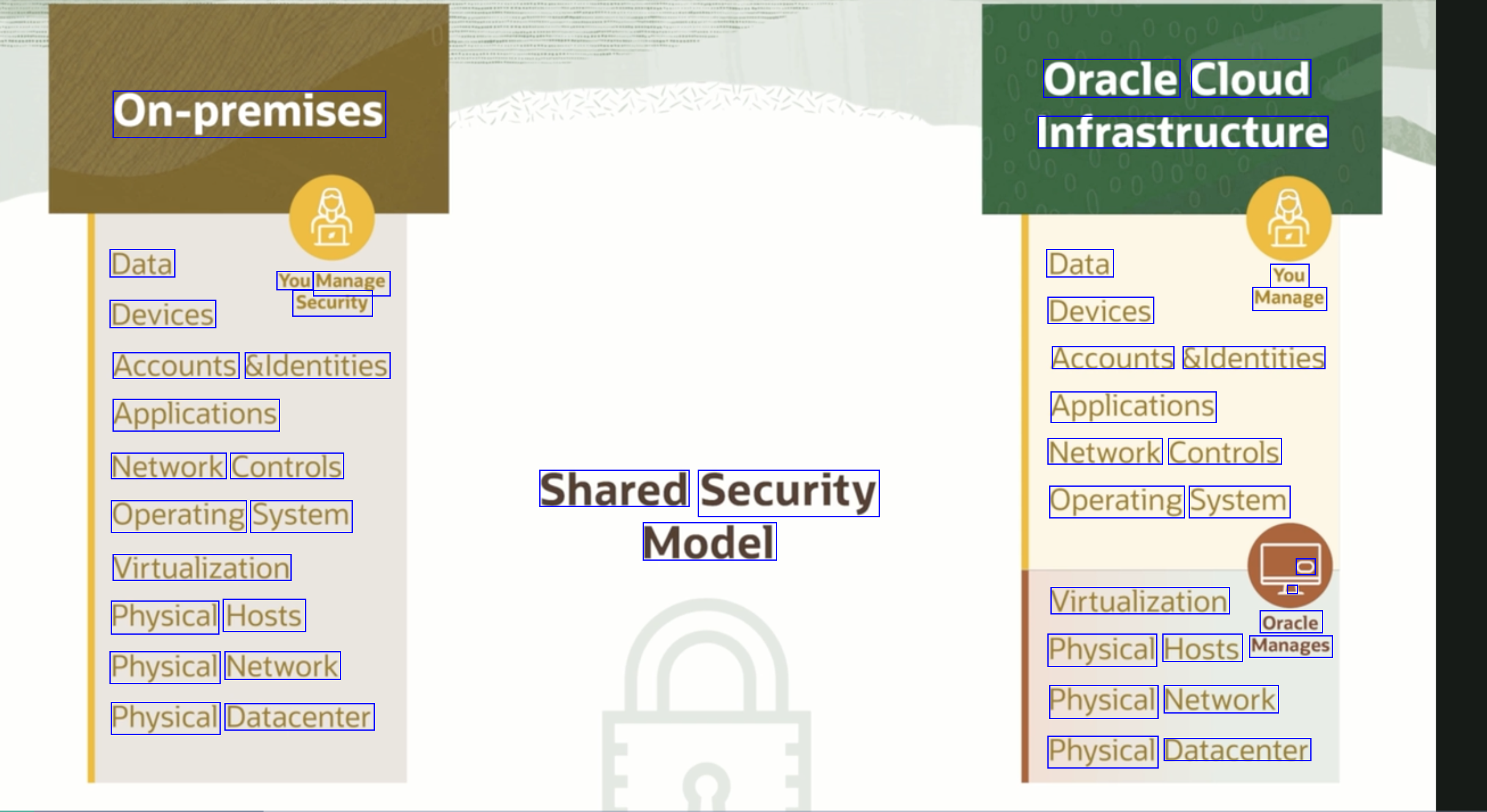
Use Cases Security Services Security posture management Secure Enclave O Security Advisor Detection and Remediation Vulnerability and exposure scanning Cloud Guard Security Zones Threat Intelligence Vulnerability Scanning O Encryption for data at rest and in transit O Centralized key storage and management Rotate, manage, and retrieve secrets Discover, classify, and protect data Data Protection Vault Key Vault Secrets Data Safe Certificates Management Management Secure Boot, Measured Boot, TPM Workload isolation o Managed Bastion OS and Workload Protection O OS patch and package management Shielded Instances Dedicated Host Bastion OS Management Manage user access and policies Manage multi-factor authentication Single sign-on to identity providers Record API calls automatically Identity and Access Management 88 IAM MFA Federation Audit DDOS protection o Network security controls Virtual firewalls O Filter malicious web traffic Infrastructure Protection DDOS Protection Web Application Security Firewall Network Firewall Lists/NSG
2023-09-26_21-53-30_screenshot.png #
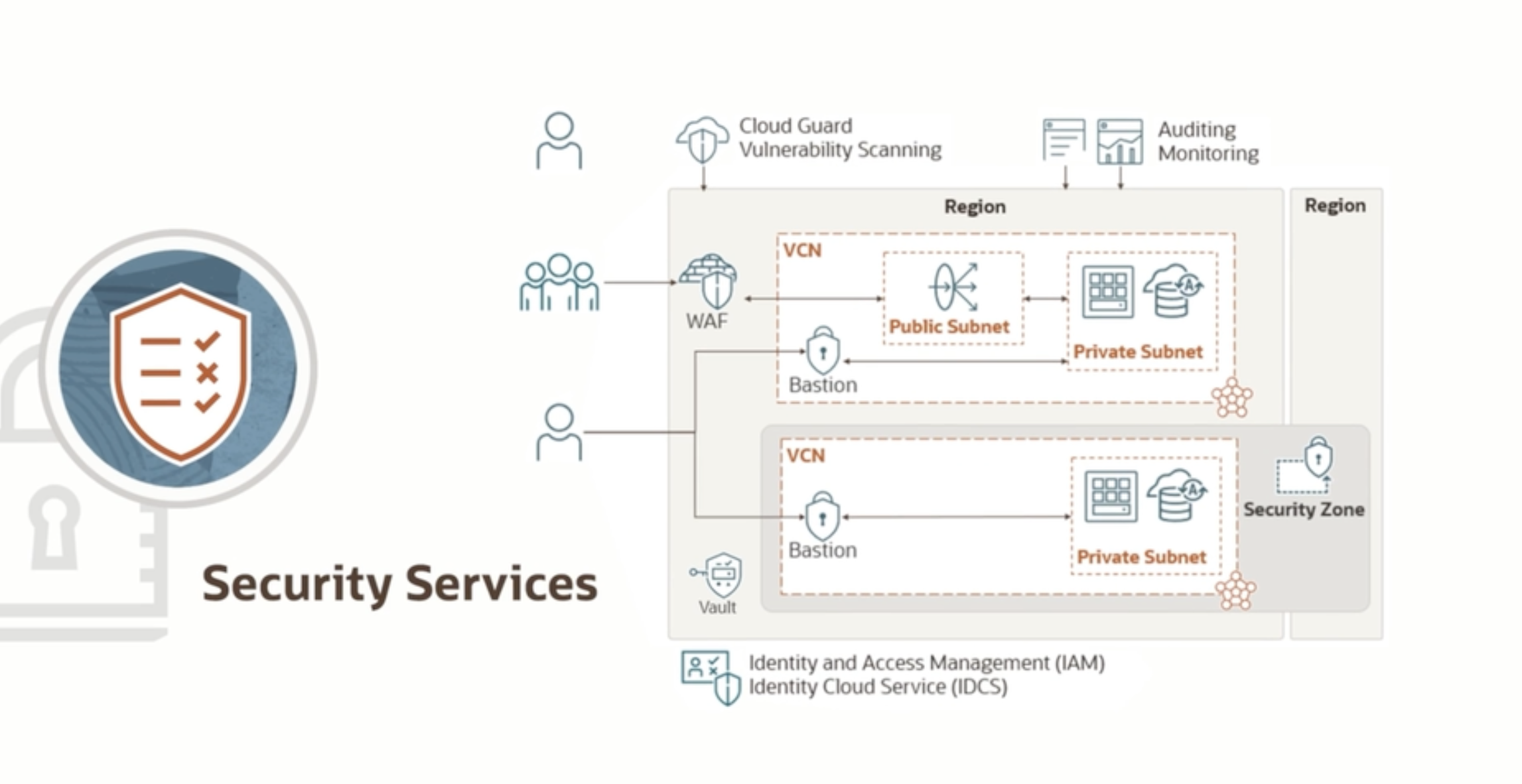
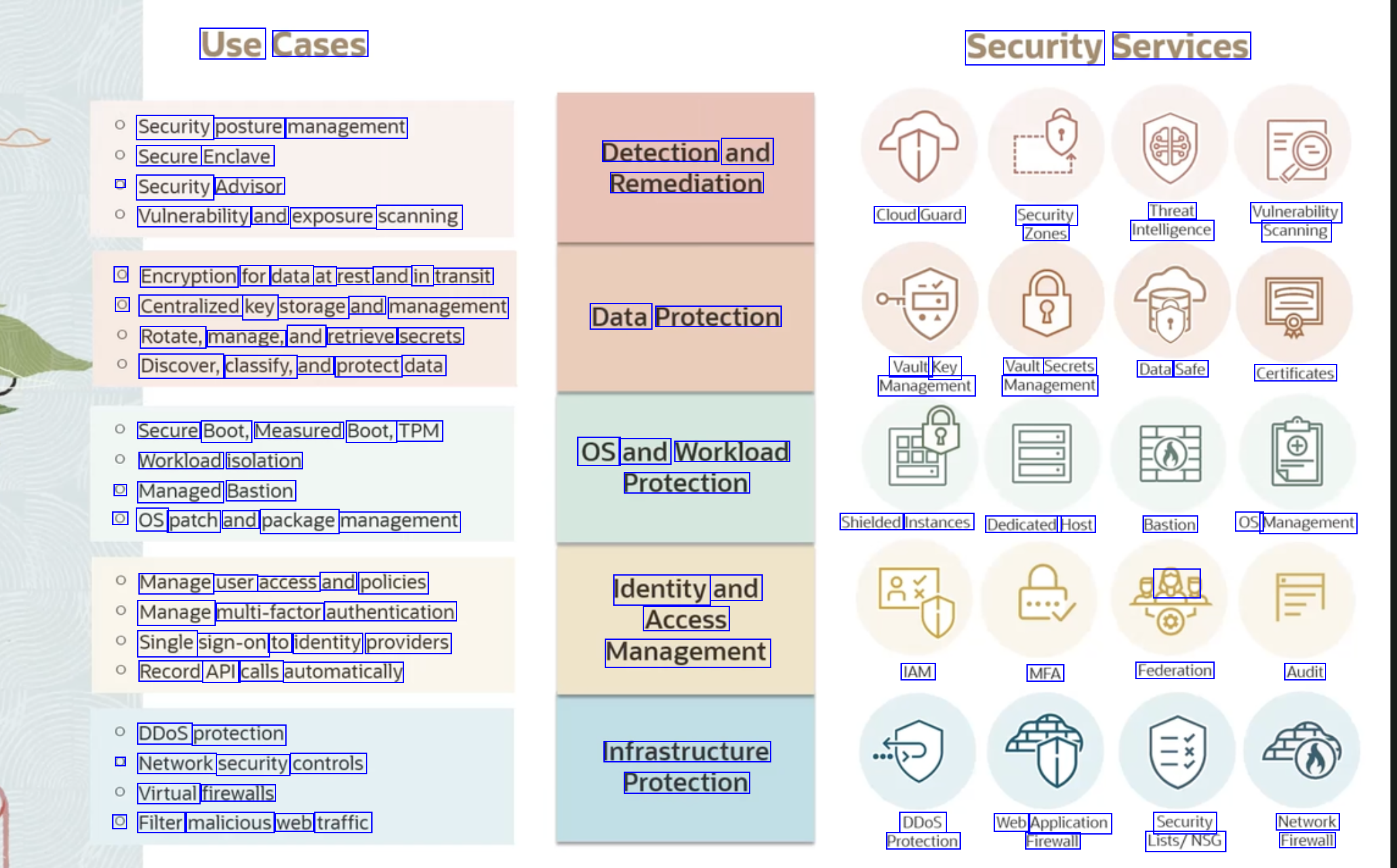
Cloud Guard Vulnerability Scanning Auditing Monitoring Region Region VCN % WAF Public Subnet Private Subnet Bastion - - - - E VCN Security Zone Bastion Private Subnet Security Services Vault Identity and Access Management (IAM) Identity Cloud Service (IDCS)
2023-09-26_21-55-48_screenshot.png #
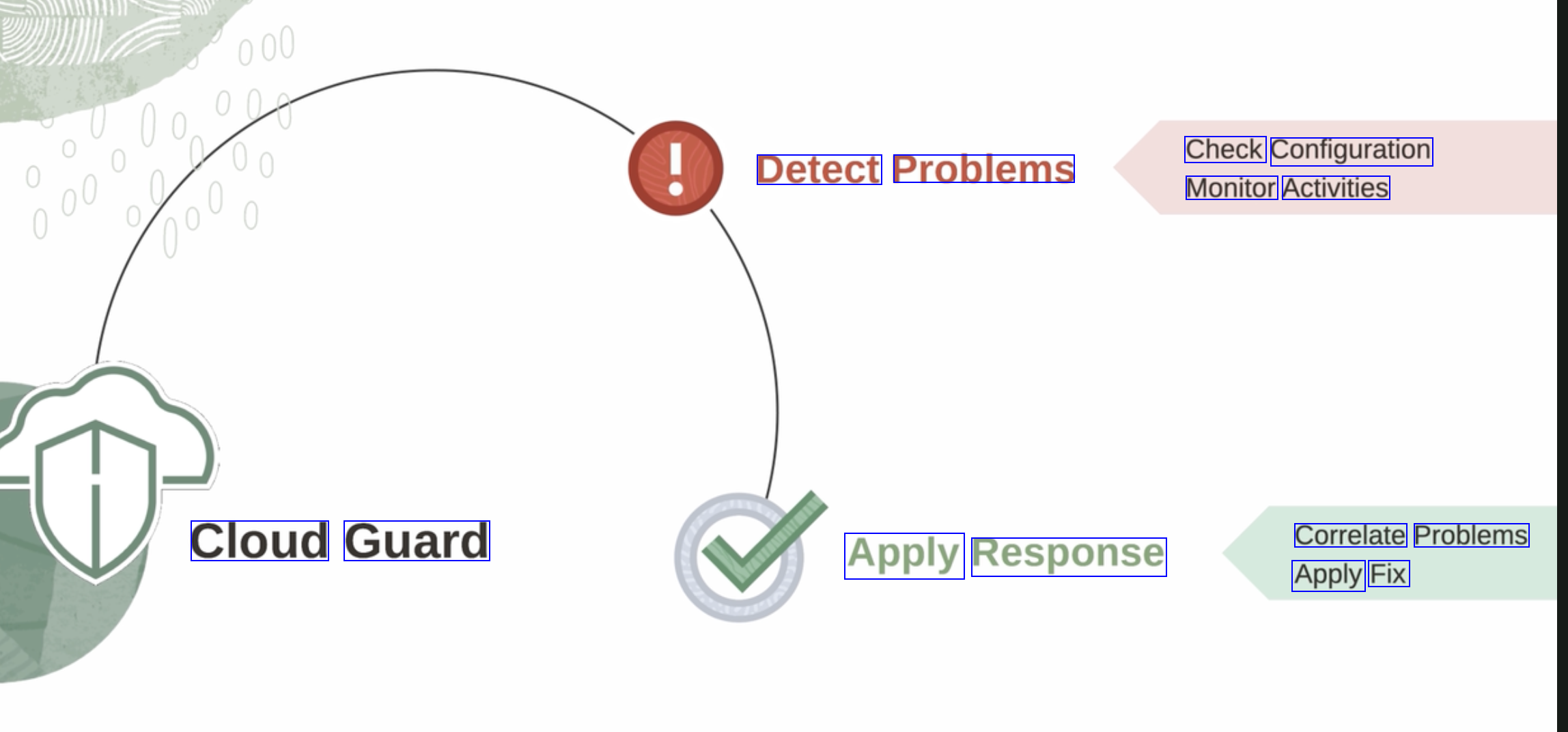
Check Configuration Monitor Activities Detect Problems Cloud Guard Correlate Problems Apply Fix Apply Response
2023-09-26_21-56-28_screenshot.png #
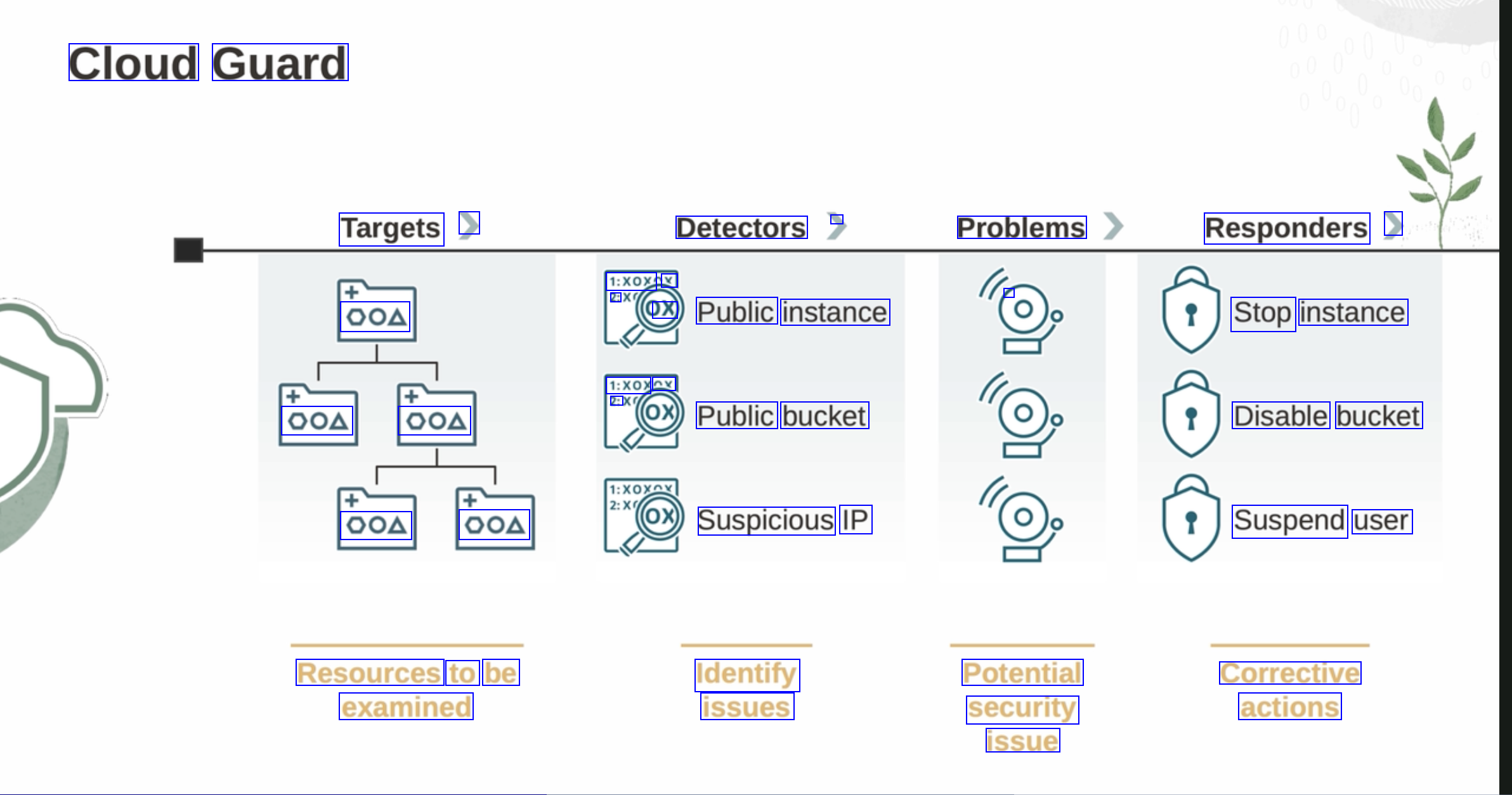
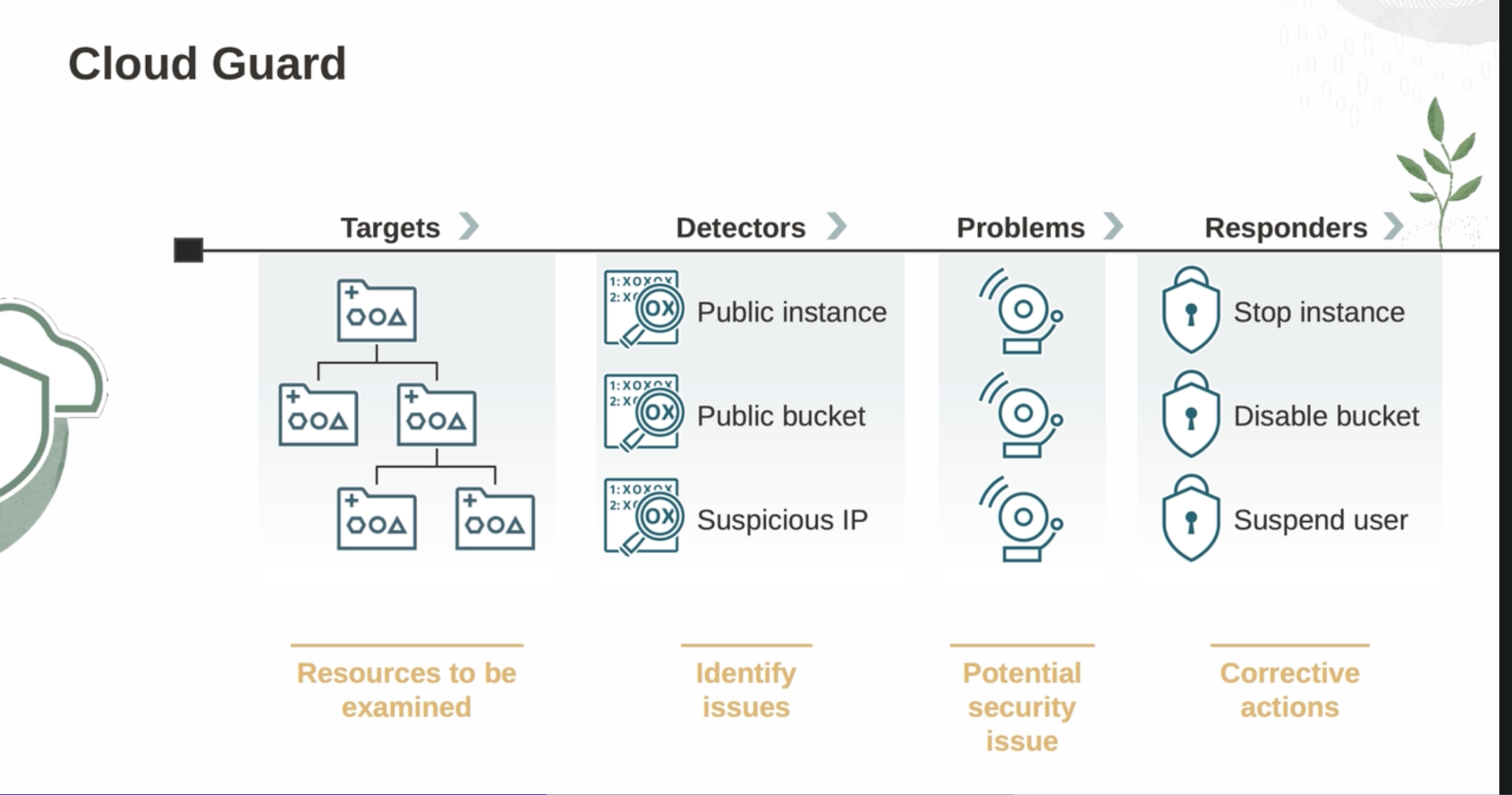
Cloud Guard Targets > Detectors - Problems Responders > 1:XOX 2: x - OOA OX Public instance Stop instance 1:XOX Ay 2: OOA OOA Public bucket Disable bucket OOA OOA Suspicious IP Suspend user Resources to be examined Identify issues Potential security issue Corrective actions
2023-09-26_21-57-57_screenshot.png #
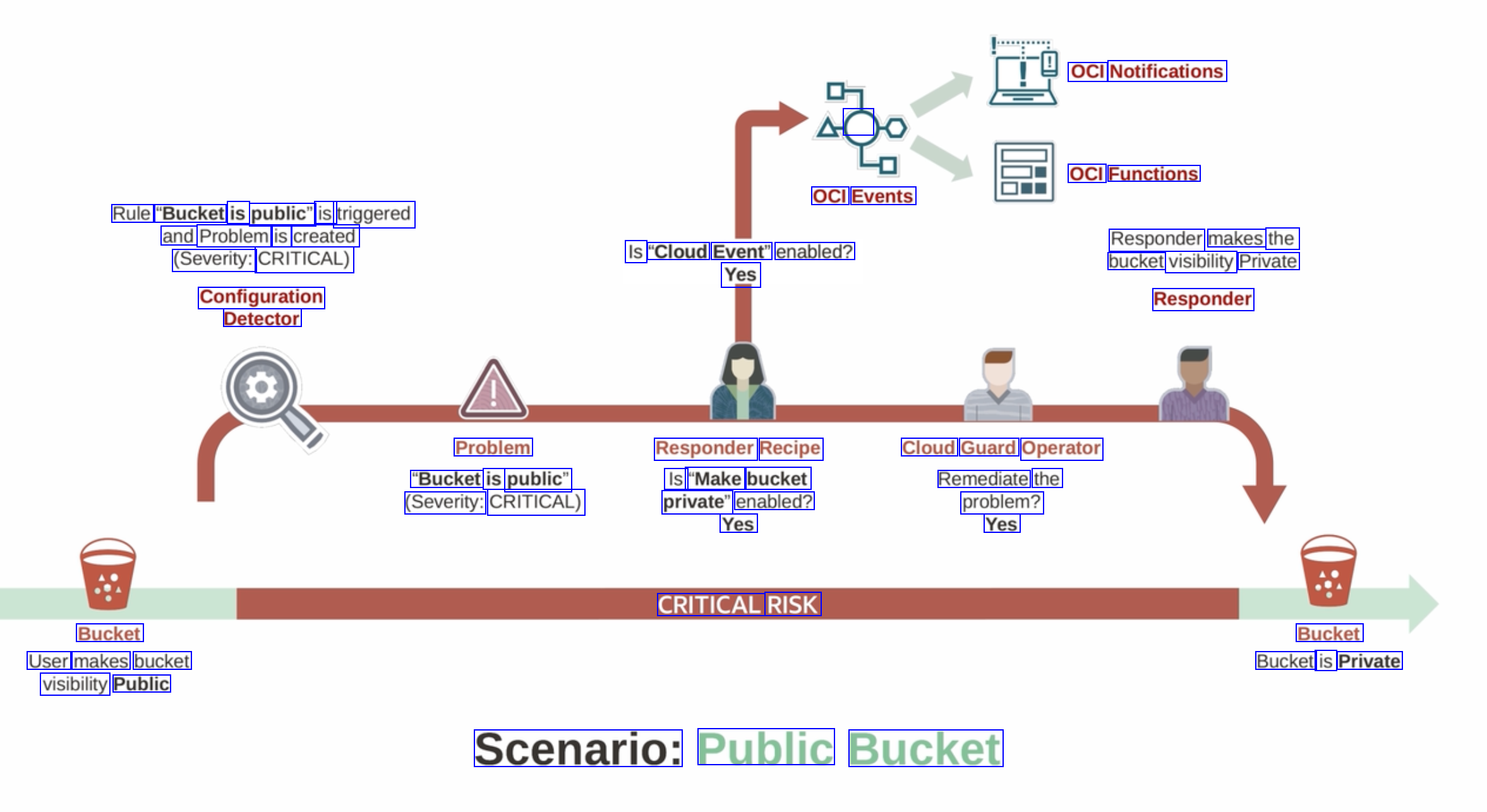
OCI Notifications C OCI Functions OCI Events Rule "Bucket is public" is triggered and Problem is created (Severity: CRITICAL) Configuration Detector Responder makes the bucket visibility Private Responder Is "Cloud Event" enabled? Yes Problem "Bucket is public" (Severity: CRITICAL) Responder Recipe Is "Make bucket private" enabled? Yes Cloud Guard Operator Remediate the problem? Yes CRITICAL RISK Bucket User makes bucket visibility Public Bucket Bucket is Private Scenario: Public Bucket
2023-09-26_21-59-29_screenshot.png #
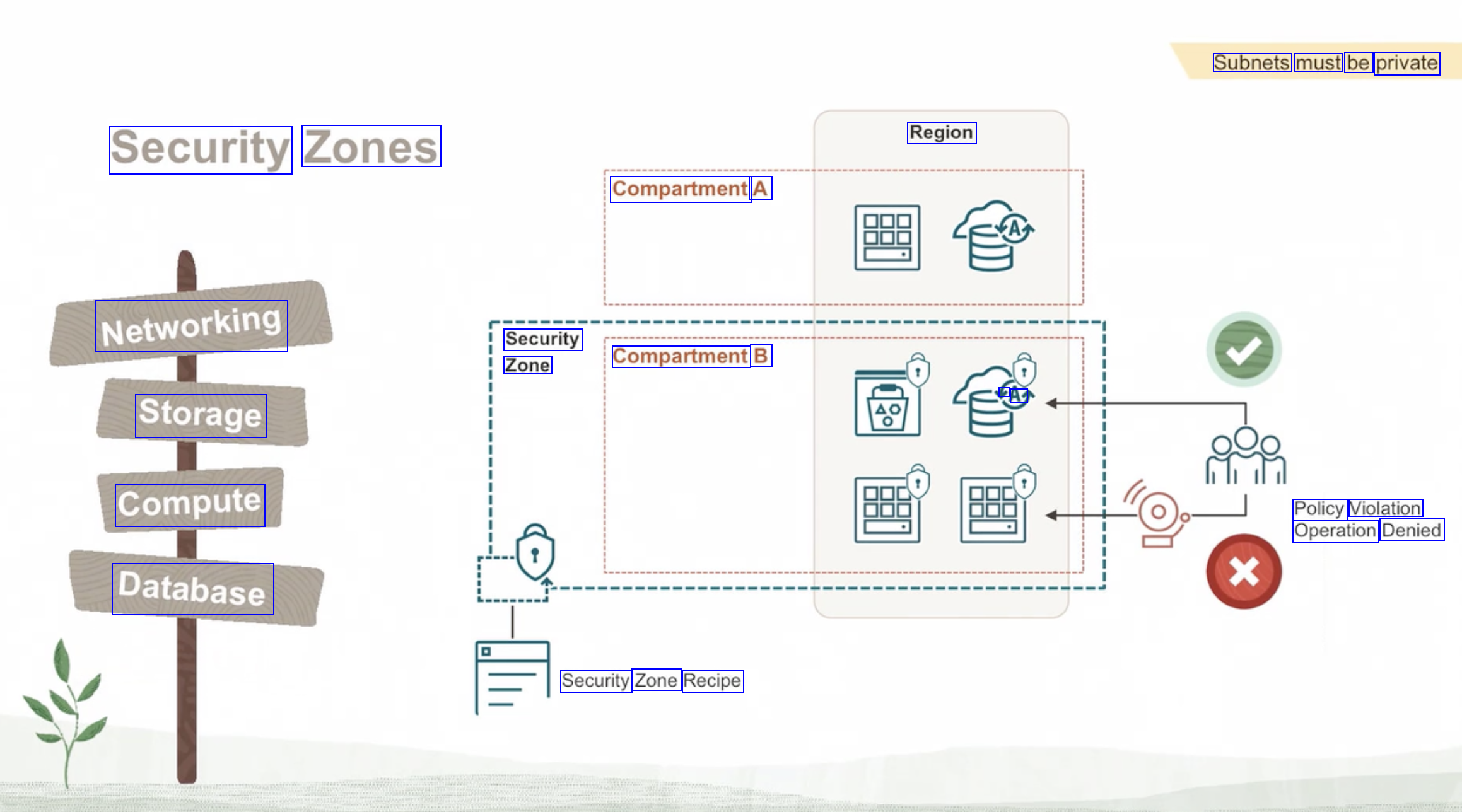
Subnets must be private Region Security Zones Compartment A Networking Security Zone Compartment B AY Storage Compute Policy Violation Operation Denied Database Security Zone Recipe
2023-09-26_22-00-42_screenshot.png #
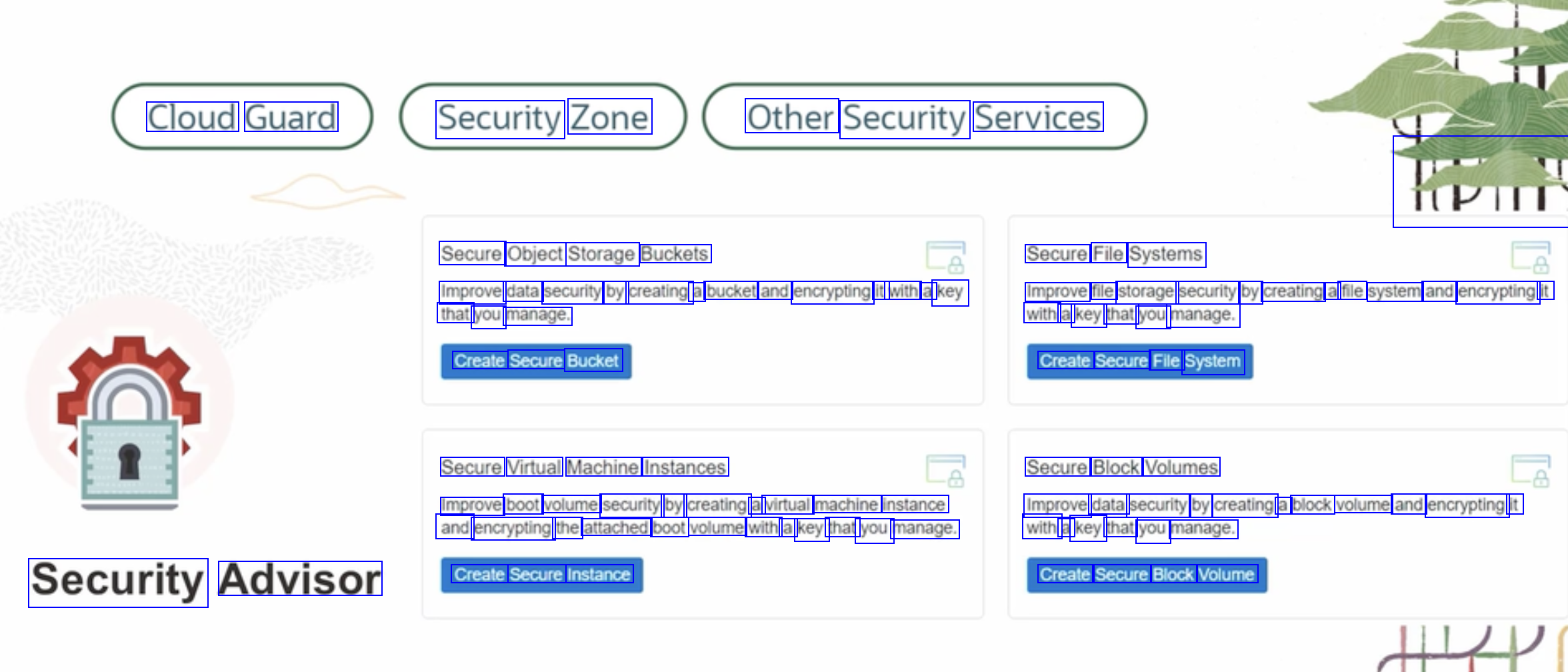
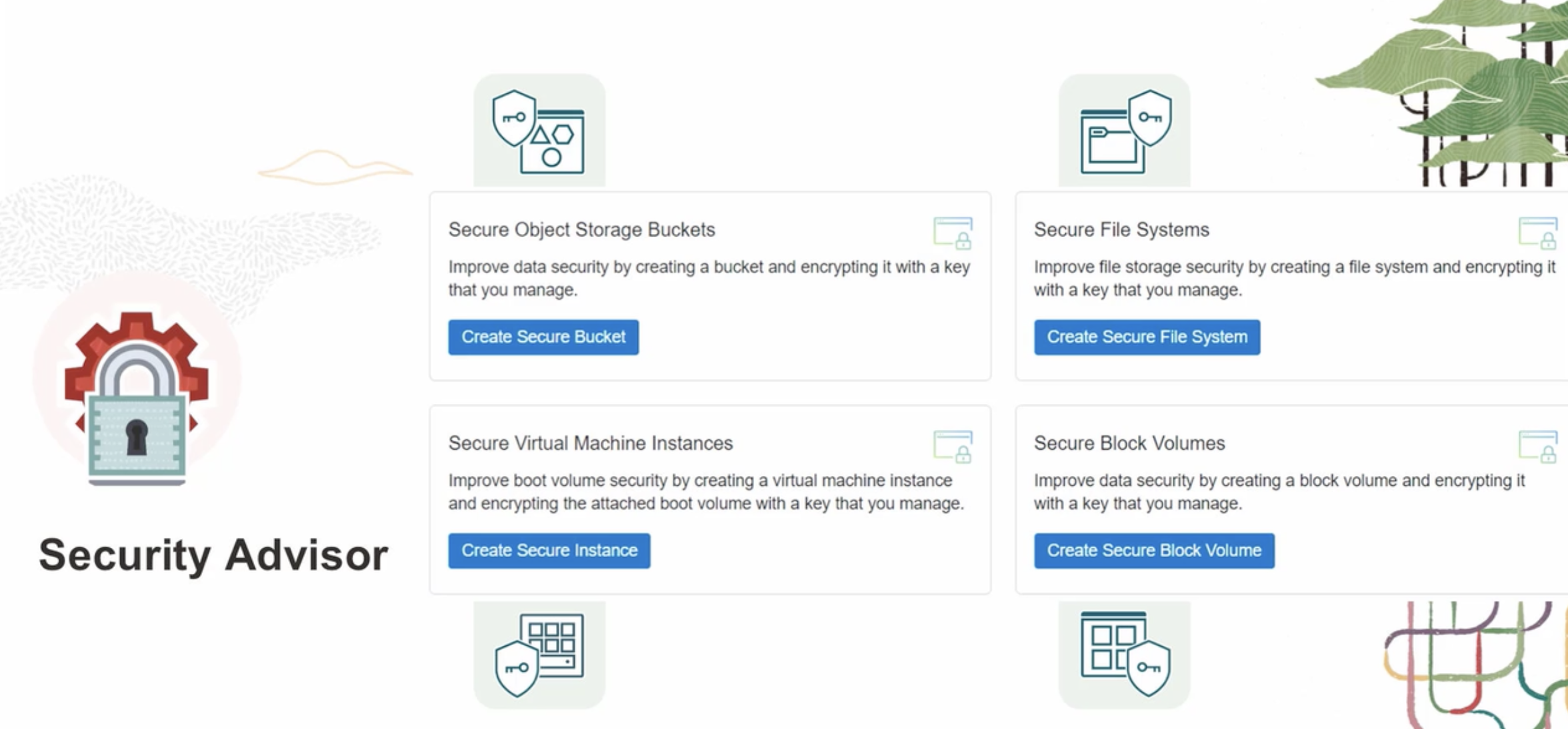
Cloud Guard Security Zone Other Security Services HPT Secure Object Storage Buckets Secure File Systems Improve data security by creating a bucket and encrypting it with a key Improve file storage security by creating a file system and encrypting it that you manage. with a key that you manage. Create Secure Bucket Create Secure File System Secure Virtual Machine Instances Secure Block Volumes Improve boot volume security by creating a virtual machine instance and encrypting the attached boot volume with a key that you manage. Improve data security by creating a block volume and encrypting it with a key that you manage. Security Advisor Create Secure Instance Create Secure Block Volume
2023-09-26_22-01-11_screenshot.png #

rO C On Hemt Secure Object Storage Buckets Secure File Systems Improve data security by creating a bucket and encrypting it with a key Improve file storage security by creating a file system and encrypting it that you manage. with a key that you manage. Create Secure Bucket Create Secure File System a Secure Virtual Machine Instances Secure Block Volumes la Improve boot volume security by creating a virtual machine instance and encrypting the attached boot volume with a key that you manage. Improve data security by creating a block volume and encrypting it with a key that you manage. Security Advisor Create Secure Instance Create Secure Block Volume On
2023-09-26_22-01-27_screenshot.png #

To wrap up... Security Zone Cannot disable security Security Advisor Security Zone Cloud Guard Other security services
2023-09-26_22-01-51_screenshot.png #
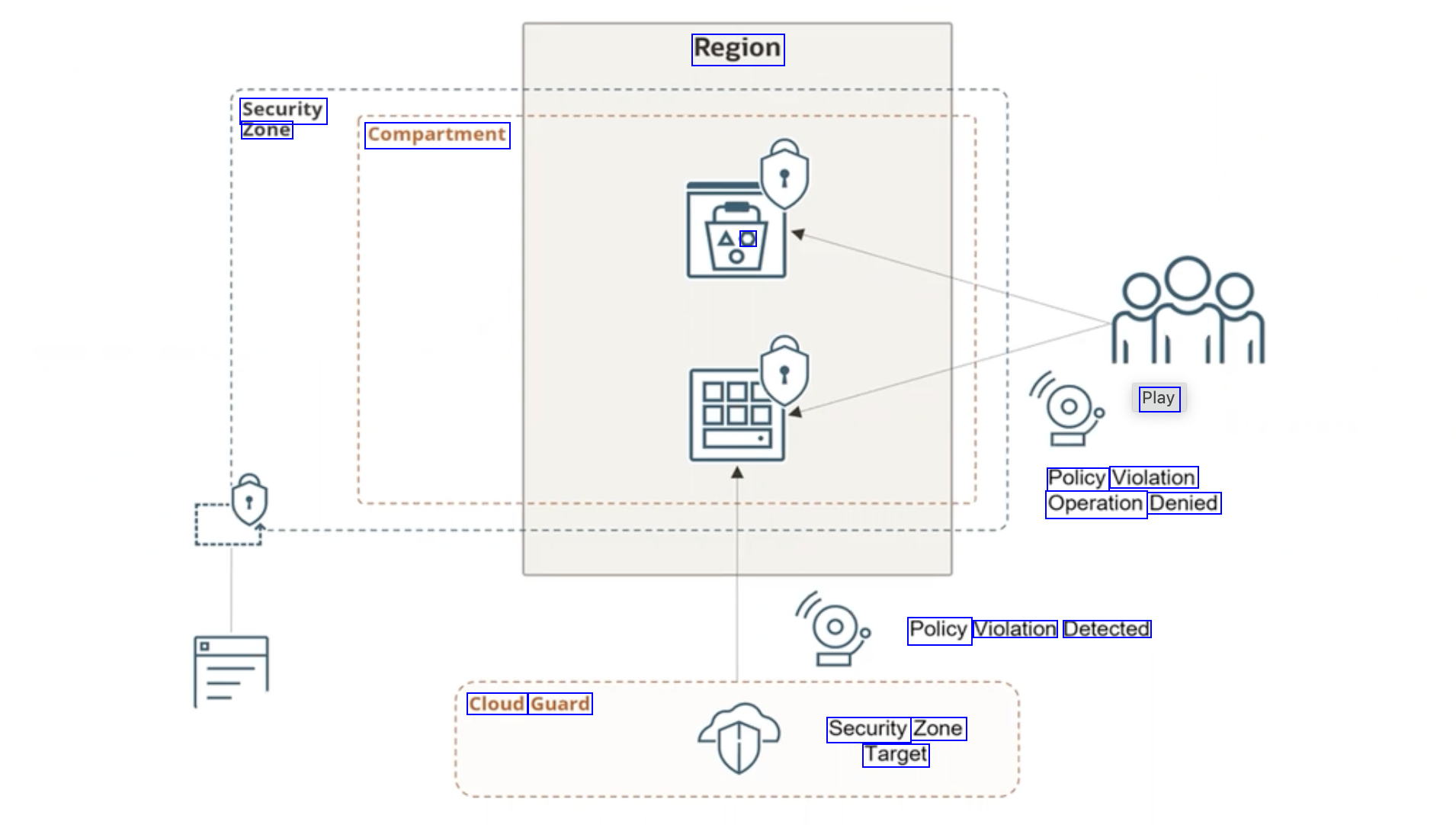
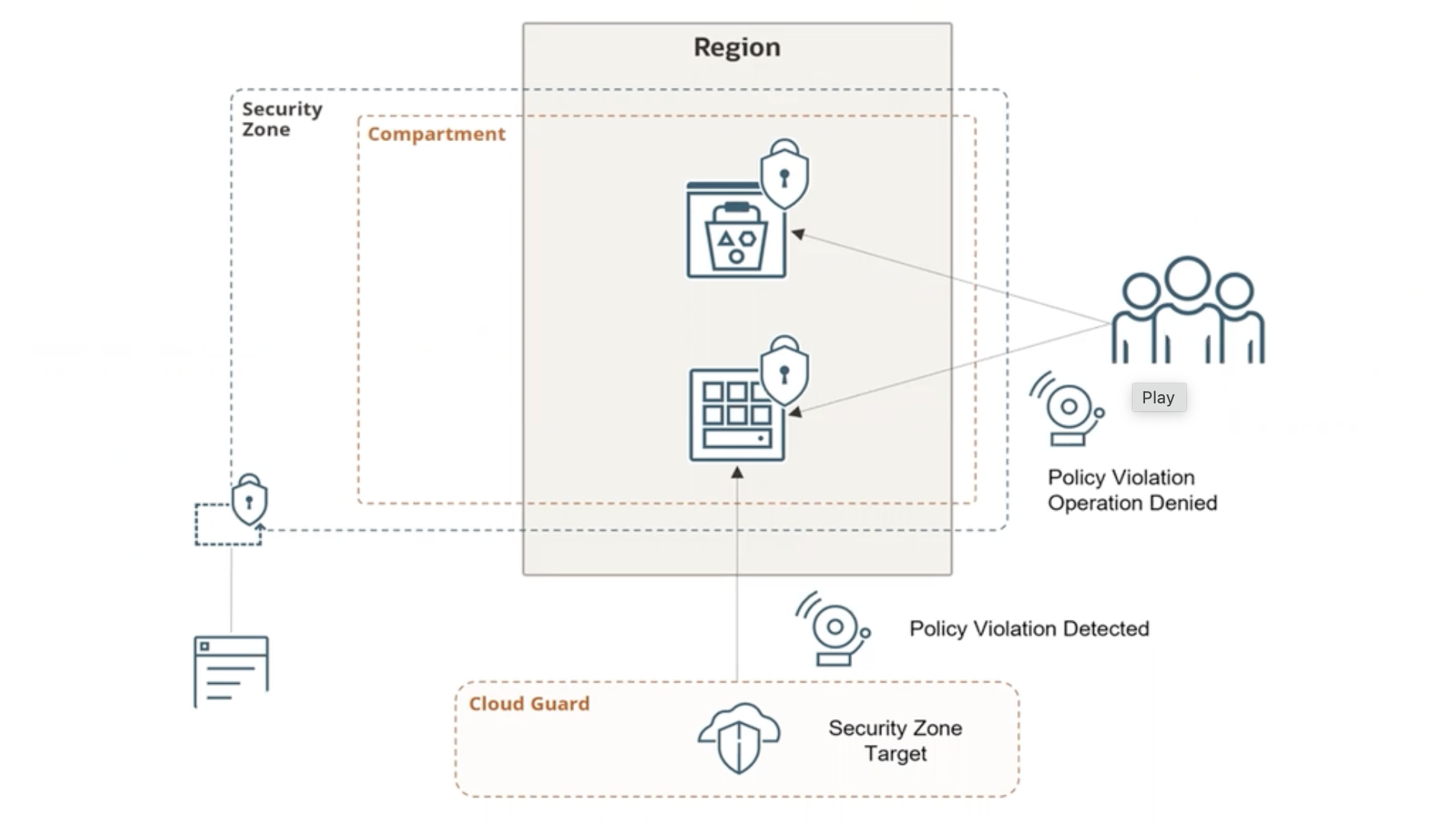
Region Security Zone Compartment O Play Policy Violation Operation Denied Policy Violation Detected Cloud Guard Security Zone Target
2023-09-26_22-06-37_screenshot.png #
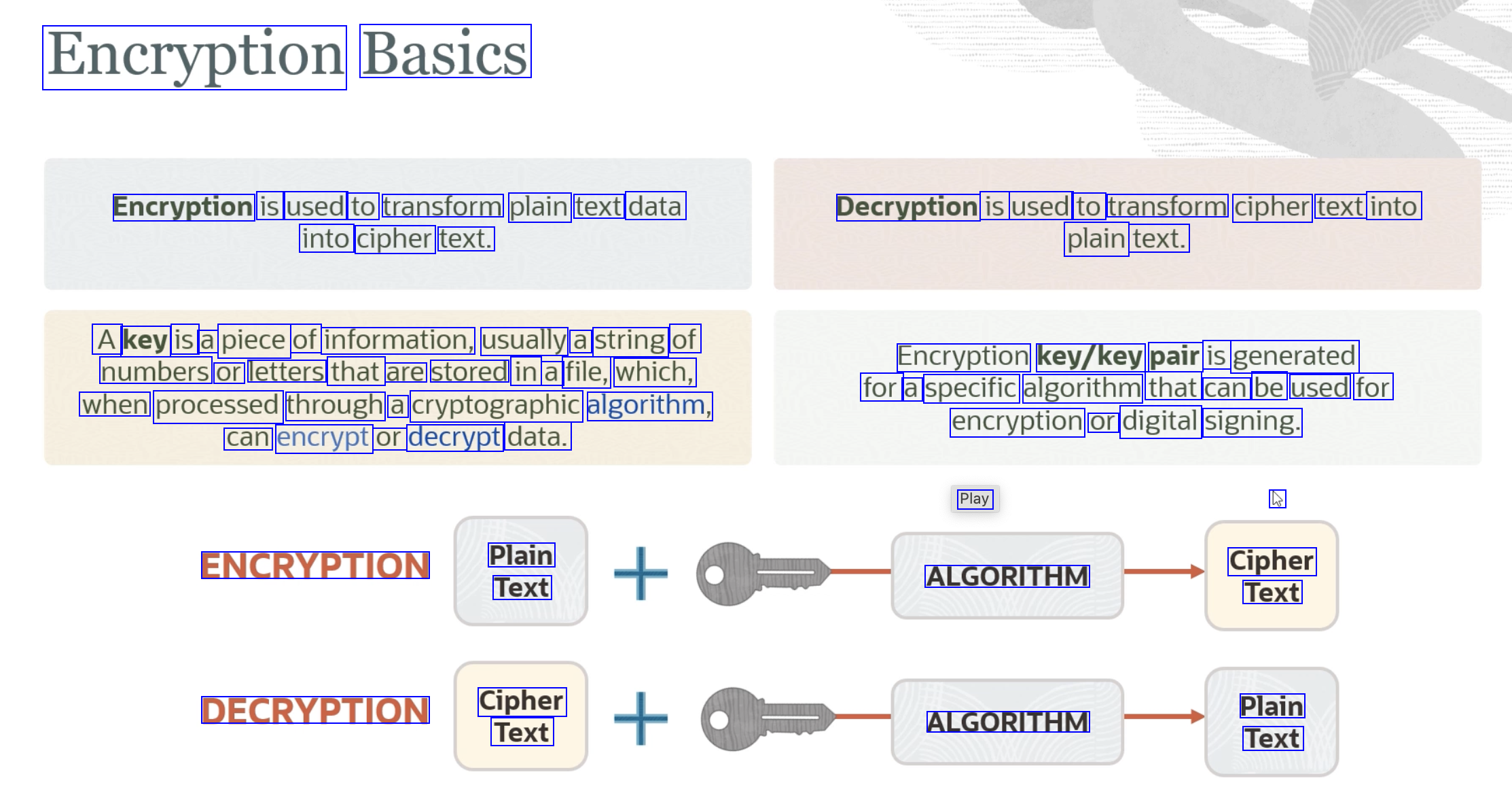
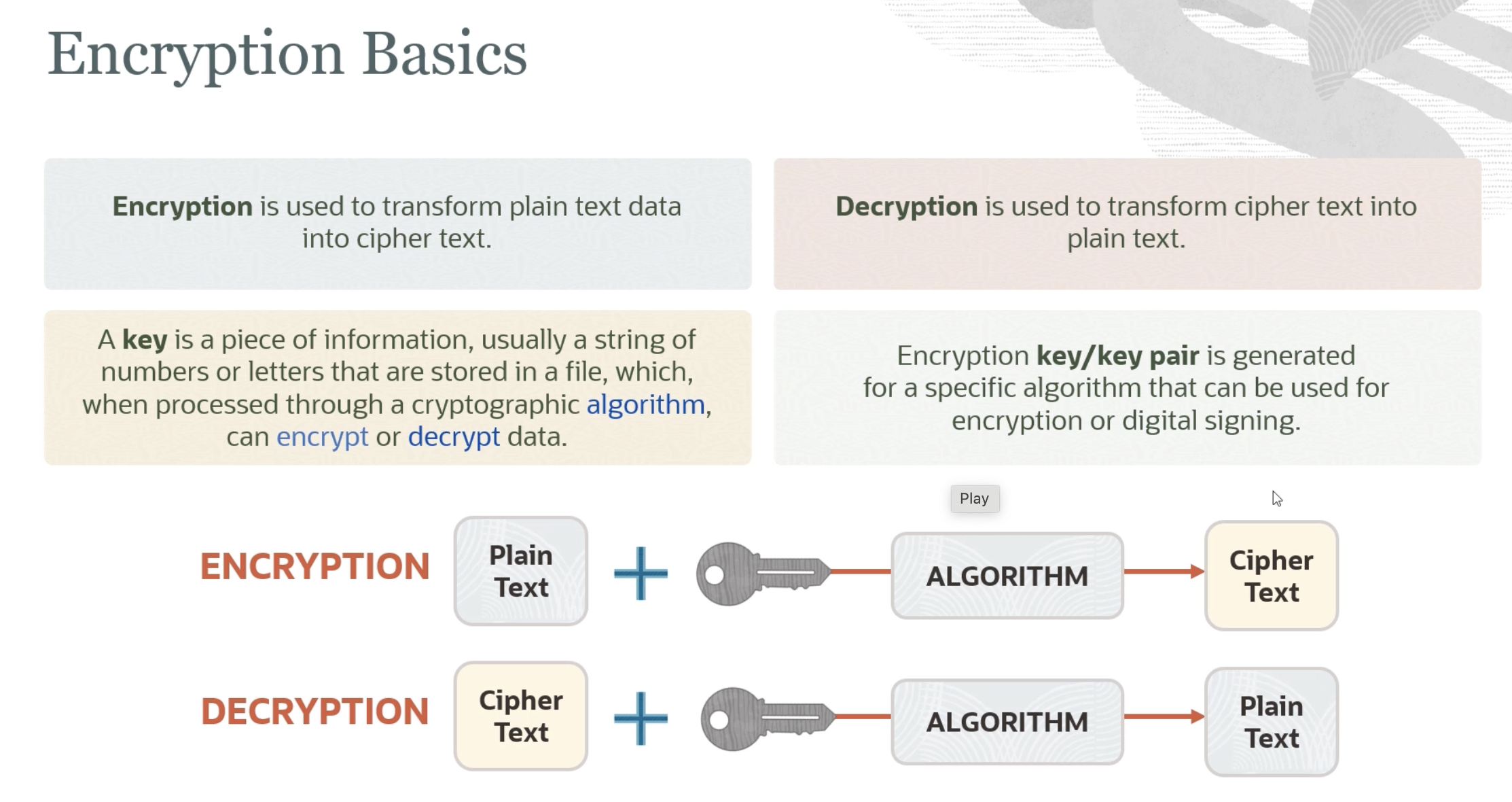
Encryption Basics Encryption is used to transform plain text data Decryption is used to transform cipher text into into cipher text. plain text. A key is a piece of information, usually a string of numbers or letters that are stored in a file, which, when processed through a cryptographic algorithm, Encryption key/key pair is generated for a specific algorithm that can be used for encryption or digital signing. can encrypt or decrypt data. Play Ce ENCRYPTION Plain Text Cipher Text ALGORITHM DECRYPTION Cipher Plain Text Text ALGORITHM
2023-09-26_22-07-42_screenshot.png #
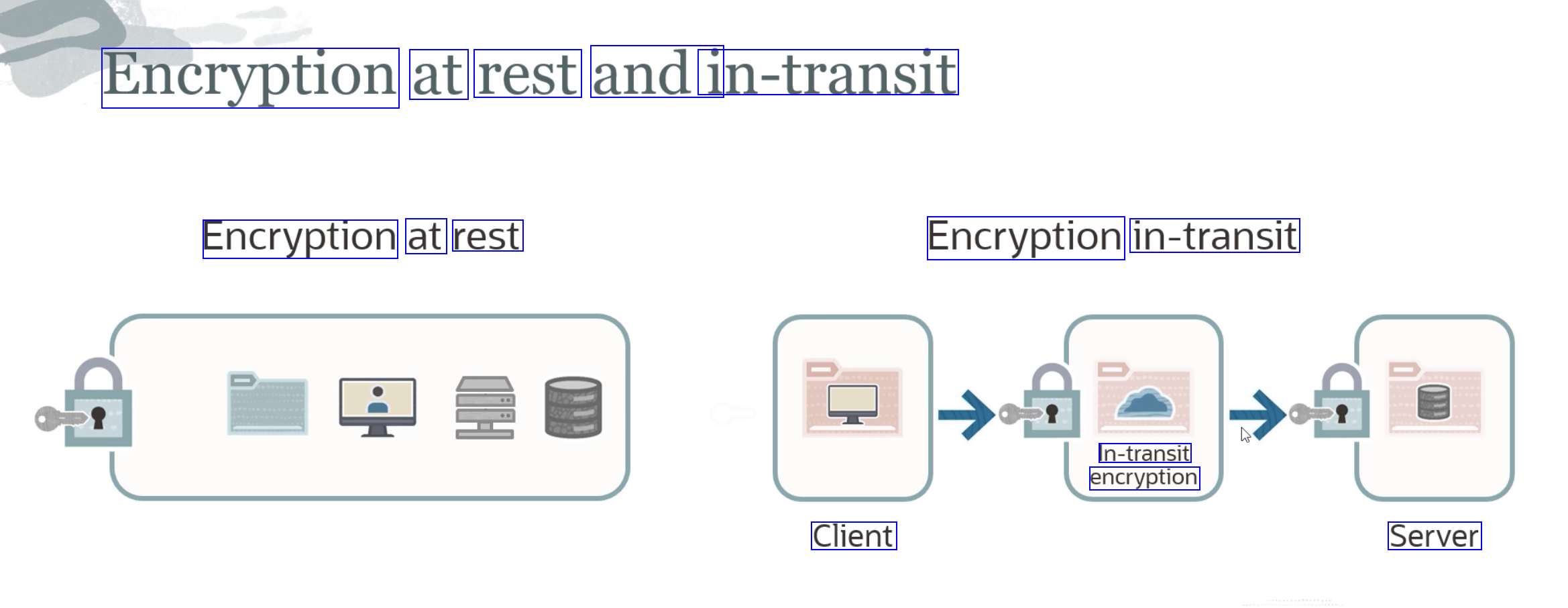
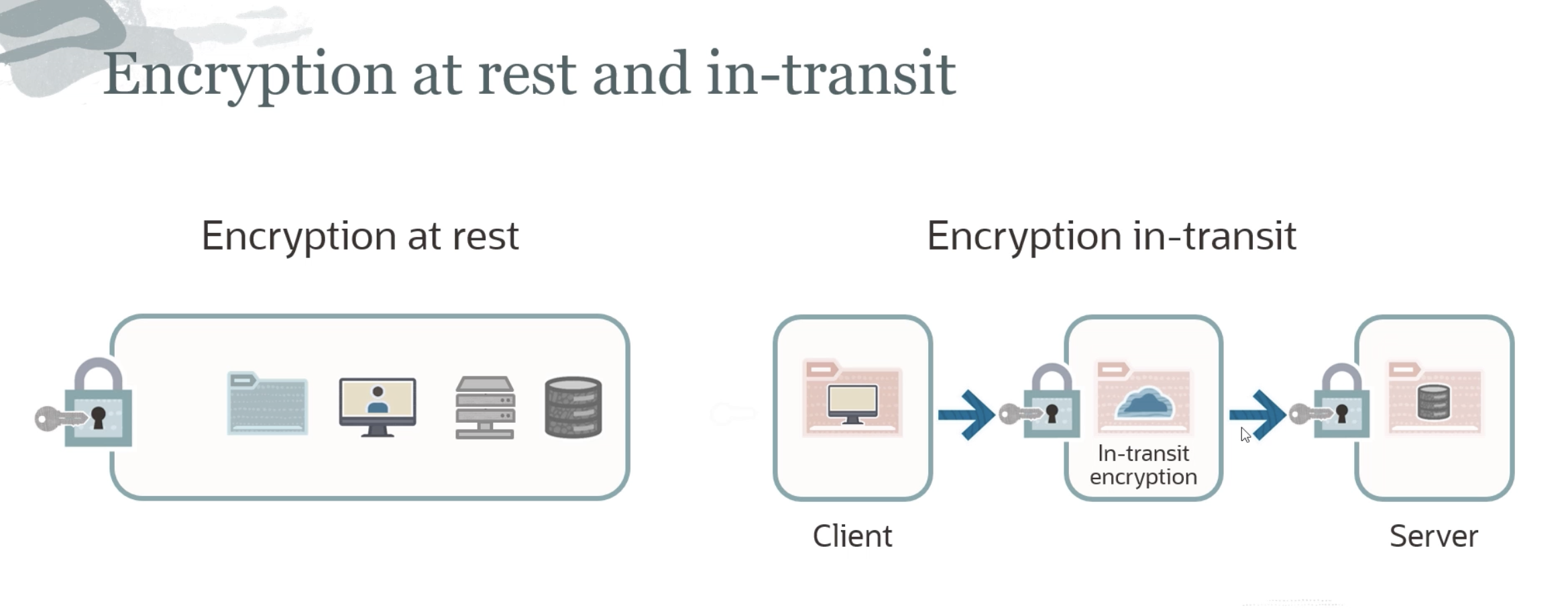
Encryption at rest andi in-transit Encryption at rest Encryption in-transit In-transit encryption Client Server
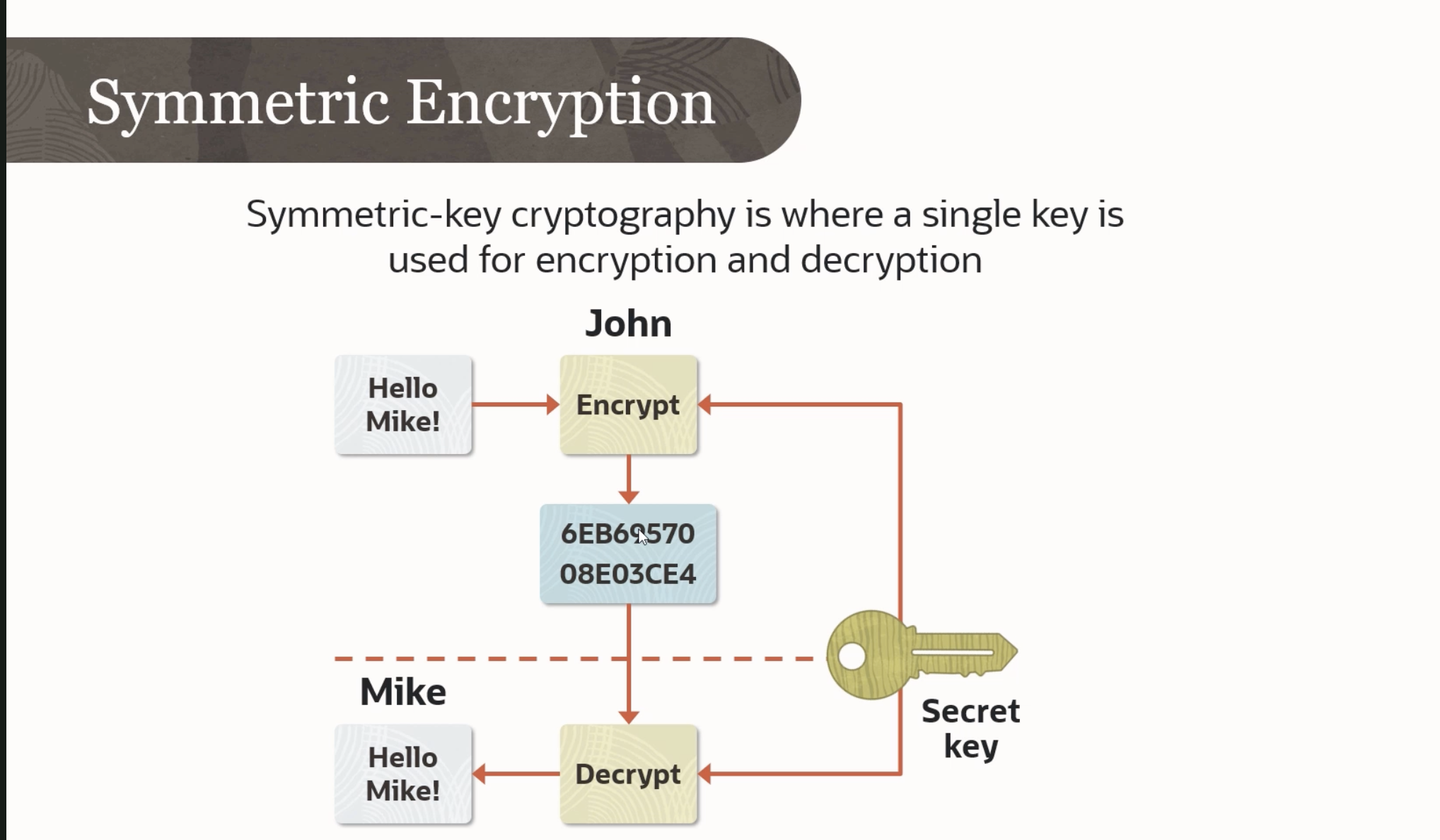
2023-09-26_22-08-28_screenshot.png #
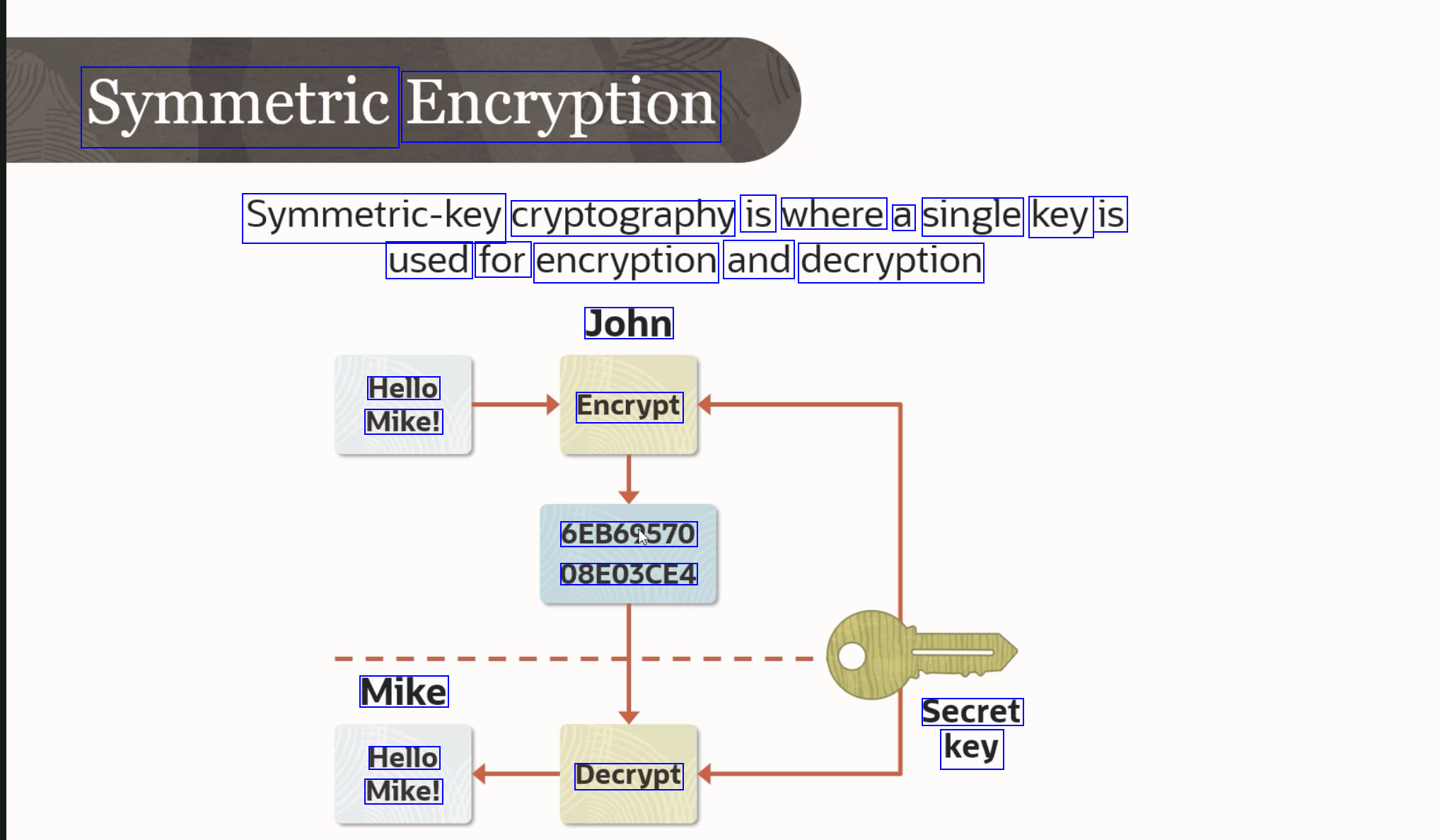
Symmetric Encryption Symmetric-key cryptography is where a single key is used for encryption and decryption John Hello Mike! Encrypt 6EB69570 08E03CE4 Mike Secret key Hello Mike! Decrypt
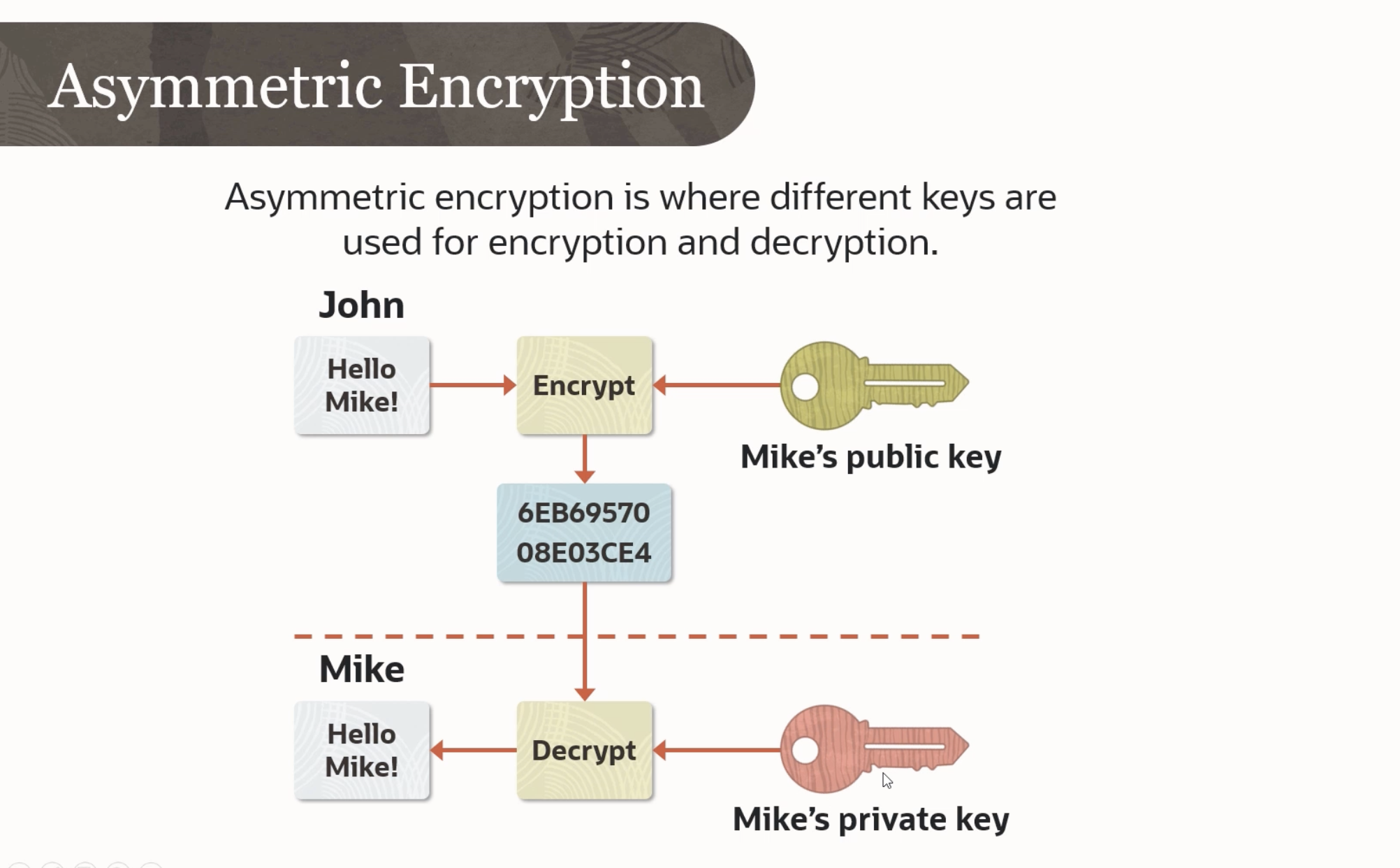
2023-09-26_22-09-07_screenshot.png #
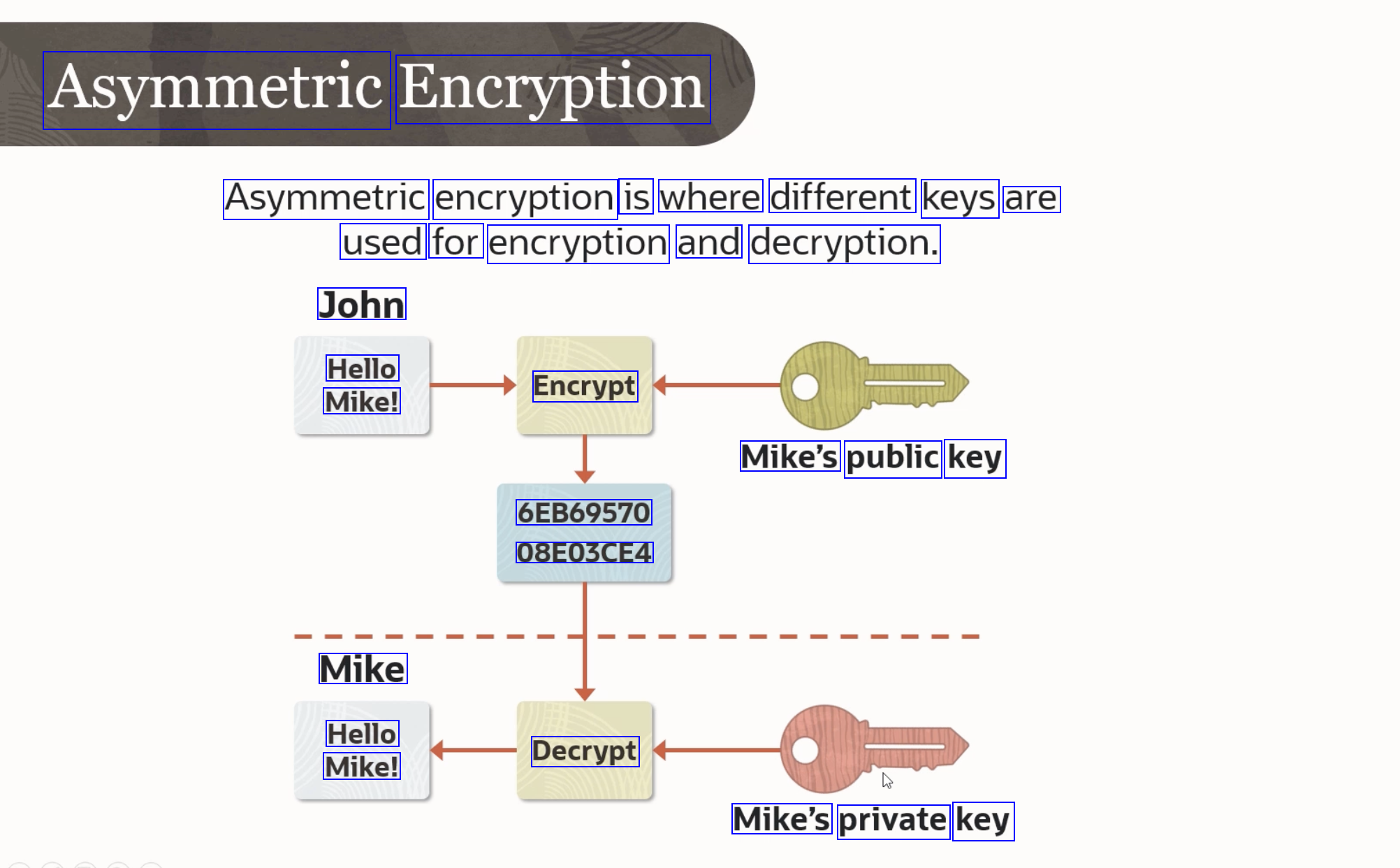
Asymmetric Encryption Asymmetric encryption is where different keys are used for encryption and decryption. John Hello Mike! Encrypt Mike's public key 6EB69570 08E03CE4 Mike Hello Mike! Decrypt Mike's private key
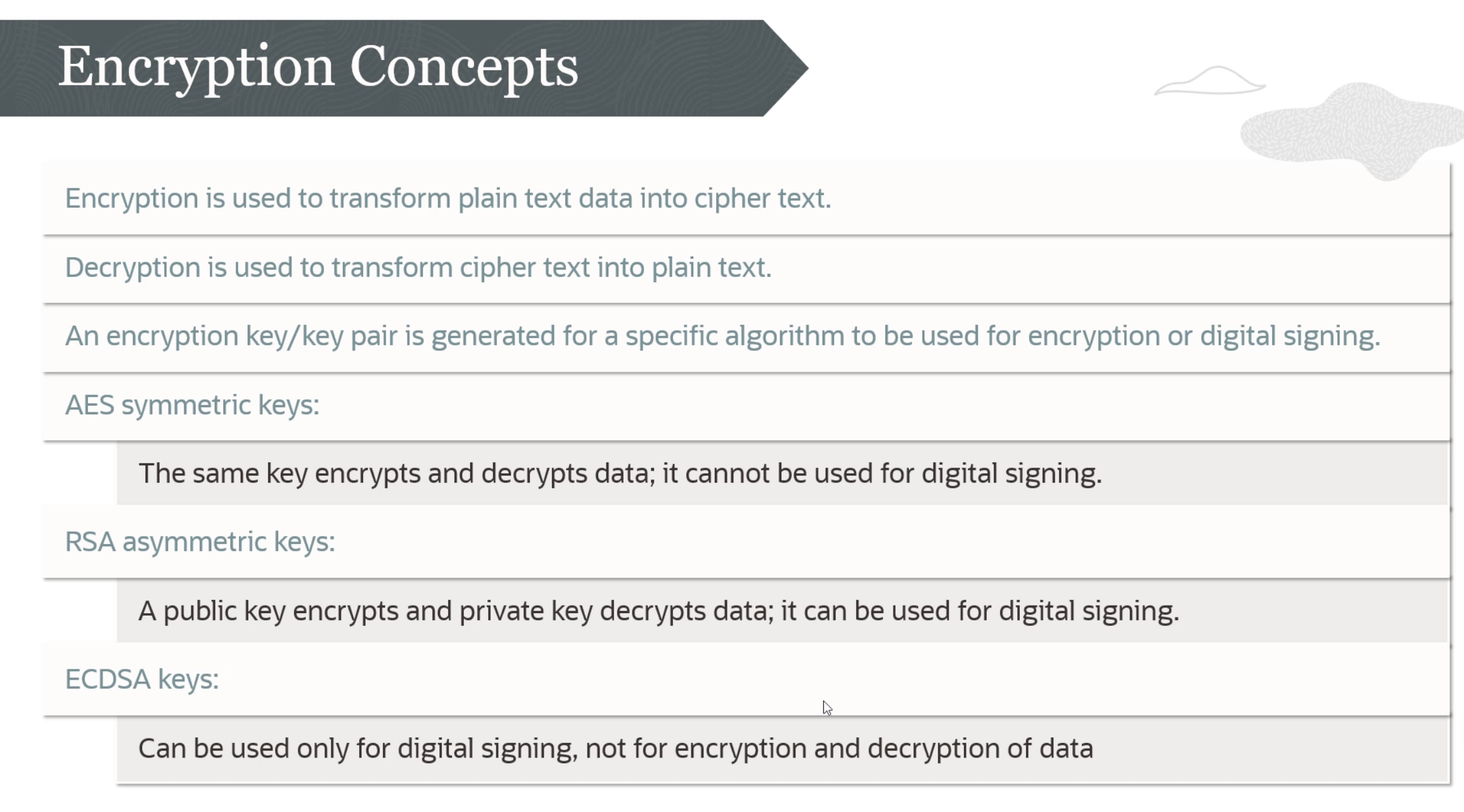
2023-09-26_22-10-35_screenshot.png #
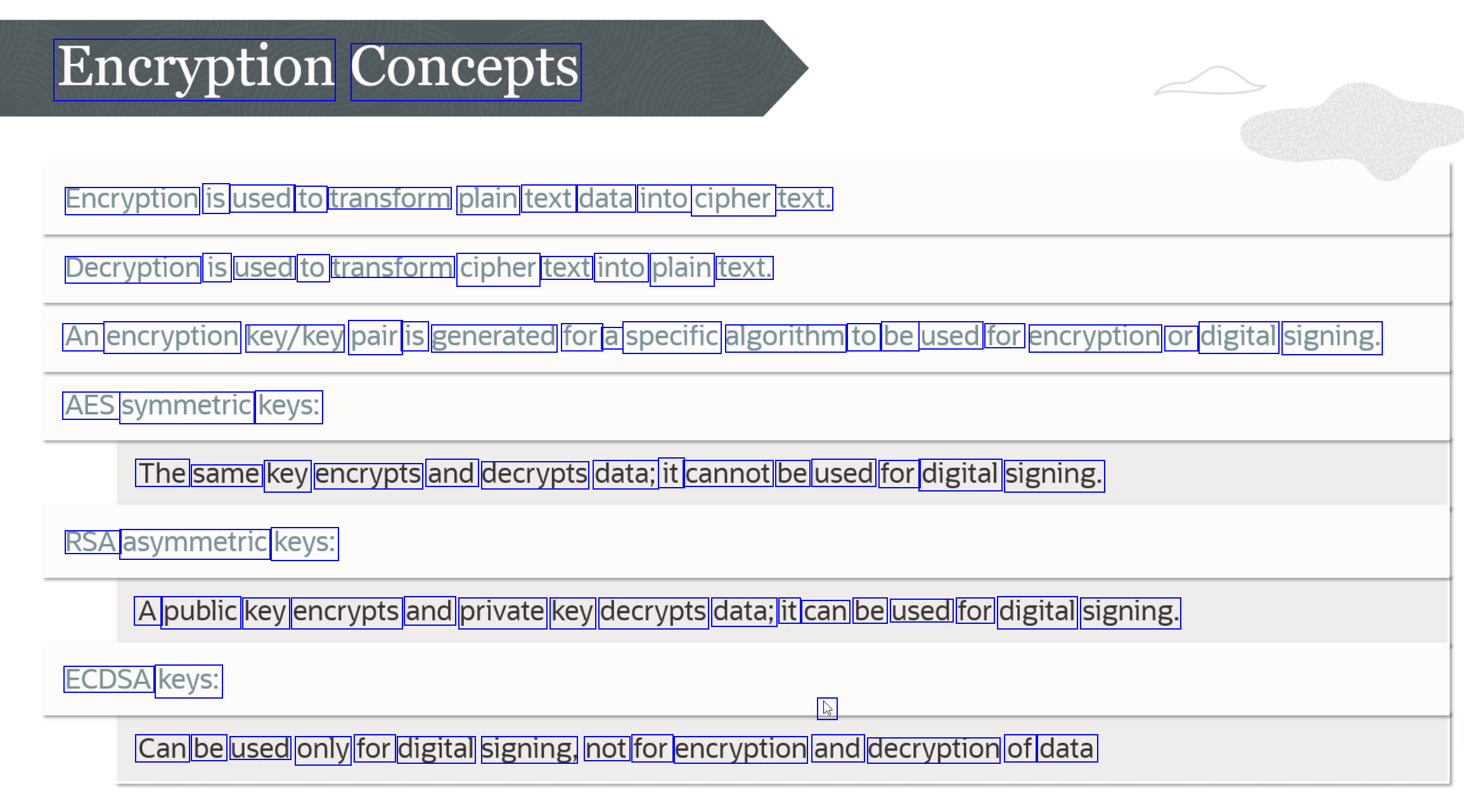
Encryption Concepts Encryption is used to transform plain text data into cipher text. Decryption is used to transform cipher text into plain text. An encryption key/key pair is generated for a specific algorithm to be used for encryption or digital signing. AES symmetric keys: The same key encrypts and decrypts data; it cannot be used for digital signing. RSA asymmetric keys: A public key encrypts and private key decrypts data; it can be used for digital signing. ECDSA keys: L Can be used only for digital signing, not for encryption and decryption of data
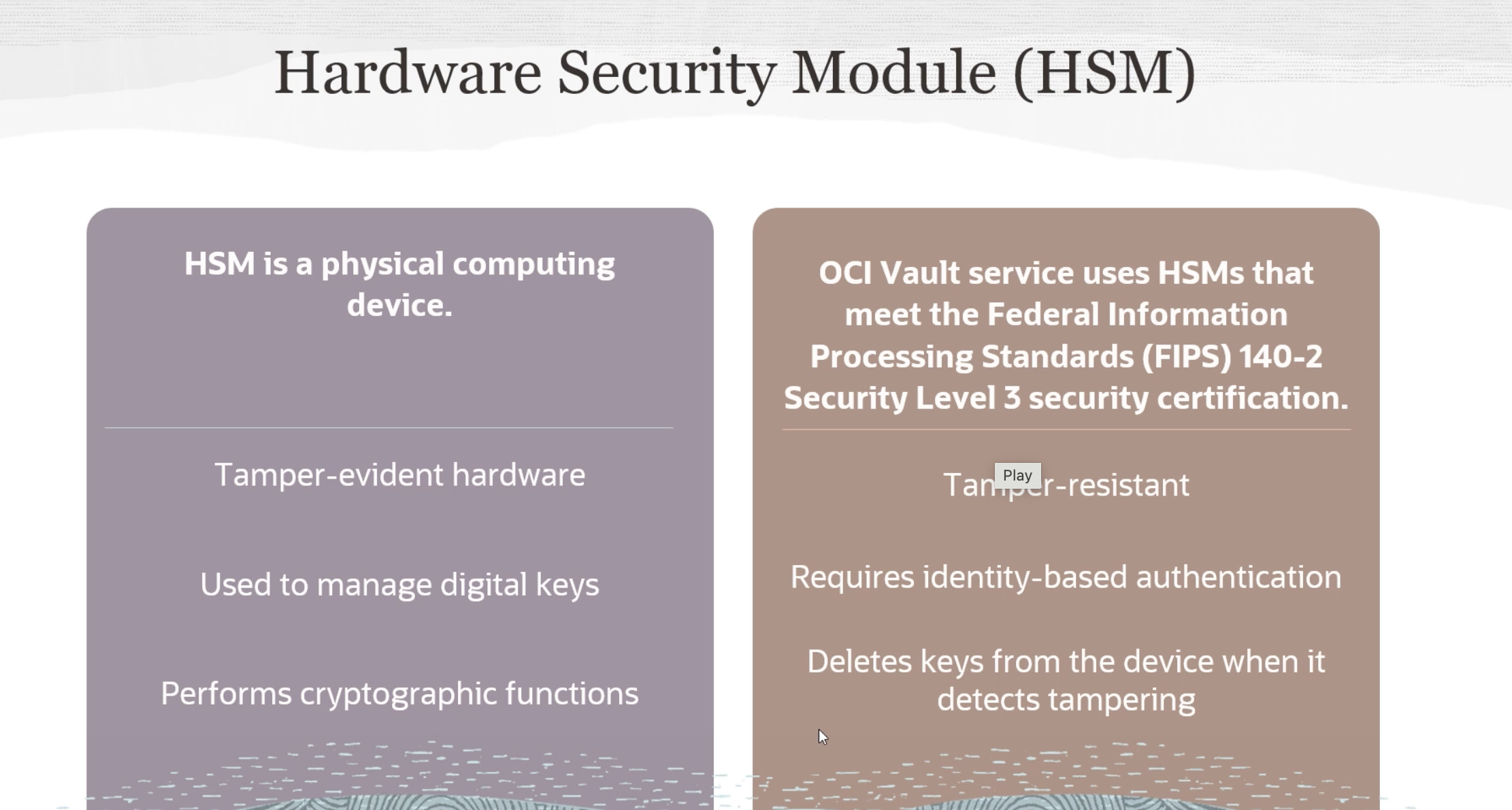
2023-09-26_22-11-29_screenshot.png #
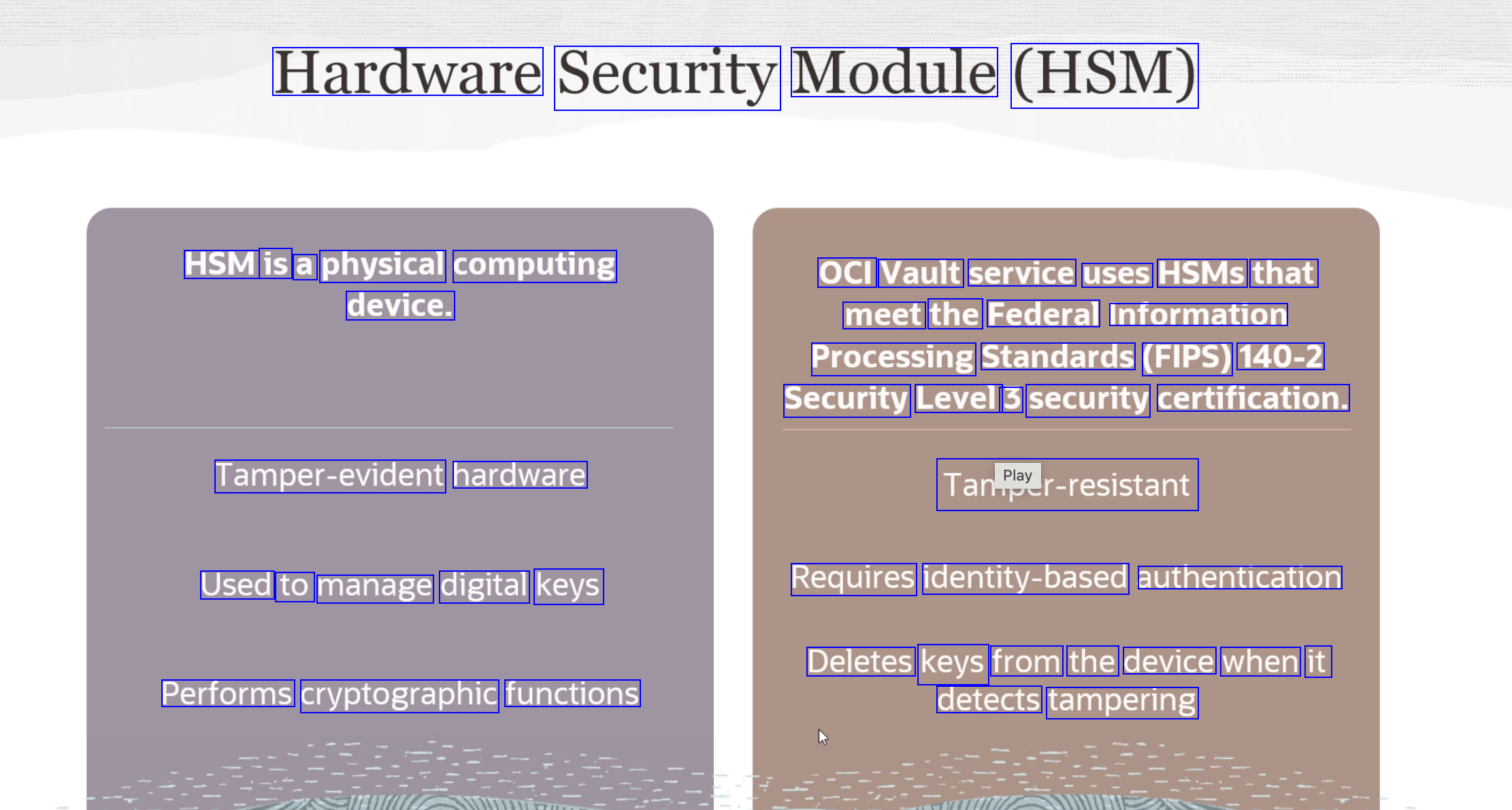
Hardware Security Module (HSM) HSM is a physical computing OCI Vault service uses HSMS that meet the Federal Information Processing Standards (FIPS) 140-2 Security Level 3 security certification. device. Tamper-evident hardware Tanlmper-resistant Used to manage digital keys Requires identity-based authentication Deletes keys from the device when it Performs cryptographic functions detects tampering
2023-09-26_22-13-37_screenshot.png #
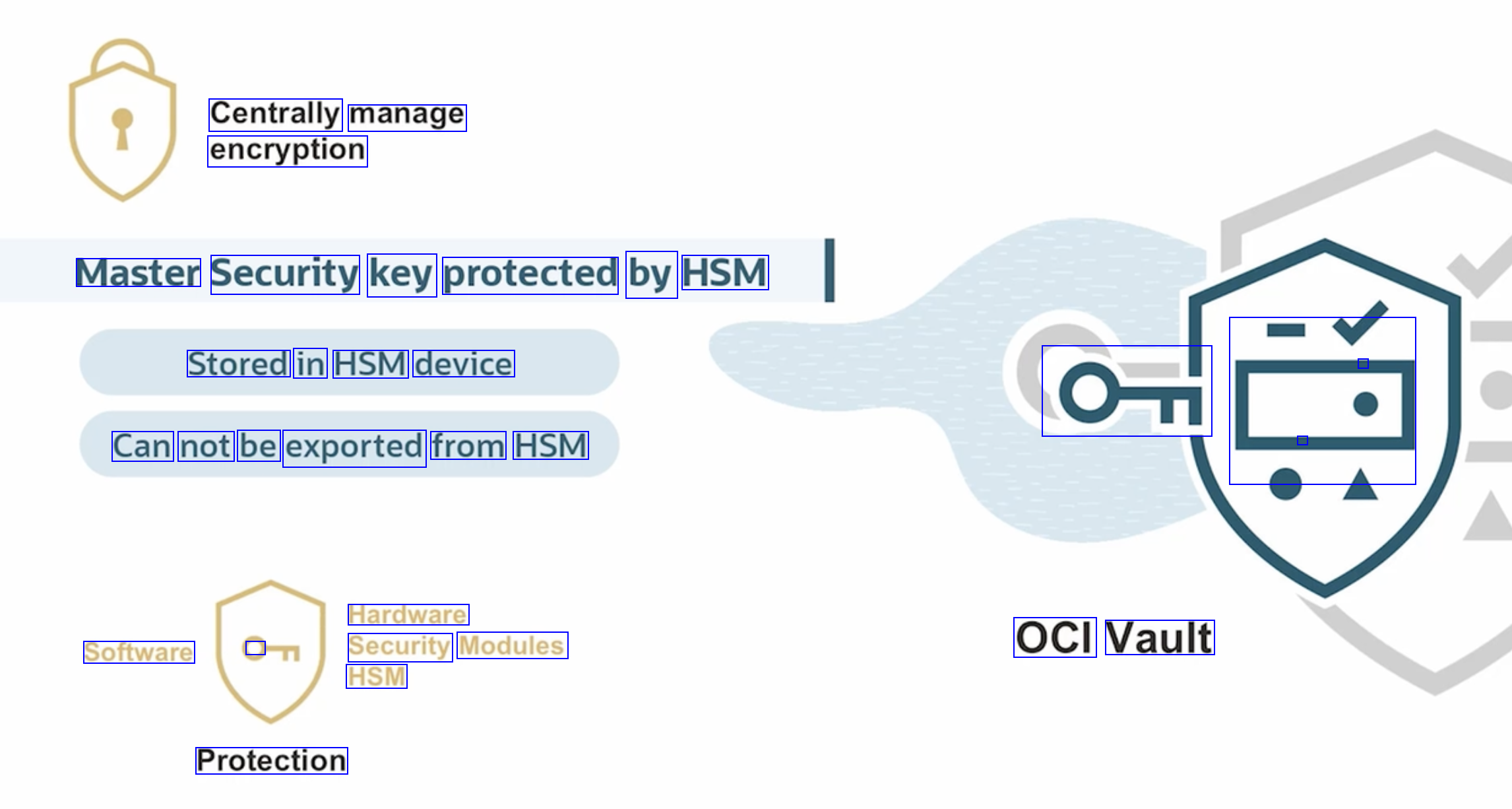
Centrally manage encryption Master Security key protected by HSM Stored in HSM device - OT Can not be exported from HSM - Ca Hardware Security Modules HSM Software 0 OCI Vault Protection
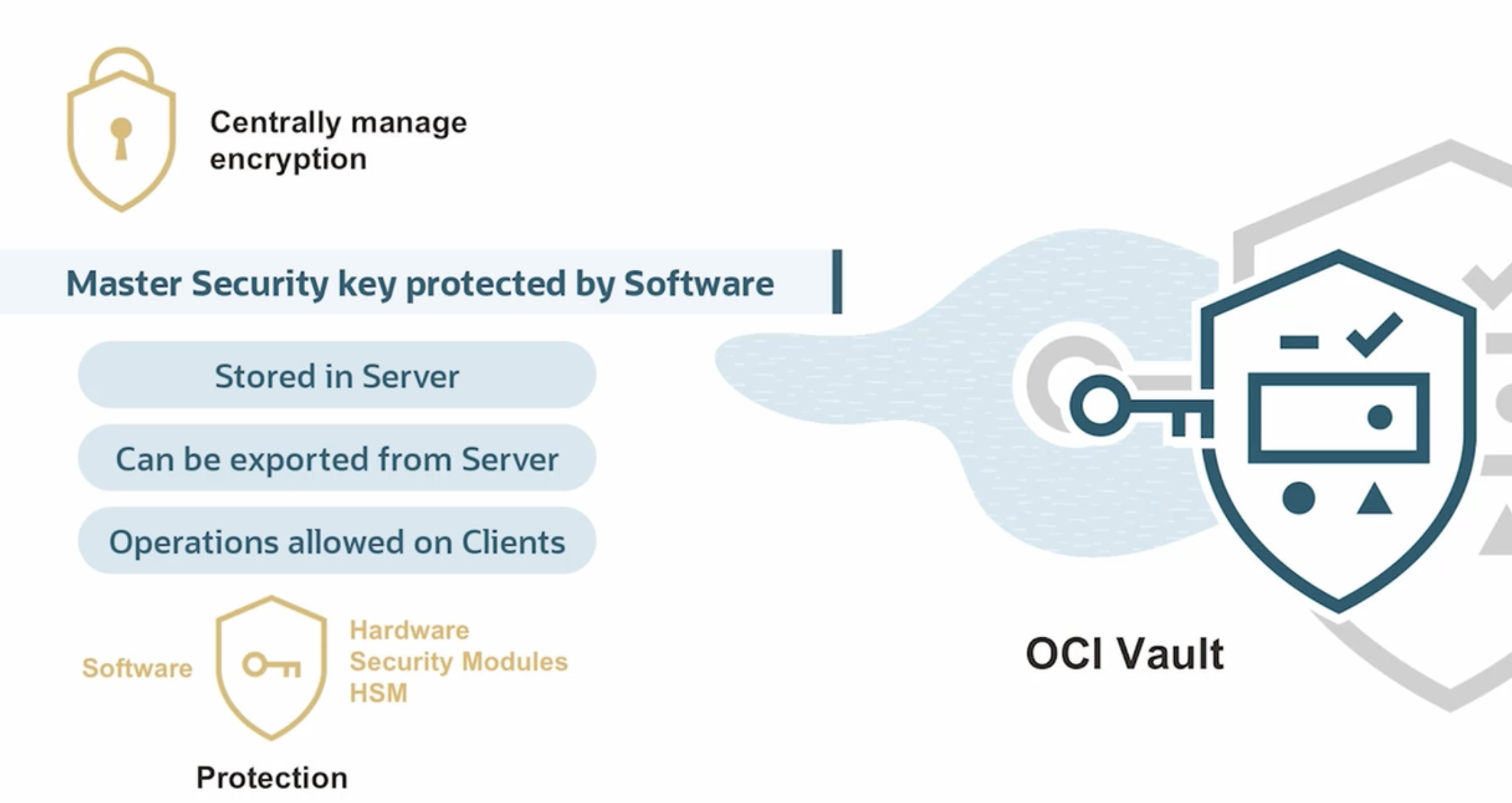
2023-09-26_22-13-46_screenshot.png #
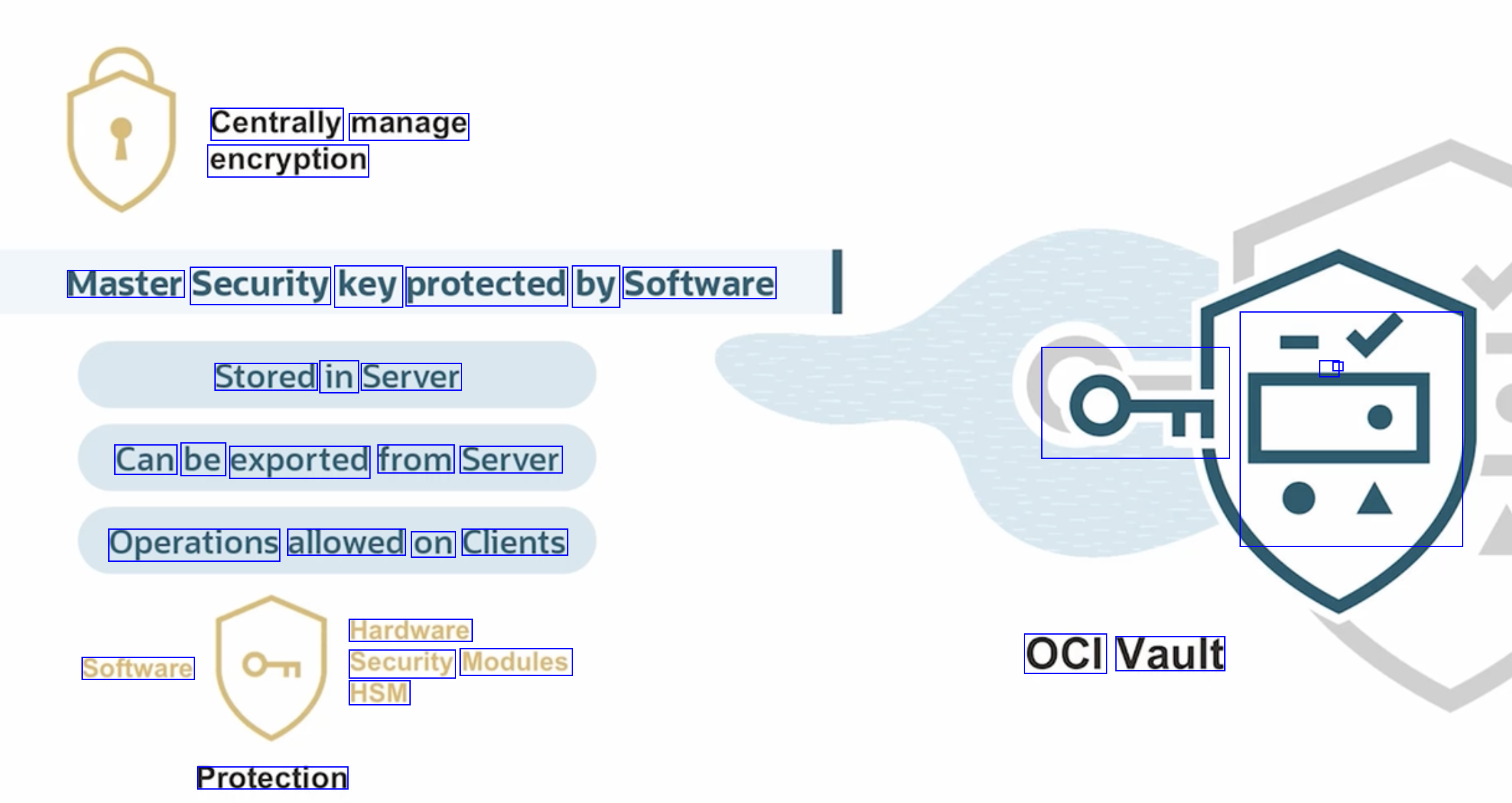
Centrally manage encryption Master Security key protected by Software Stored in Server - - OT Can be exported from Server E Operations allowed on Clients Hardware Security Modules HSM Software OCI Vault Protection
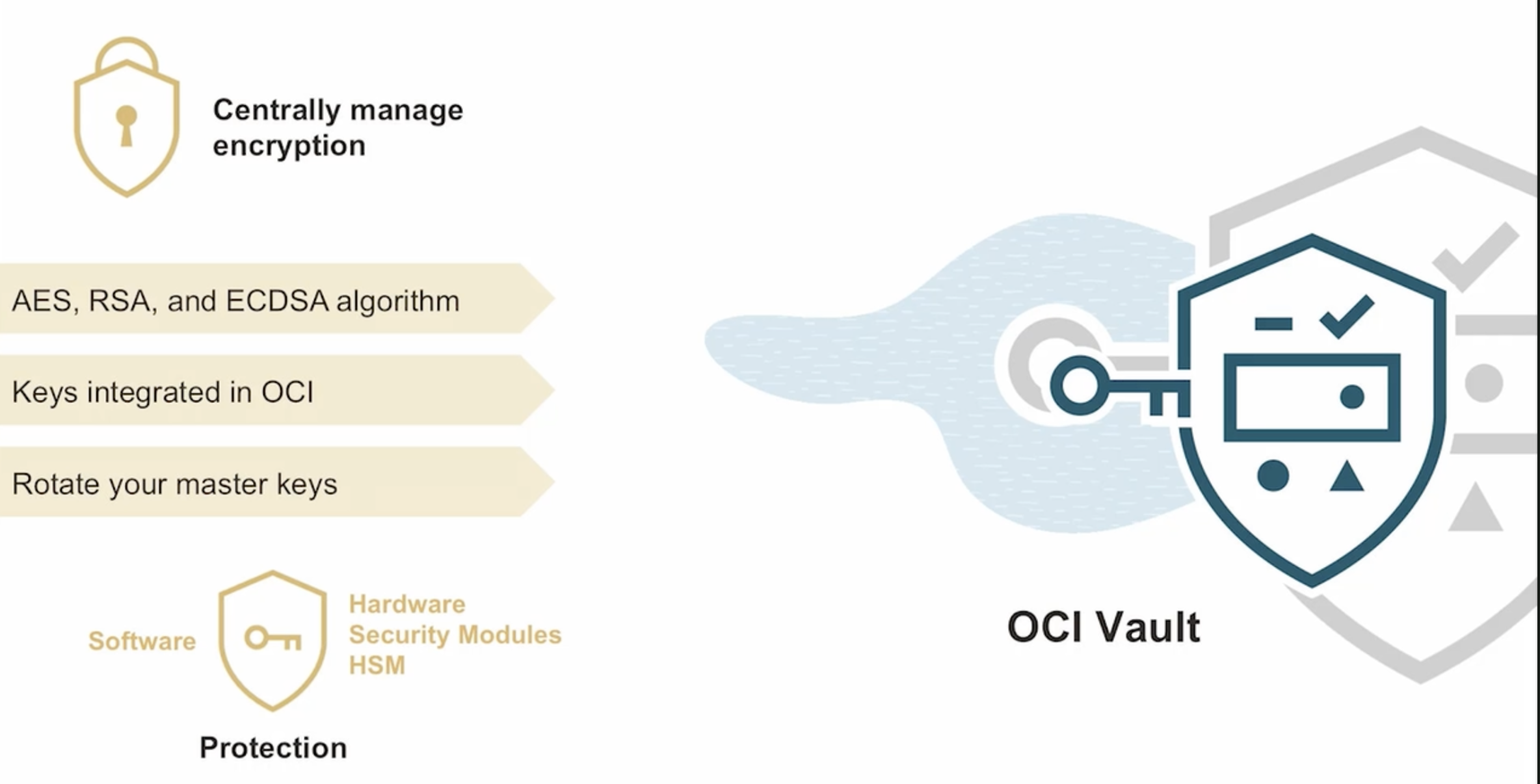
2023-09-26_22-14-30_screenshot.png #
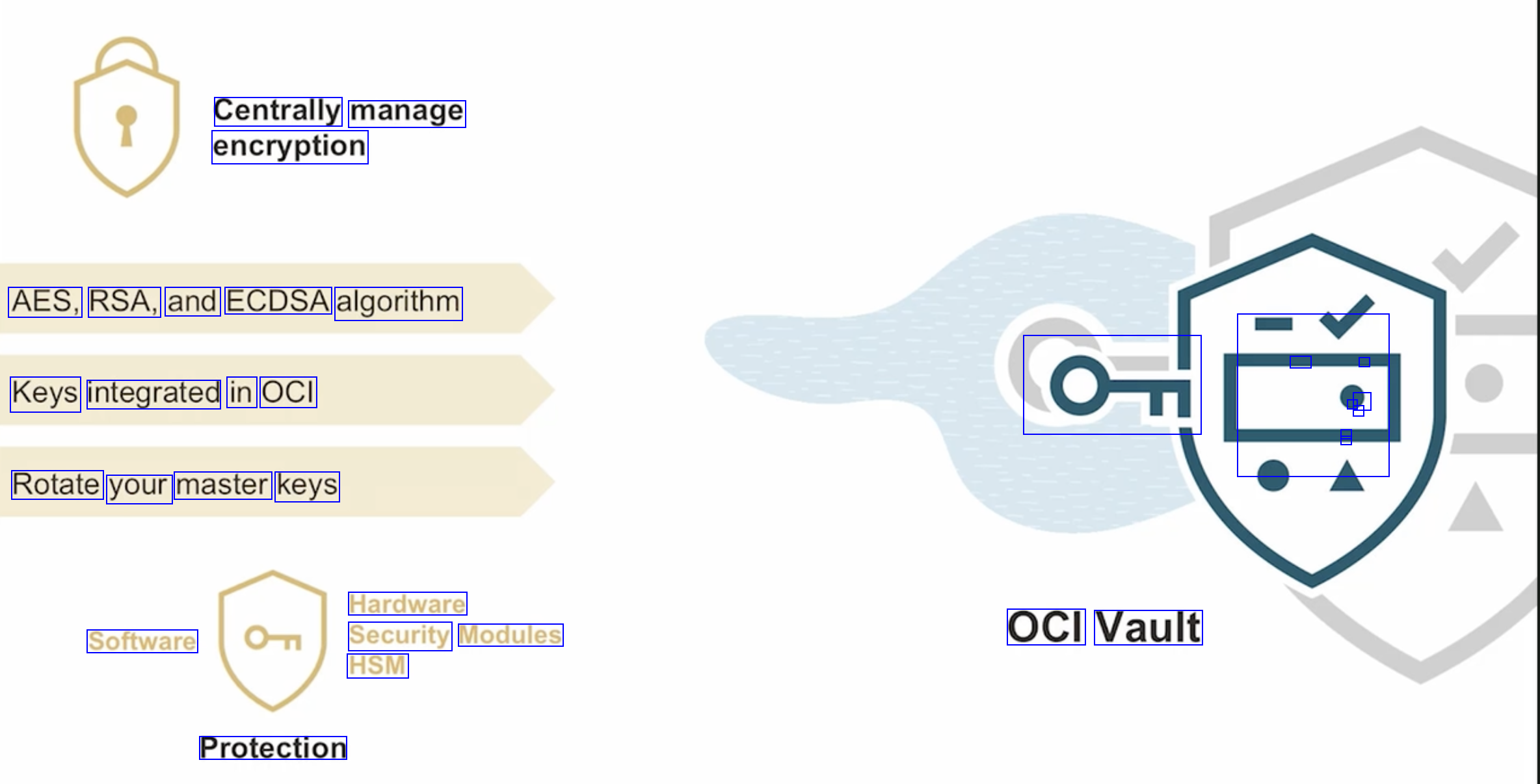
Centrally manage encryption AES, RSA, and ECDSA algorithm - - L J - - - - Keys integrated in OCI OT Rotate your master keys Hardware Security Modules HSM Software OCI Vault Protection
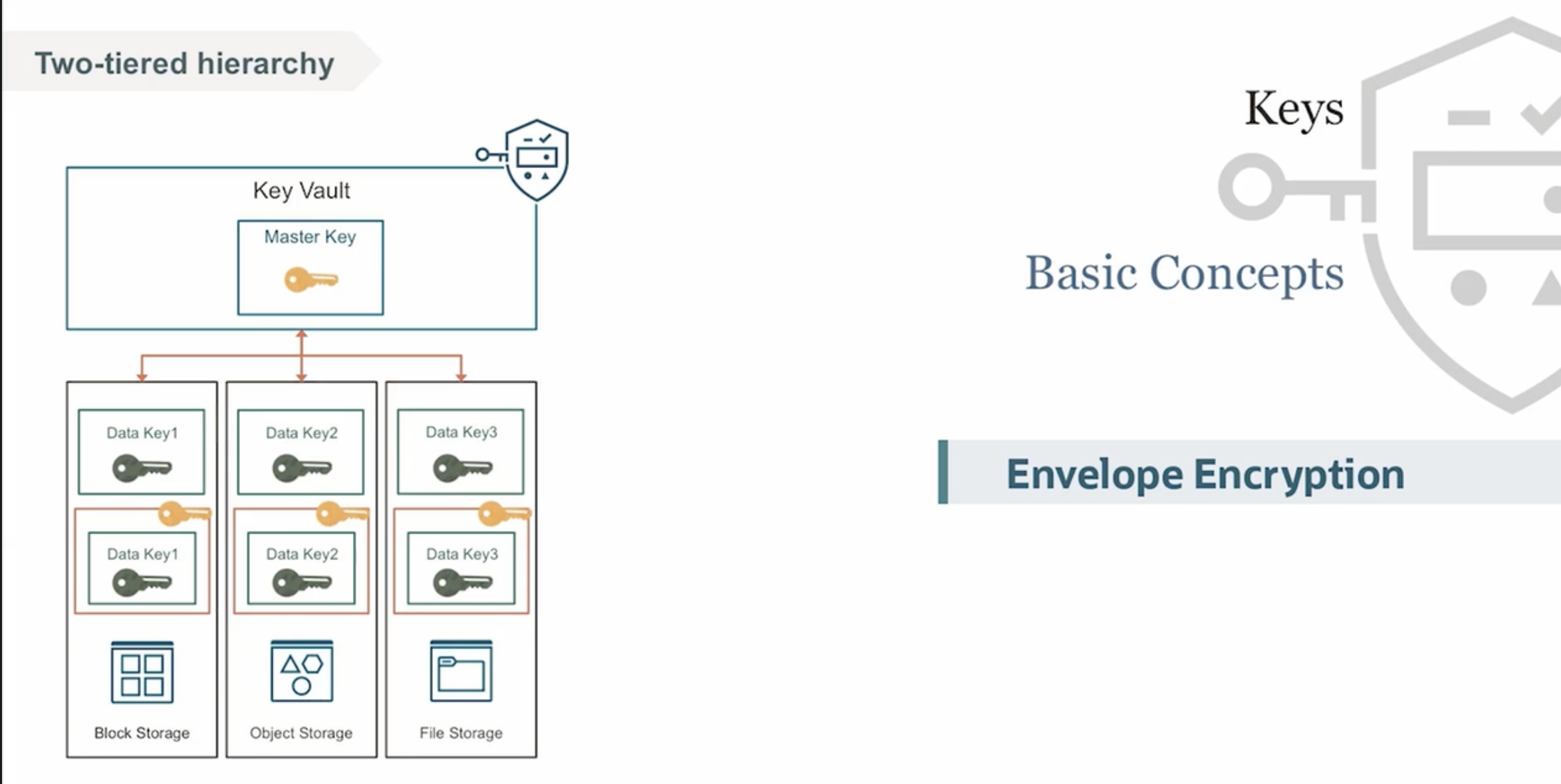
2023-09-26_22-15-24_screenshot.png #
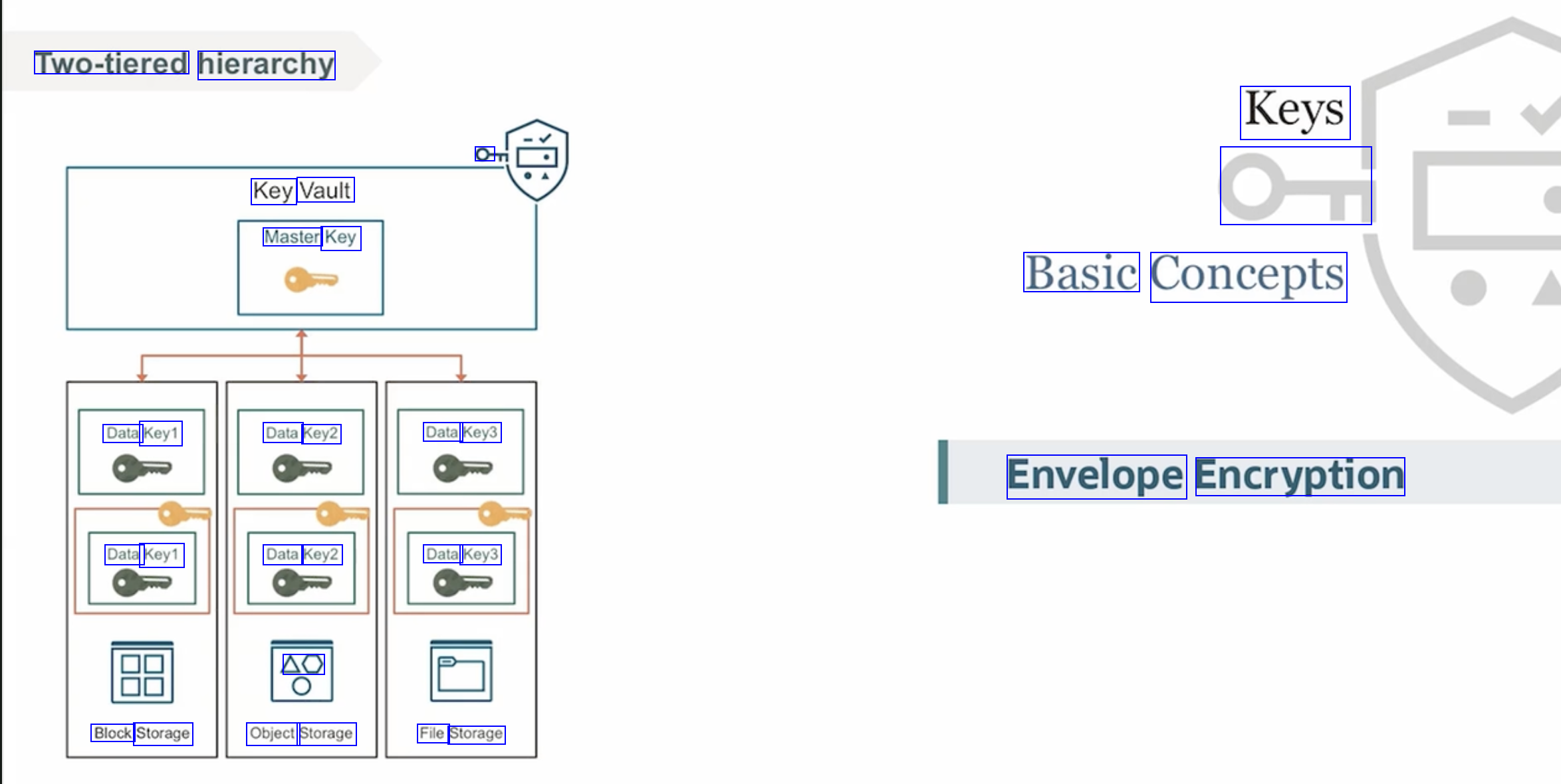
Two-tiered hierarchy Keys O Key Vault Master Key On Basic Concepts Data Key1 Data Key2 Data Key3 Envelope Encryption Data Key1 Data Key2 Data Key3 AO Block Storage Object Storage File Storage
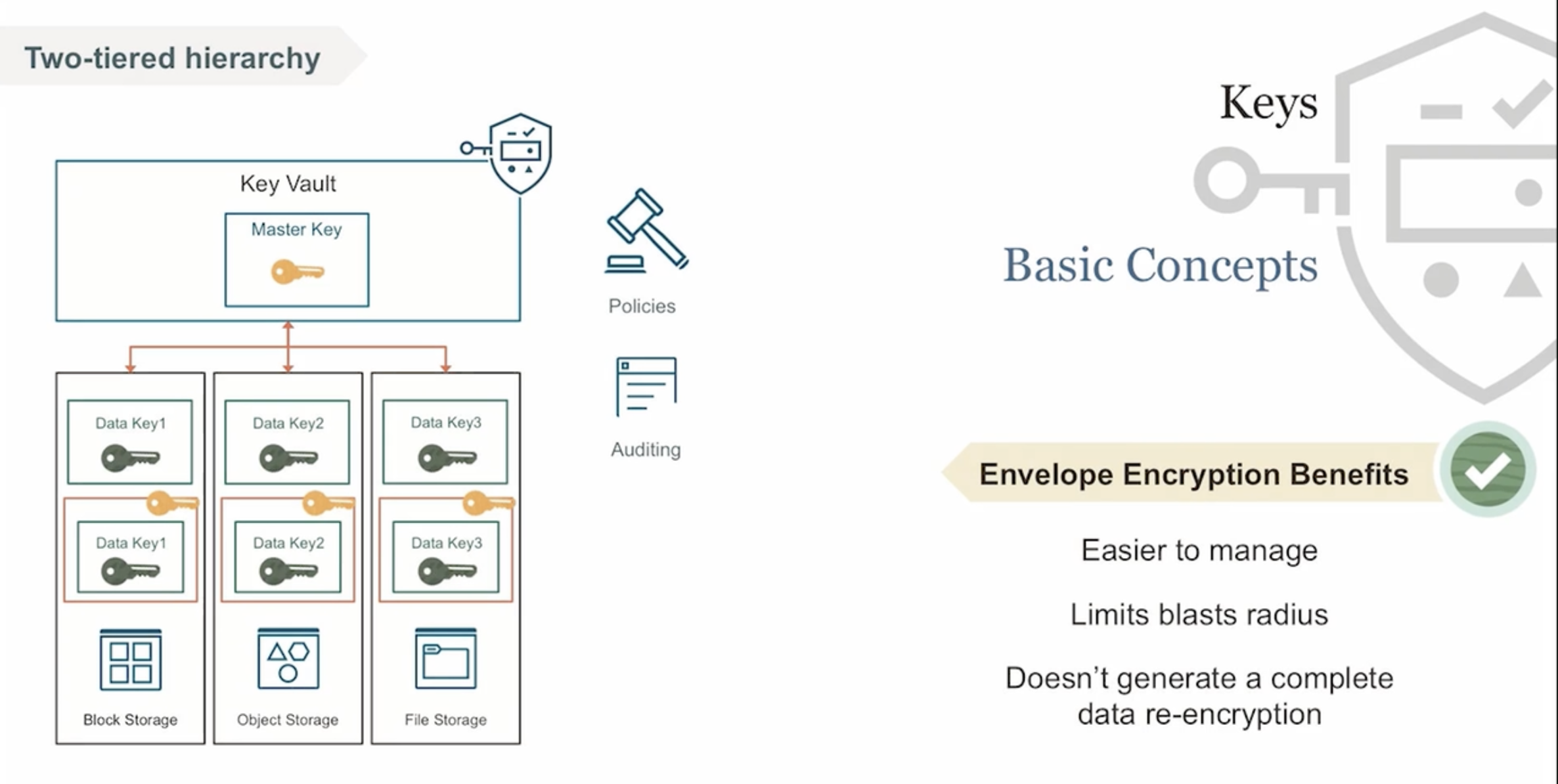
2023-09-26_22-15-43_screenshot.png #
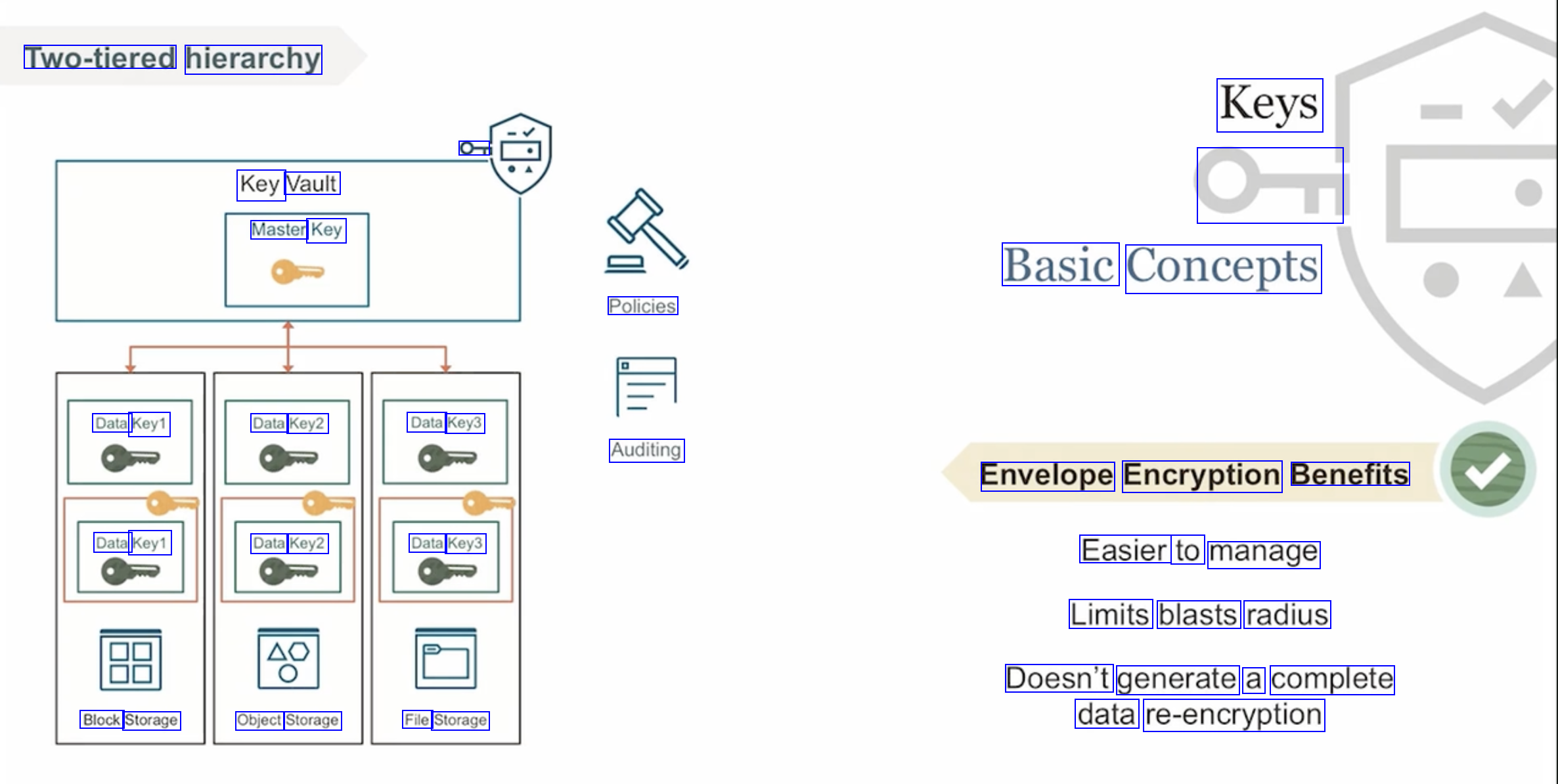
Two-tiered hierarchy Keys OT Key Vault Master Key On Basic Concepts Policies Data Key1 Data Key2 Data Key3 Auditing Envelope Encryption Benefits Data Key1 Data Key2 Data Key3 Easier to manage Limits blasts radius Doesn't generate a complete data re-encryption Block Storage Object Storage File Storage
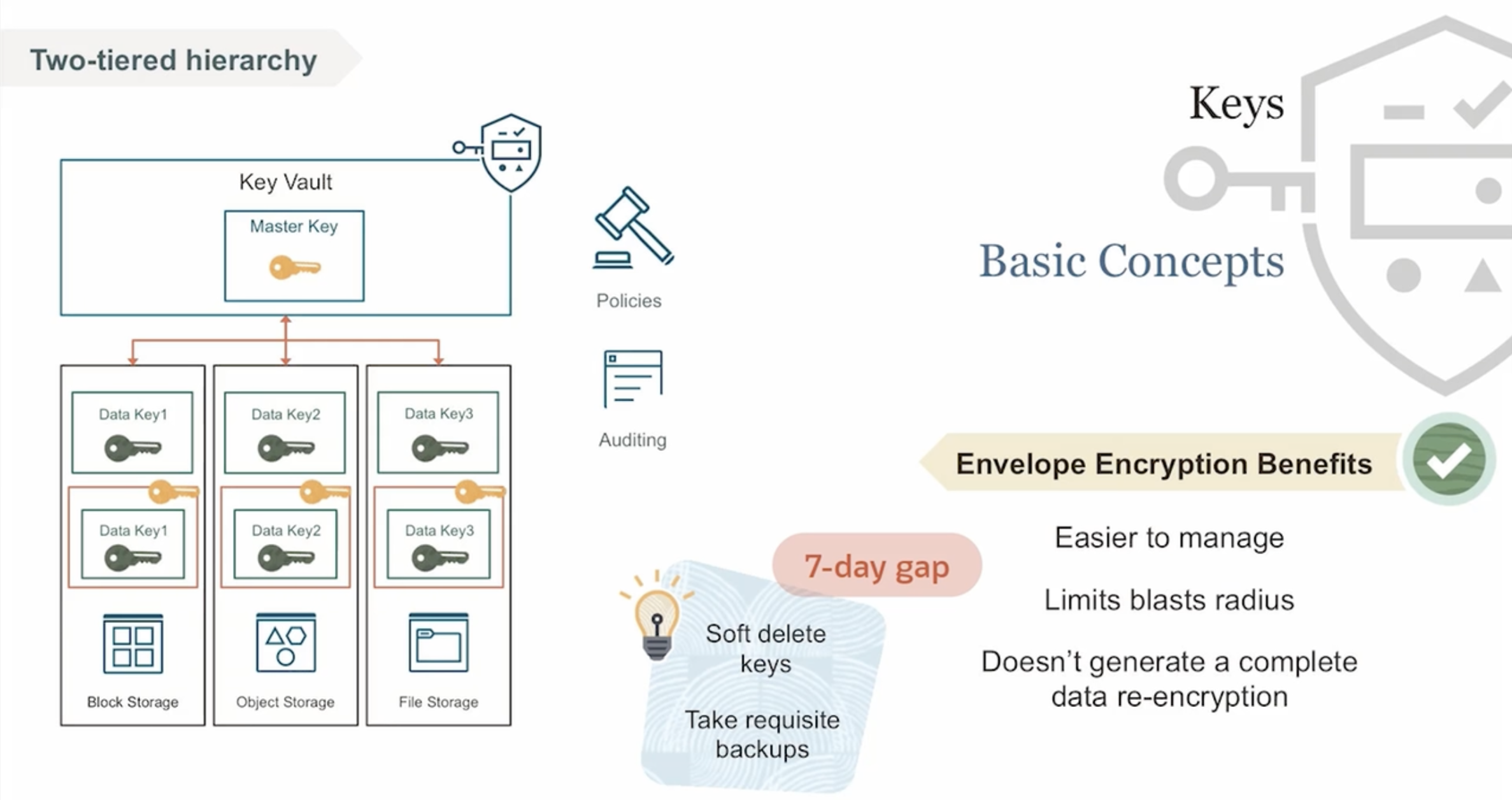
2023-09-26_22-16-09_screenshot.png #
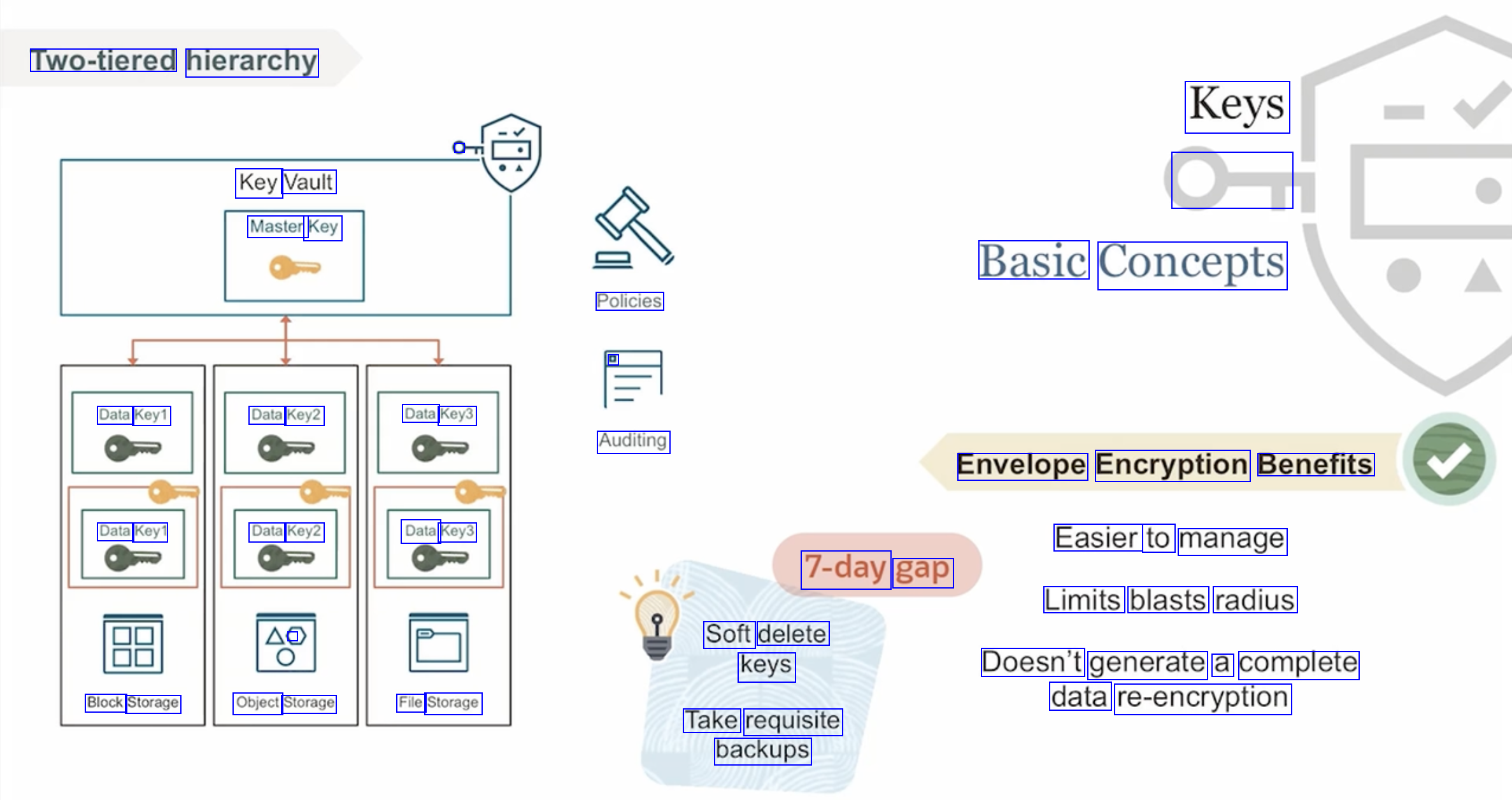
Two-tiered hierarchy Keys Key Vault Master Key O Basic Concepts Policies D Data Key1 Data Key2 Data Key3 Auditing Envelope Encryption Benefits Data Key1 Data Key2 Data Key3 Easier to manage 7-day gap Limits blasts radius ( Soft delete keys Doesn't generate a complete data re-encryption Block Storage Object Storage File Storage Take requisite backups
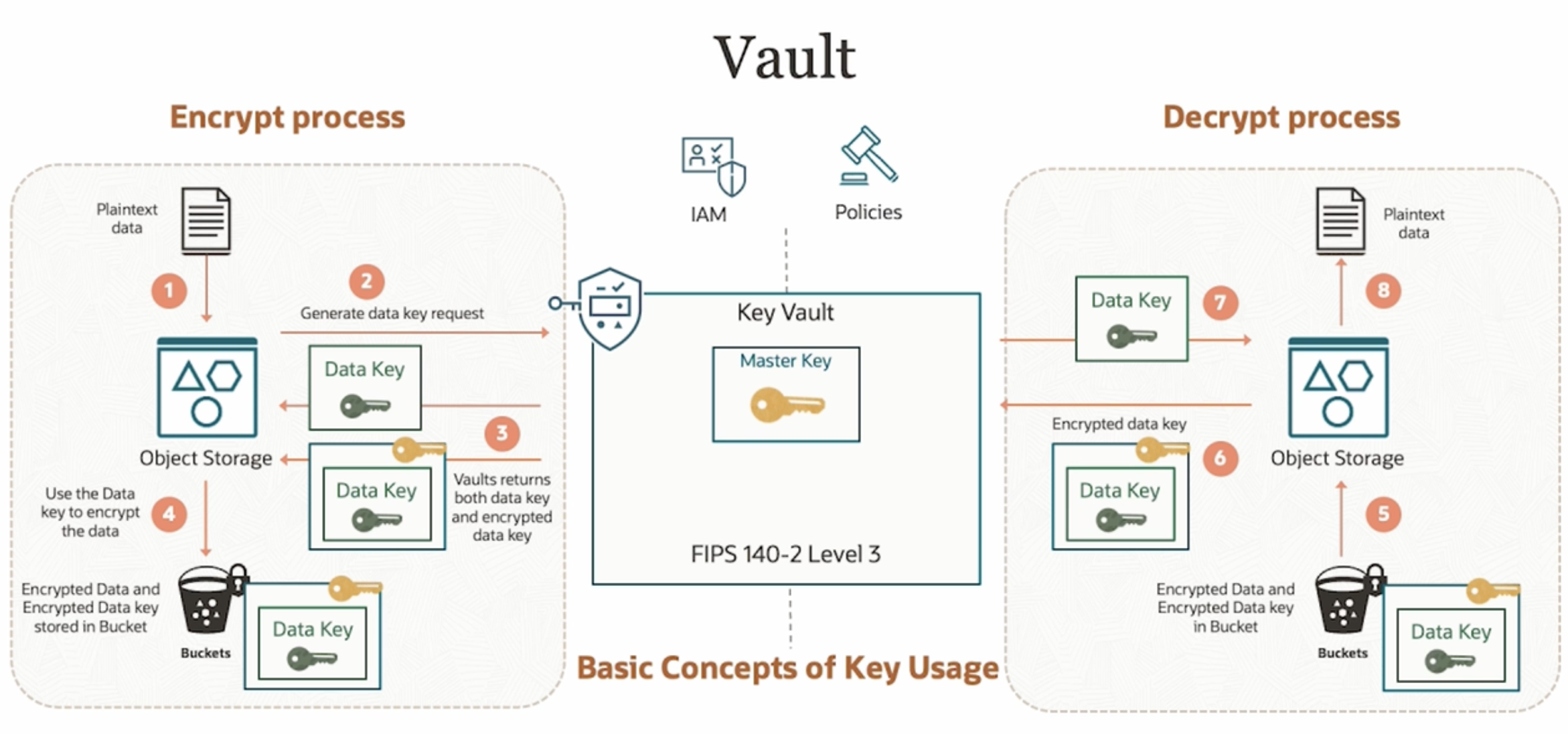
2023-09-26_22-17-35_screenshot.png #
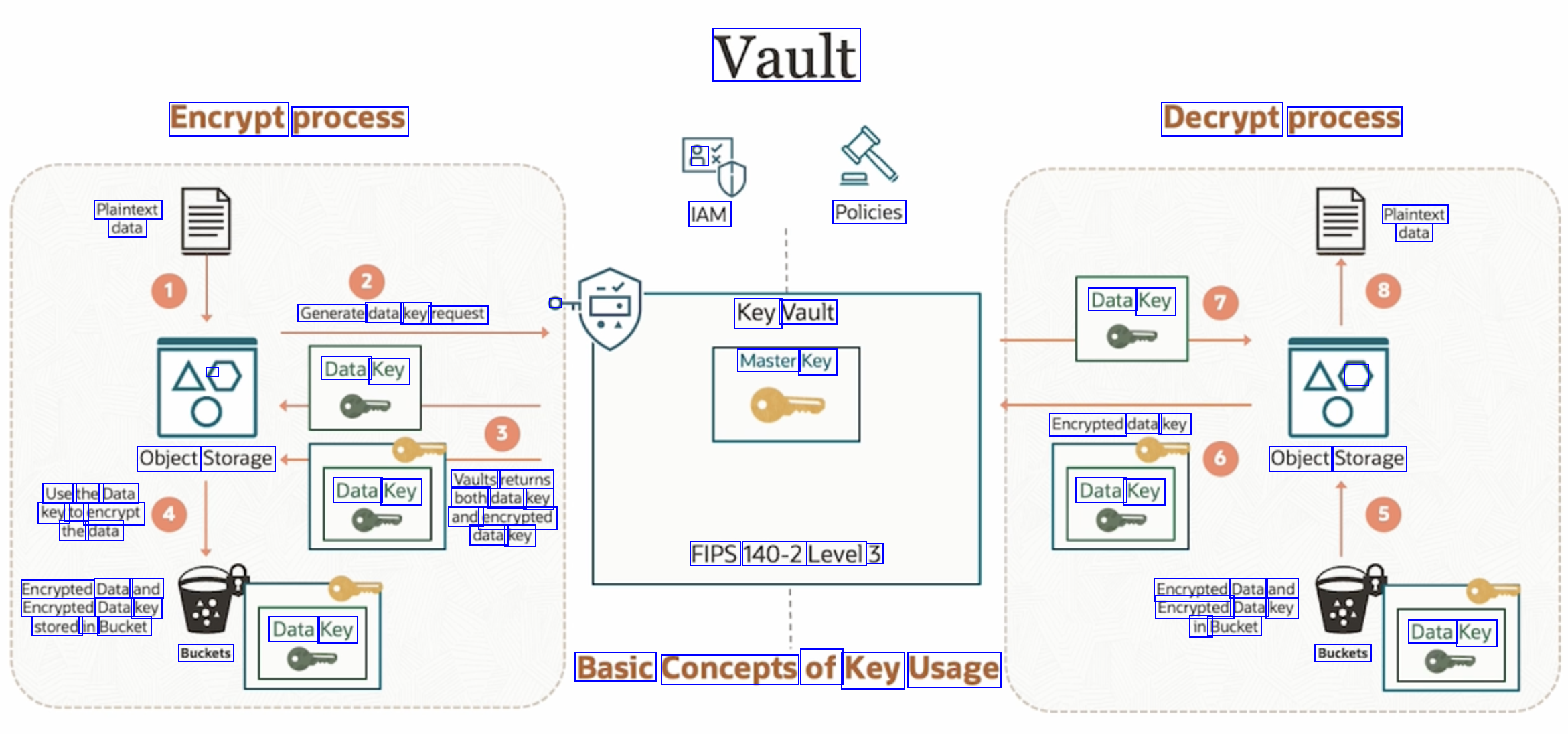
Vault Encrypt process Decrypt process 3 Plaintext data IAM Policies Plaintext data 0 Data Key Generate data key request Key Vault Master Key - Data Key - Encrypted data key Object Storage Object Storage Vaults returns Data Key both data key and encrypted data key Use the Data key to encrypt the data Data Key FIPS 140-2 Level 3 Encrypted Data and Encrypted Data key stored in Bucket Encrypted Data and Encrypted Data key in Bucket Data Key Data Key Buckets Buckets Basic Concepts of Key Usage
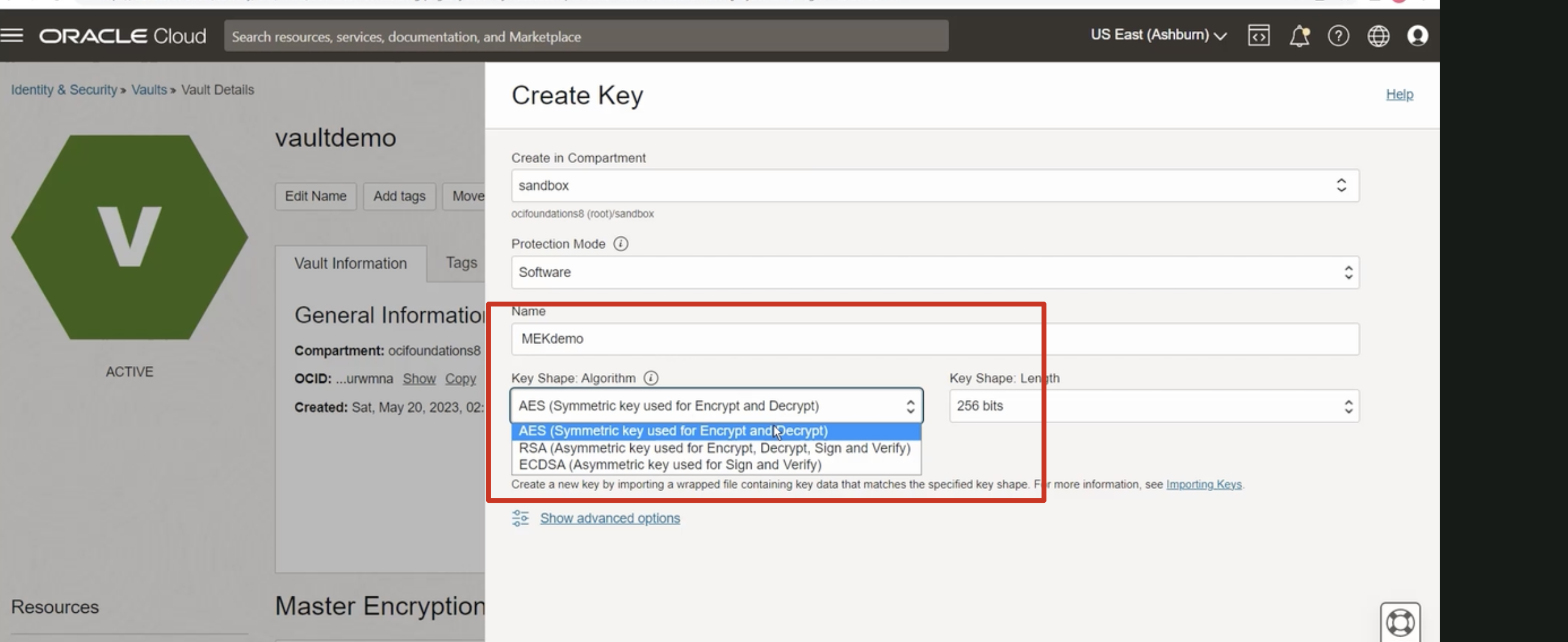
2023-09-26_22-23-34_screenshot.png #
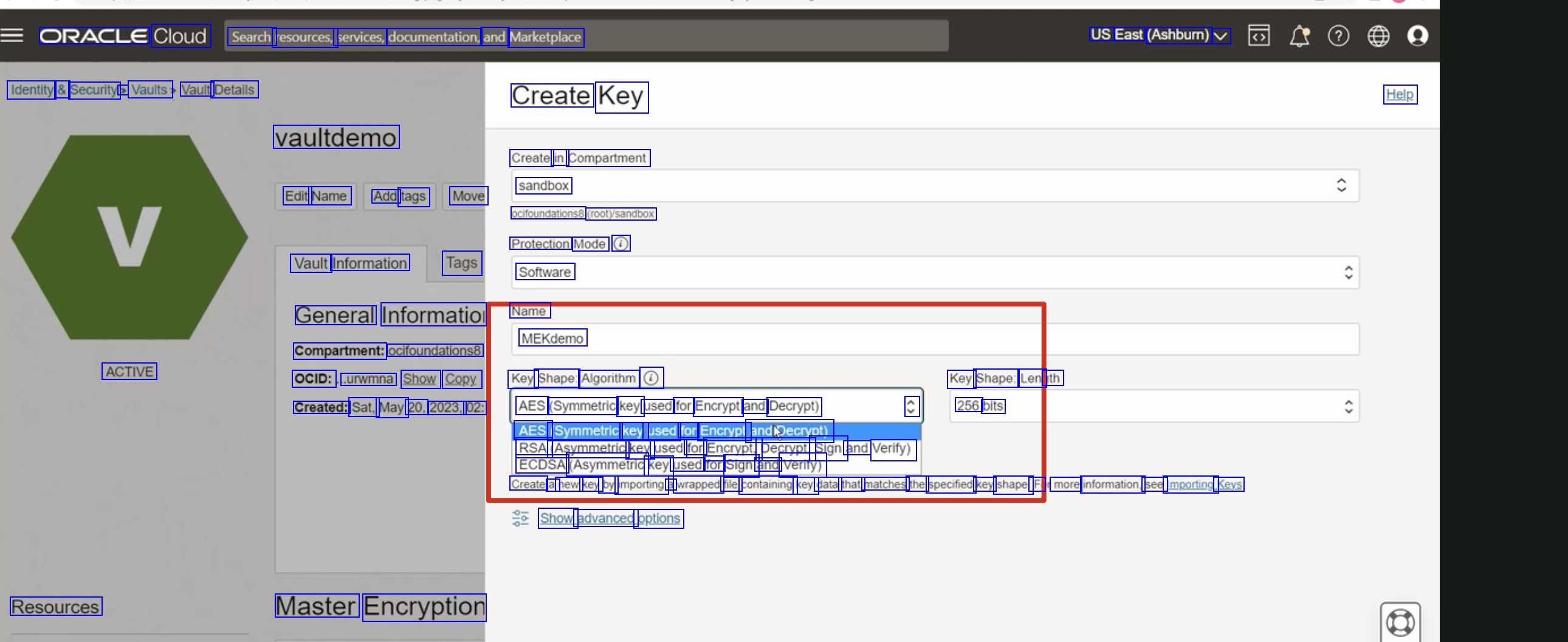
ORACLE Cloud Search resources, services, documentation, and Marketplace US East (Ashbumn) V Identity & Security > Vaults Vault Details Create Key Help vaultdemo Create in Compartment sandbox ocifoundations8 (rooty/sandbox Protection Mode 0 Software Edit Name Add tags Move Vault Information Tags General Information Name Compartment: ocifoundations8 MEKdemo ACTIVE OCID: .urwmna Show Copy Key Shape: Algorithm 0 Key Shape: Len th C 256 bits Created: Sat, May 20, 2023, 02: AES (Symmetric key used for Encrypt and Decrypt) AES (Symmetric key used for Encrypt andpecrypt) RSA (Asymmetric key used for Encrypt, Decrypt, Sign and Verify) ECDSA (Asymmetric key used for Sign and Verify) Create a new key by importing a wrapped file containing key data that matches the specified key shape. F more information, see Importing Keys Show advanced options Resources Master Encryption
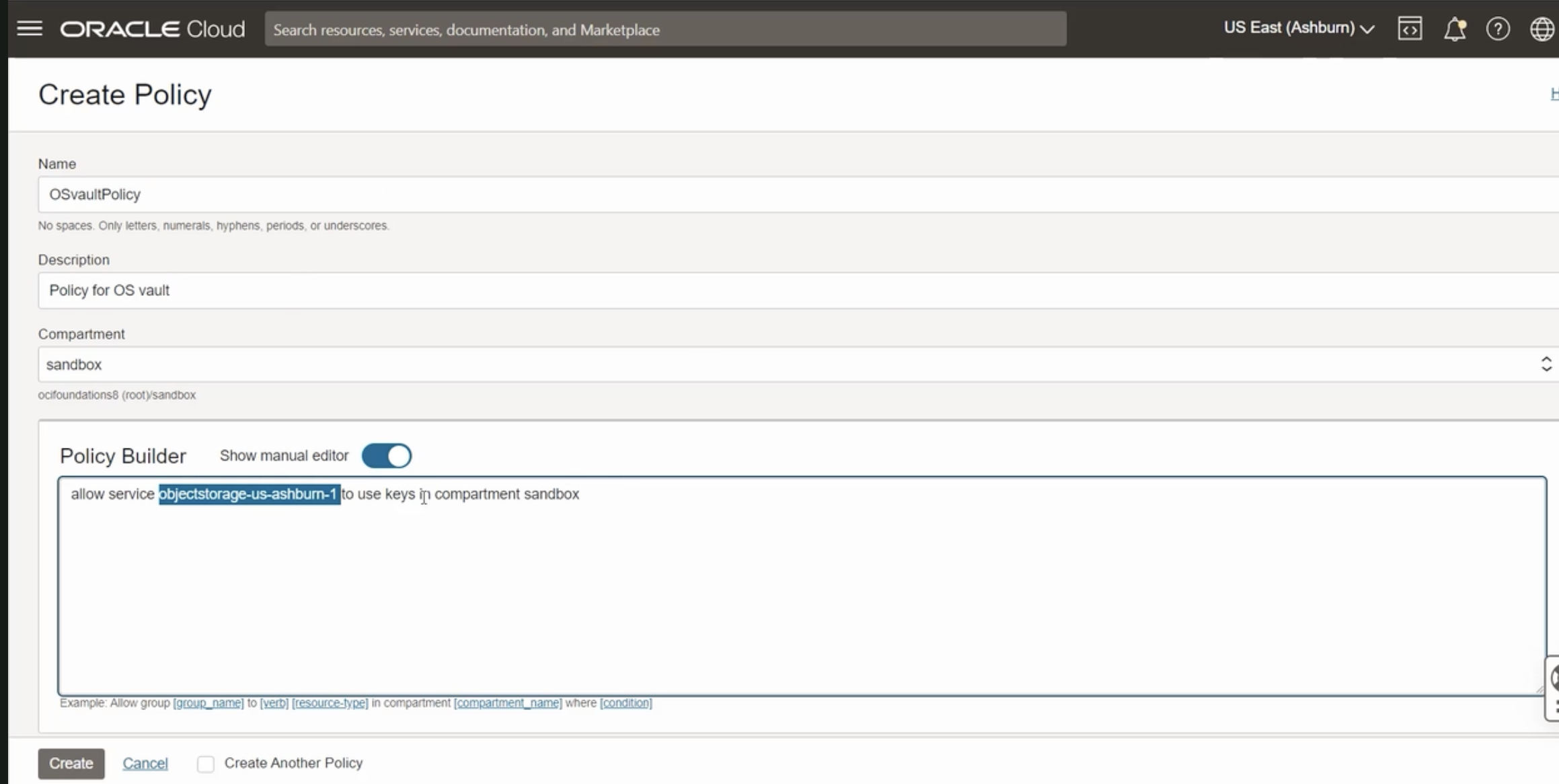
2023-09-26_22-24-49_screenshot.png #
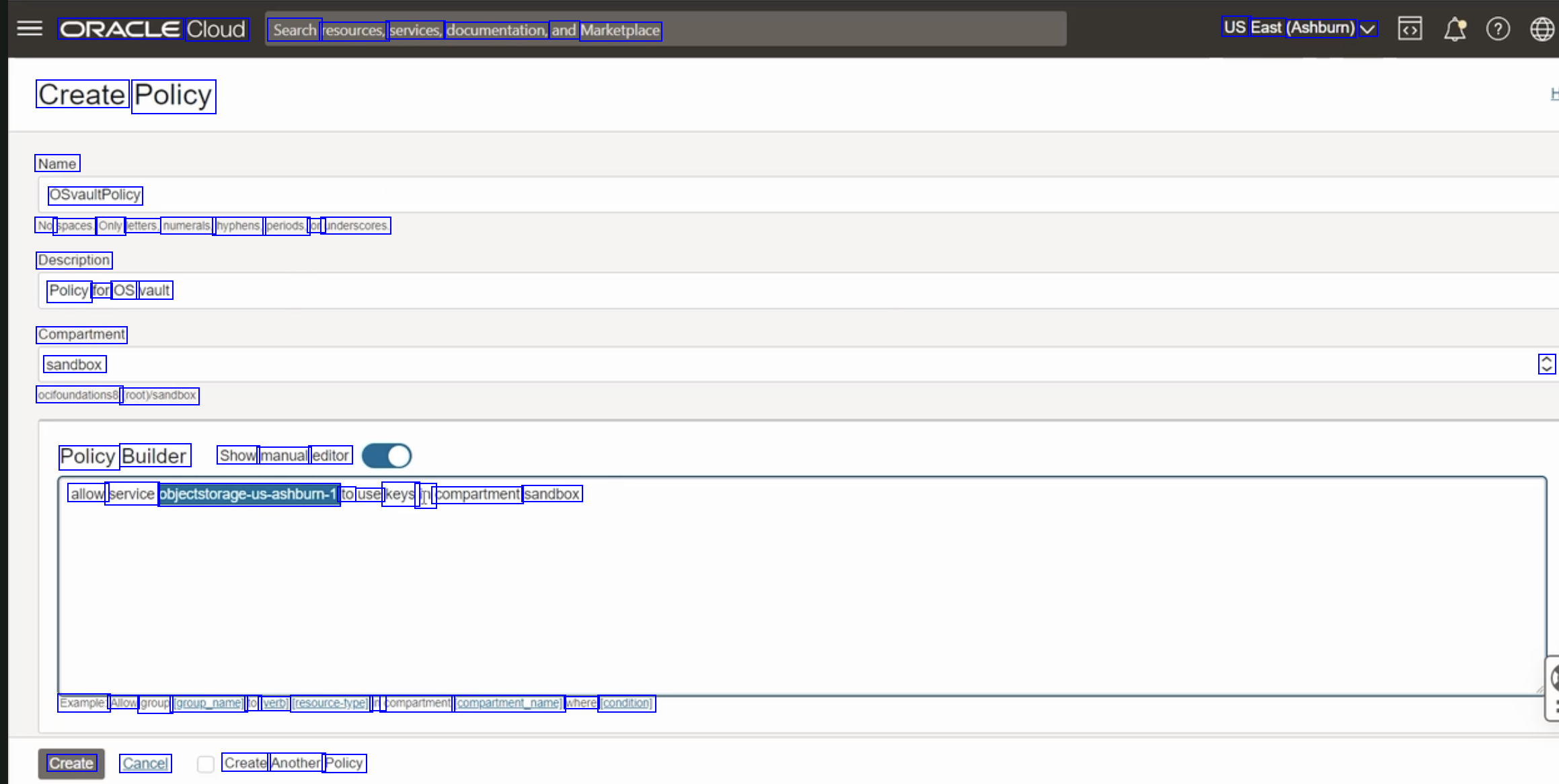
ORACLE Cloud Search resources, services, documentation, and Marketplace US East (Ashburn) V Create Policy Name OSvaultPolicy No spaces. Only letters, numerals, hyphens, periods, or underscores. Description Policy for OS vault Compartment sandbox ocifoundationss (rootysandbox C Policy Builder Show manual editor allow service obiectslorngeus-amhbum1 to use keys in compartment sandbox Example: Allow group (group_name] to [verb] (resource-ype) in compartment Ccomparimenunamel where (condition) Create Cancel Create Another Policy
2023-09-26_22-26-42_screenshot.png #
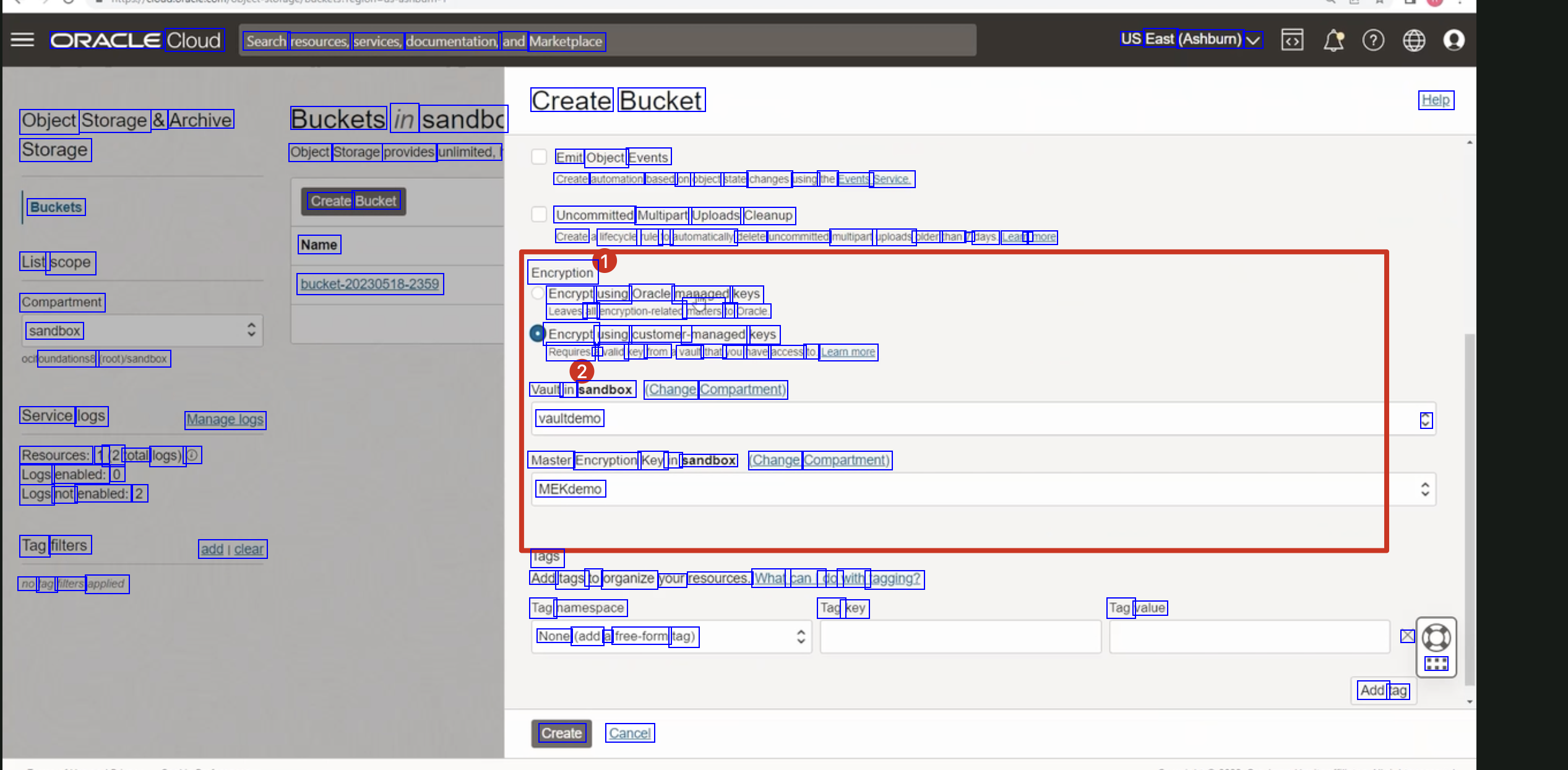
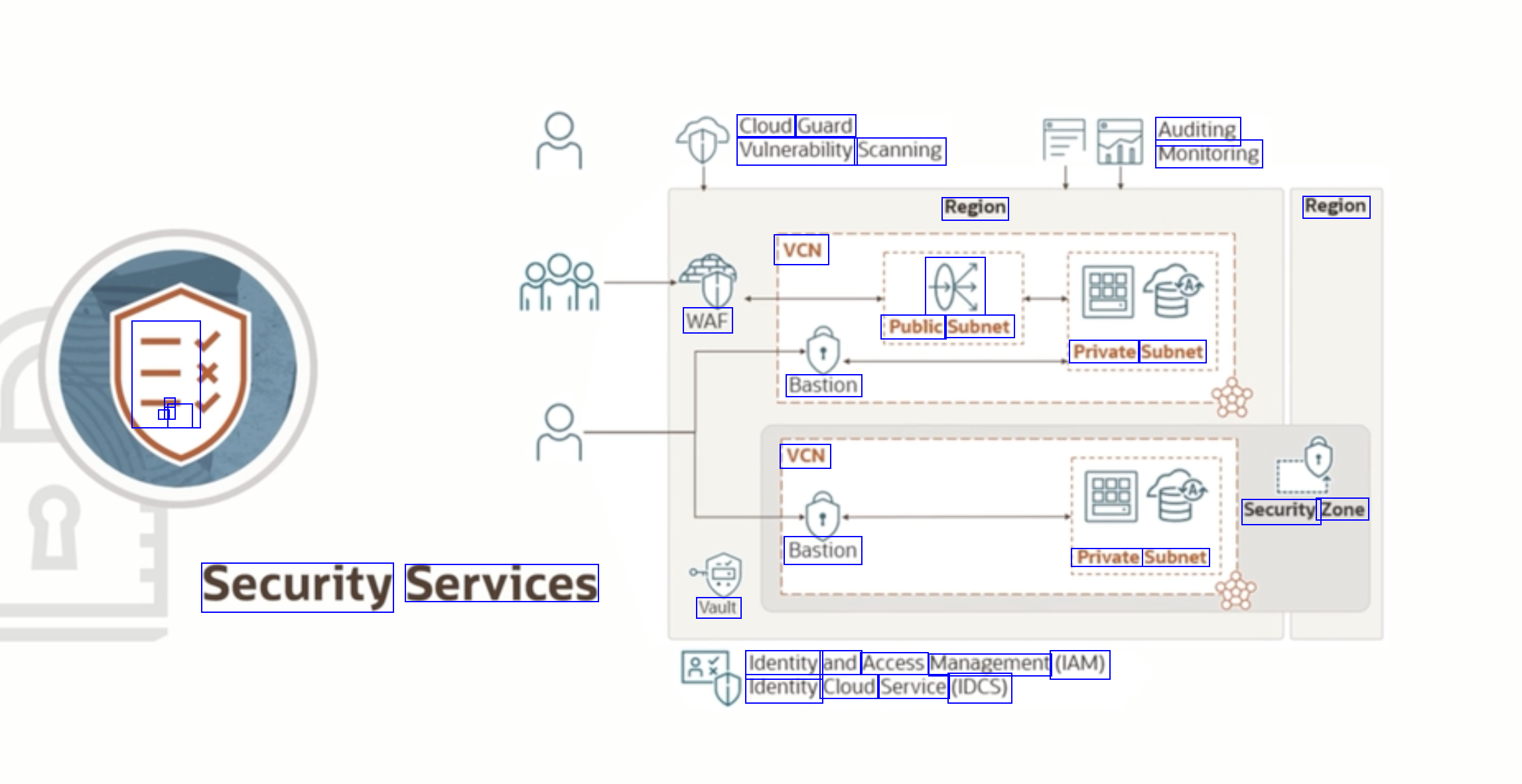
ORACLE Cloud Search resources, services, documentation, and Marketplace US East (Ashburn) V Create Bucket Help Object Storage & Archive Storage Buckets in sandbo Object Storage provides unlimited, Create Bucket Name Emit Object Events Create automation based on object state changes using the Events Service. Uncommitted Multipart Uploads Cleanup Buckets Create lifecycle rule to automatically delete uncommitted multipart uploads older than 7 days. Leam n more List scope Compartment sandbox oundations8 (rooty/sandbox Encryption bucket.20230518.:2359 Encrypt using Oracle managed keys Leaves all encryption-related maters to Oracle. Encrypt using customer- r-managed keys Requires a valid key from vault that you have access to. Leammore Vault in sandbox (Change Compartment) vaultdemo Service logs Resources: 1 (2 total logs) 0 Logs enabled: 0 Logs not enabled: 2 Managelogs C Master Encryption Key in sandbox (Change Compartment) MEKdemo Tag filters no tag filters applied addiclear Tags Add tags to organize your resources. What canl do with tagging? Tag namespace None (add a free-form tag) Tag key Tag value X ::: Add tag Create Cancel