SAML
Summary #
Sends the user’s identity from one place (IdP) to the requesting Service Provider (Decisions) through an exchange of digitally signed XML documents
IdP (signed XML) -> SP
Due to its many benefits, SAML is a widely adopted enterprise solution
How it works? #
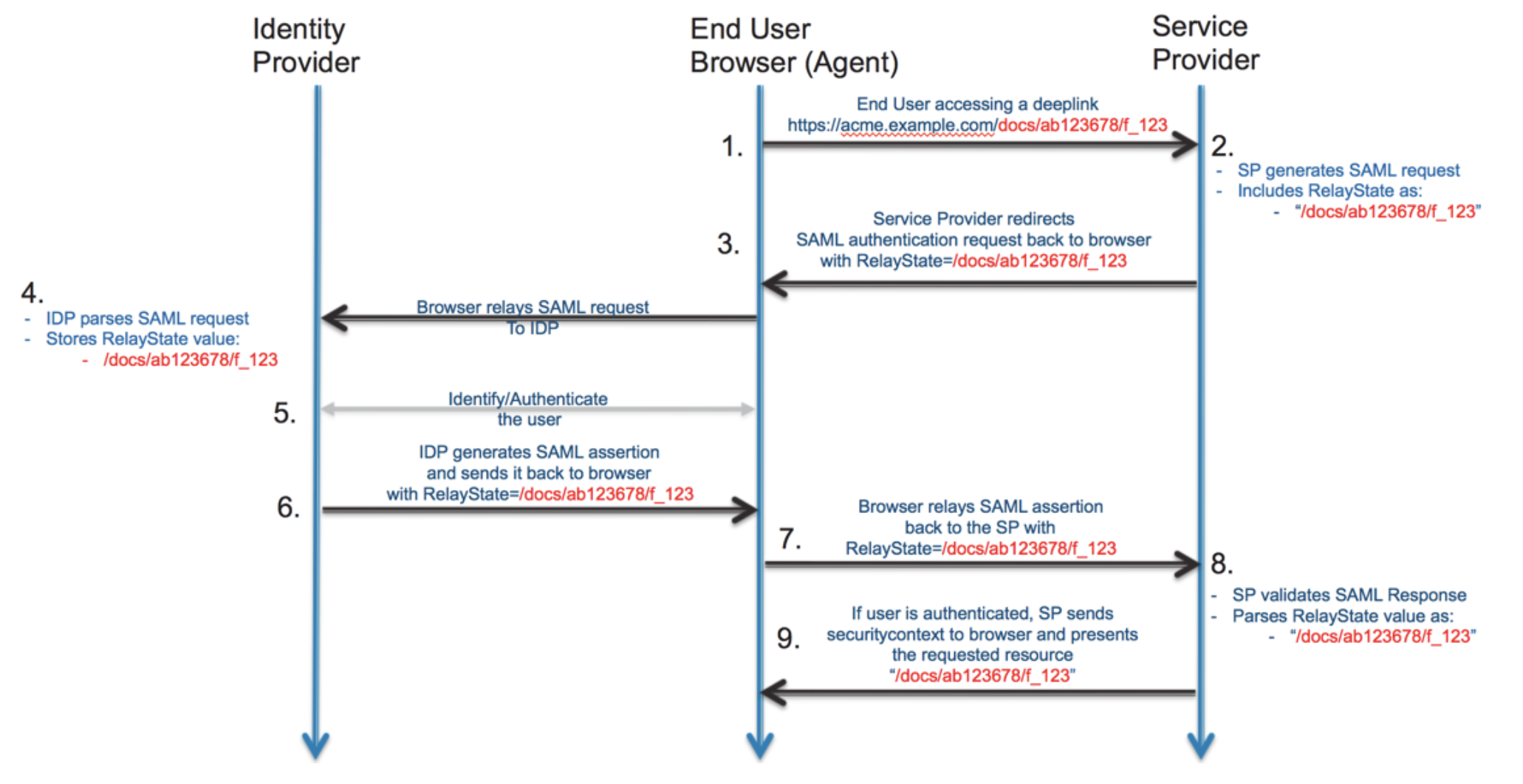
- The user opens their browser and navigates to the service provider’s web application, which uses an identity provider for authentication.
- The web application responds with a SAML request.
- The browser passes SAML request to the identity provider.
- The identity provider parses the SAML request.
- The identity provider authenticates the user by prompting for a username and password or some other authentication factor. NOTE: The identity provider will skip this step if the user is already authenticated.
- The identity provider generates the SAML response and returns it to the user’s browser.
- The browser sends the generated SAML response to the service provider’s web application which verifies it.
- If the verification succeeds, the web application grants the user access.
SAML Request #
SAML Assertion #
A SAML assertion is an XML packet that contains authentication and authorization information about the identity.
You can think of assertions as statements made by the IdP about a user.
The SP uses SAML assertions to create and configure sessions when a user logs in to a service.
SAML assertions are the messages that are exchanged between an identity provider (IdP) and service provider (SP) that confidentially identify who a user is, what pertinent information exists
about them, and what they’re authorized or entitled to access.
- Those messages also specify security conditions (such as the source of the assertion) and assurances that assertions are valid.
- XML schemas are used to author assertions, providing a rich canvas to specify very specific conditions.
- They’re communicated following successful authentication of the SAML request. The SAML response is sent in lieu of a username and password being shared over the wire. ref
There are three types of SAML assertions: #
Authentication assertions.
They help to confirm the identity of the user. Authentication assertions contain statements about which method a user has used to authenticate to the service, such as password, multi-factor authentication (MFA), or Kerberos. They also indicate the time the user logged in to the platform.
Attribute assertions
These are specific datasets that provide information about the user, such as first name, last name, email address, etc. The attributes that SAML uses to identify a user must be the same in both IdP and SP directories.
Authorization assertions
Authorization assertions are typically issued by SAML policy decision point (PDP) when a user requests access to a specified resource from the SP. They communicate whether a user’s authorization attempt is successful or not.
SAML Response #
Why SAML was created? #
SAML vs LDAP
- tags
- diff
The need of SAML occurred when enterprises started moving to cloud to save cost.
It is not safe to allow access to Active Directory from cloud network via LDAP.
It leverages the ability of browsers to redirect the request to another application, which is in enterprise DC and can connect to the user store safely(IdP).
The difference between SAML and LDAP is that SAML is designed for cloud-based connections using only an IdP and SP to communicate user data. - LDAP, however, is typically used for accessing on-premises resources by installing a client on the user’s device to connect with a directory service. - inside enterprise network
SAML vs OAuth2 #
OAuth and SAML are both protocols we use for allowing access. However, the primary difference between the two is that we use SAML for authentication and OAuth for authorization.
If we revisit the airline analogy, the passenger's ID is the SAML assertion, and the ticket the OAuth token. The airline uses the ID to verify the passenger’s identity before allowing them to board the aircraft. However, once the passengers are on the plane, the flight attendants use the ticket to confirm the passengers’ status and entitlement. For example, they may have a first-class ticket giving them access to seats and amenities not accessible by passengers in economy.
Google IdP #
Used this in Azm X CMS, setting up
Check logs here