Public-key Cryptography
tags :
Summary #
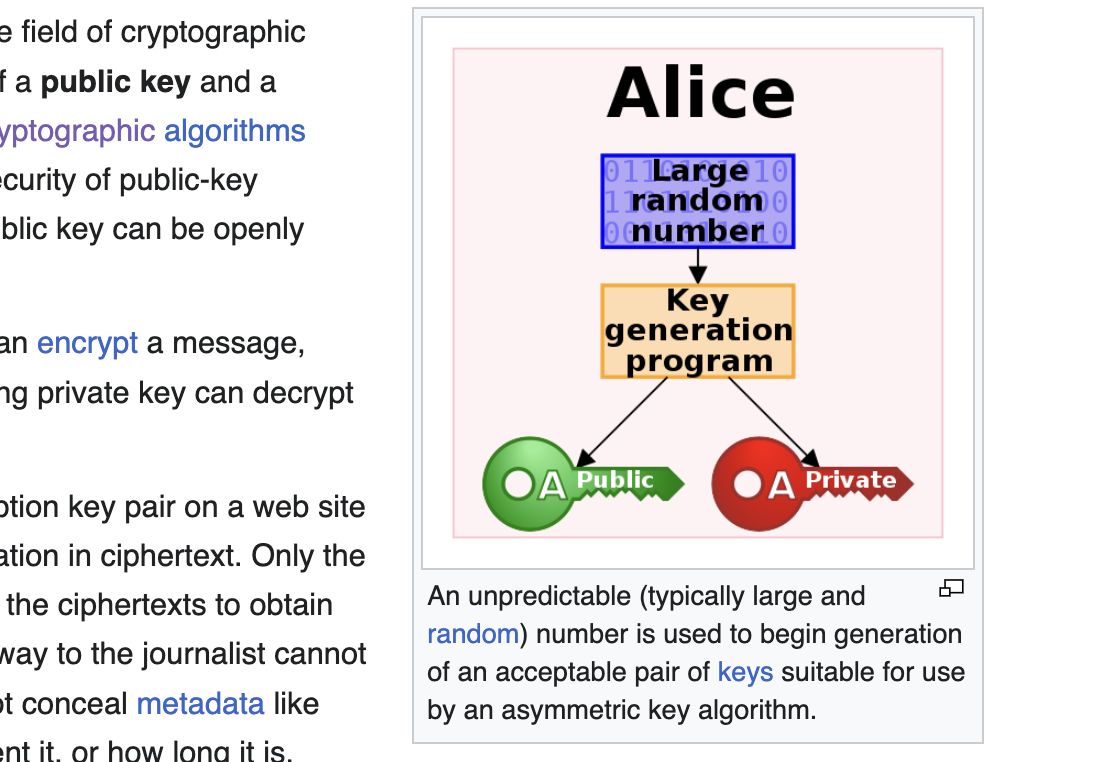
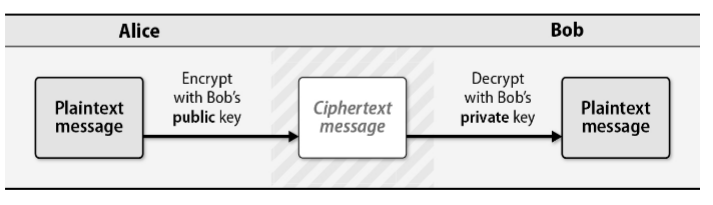
Limitation of symmetric key is exchange of private key, public key only the public is shared and private key never leaves the owner.
Not efficient: computationally expensive.
#
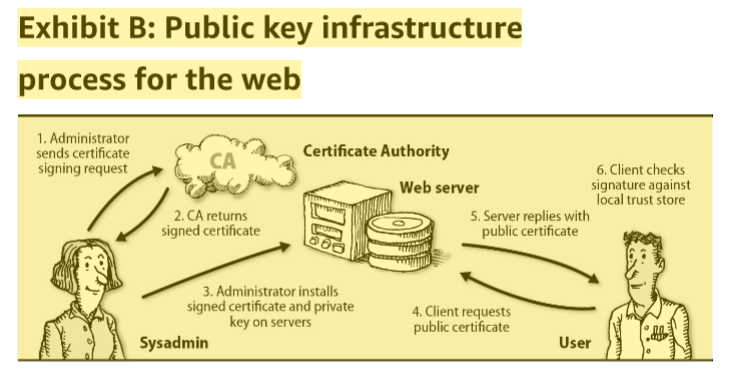
Validating the authenticity of public keys at Internet scale is a formidable challenge. The Public Key Infrastructure, used to implement on the web, address this problem by trusting a third party known as to vouch for public keys. issues certificate that the clients(e.g. browser) can trust using trust chain.
Creating Public and private keys using #
openssl genrsa -out rsa.private 1024 # generate private key
openssl rsa -in private.key -pubout -out public.key # extract public key from private key
File Format and #
The public and Private keys are stored in
s #
#
public and private key pasting issue #
In invoicing-apis project generating private and public keys with copying these keys to the files did not work.
- for generated private key using `mv` command to rename the private key
- the issued “binarySecurityToken”: “base64 of public key in X.509 format”, when copy pasted was not
working, using python library to decode and write the key to file worked
certb64 = "binarySecurityToken" public_cert = base64.b64decode(cert64) open("cert2.pem", "w").write(public_cert.decode())
exporting of base64 issue in shell #
export ZATCA_BINARY_SECURITY_TOKEN="TUlJQ0tqQ0NBYytnQXdJQkFnSUdBWXBwNzZQRk1Bb0dDQ3FHU000OUJBTUNNQlV4RXpBUkJnTlZCQU1NQ21WSmJuWnZhV05wYm1jd0hoY05Nak13T1RBMk1UQXdNREl5V2hjTk1qZ3dPVEExTWpFd01EQXdXakJjTVFzd0NRWURWUVFHRXdKVFFURVdNQlFHQTFVRUN3d05VbWw1WVdSb0lFSnlZVzVqYURFTk1Bc0dBMVVFQ2d3RVFWcE5XREVtTUNRR0ExVUVBd3dkVkZOVUxUZzROalF6TVRFME5TMHpNVEV4TVRFeE1URXhNREV4TVRNd1ZqQVFCZ2NxaGtqT1BRSUJCZ1VyZ1FRQUNnTkNBQVN3c1Q2K01iRVV4WTNwTFUyYnJINHBUS0JyNTd5TlFuUFJzSlRZSjBnYUtrMW4wbmtHNnA2RTlLeG9mRUExdHlDekV2OUIrR3pENkZUR0JiNjU3SDE1bzRIR01JSERNQXdHQTFVZEV3RUIvd1FDTUFBd2diSUdBMVVkRVFTQnFqQ0JwNlNCcERDQm9URTdNRGtHQTFVRUJBd3lNUzFVVTFSOE1pMVVVMVI4TXkxbFpESXlaakZrT0MxbE5tRXlMVEV4TVRndE9XSTFPQzFrT1dFNFpqRXhaVFEwTldZeEh6QWRCZ29Ka2lhSmsvSXNaQUVCREE4ek1URXhNVEV4TVRFeE1ERXhNVE14RFRBTEJnTlZCQXdNQkRFeE1URXhFVEFQQmdOVkJCb01DRkpTVWtReU9USTVNUjh3SFFZRFZRUVBEQlpTWldGc0lHVnpkR0YwWlNCaFkzUnBkbWwwYVdWek1Bb0dDQ3FHU000OUJBTUNBMGtBTUVZQ0lRRFBLejk4dTcvcVUxQ3NSdHQrMy9xeUdOVy92TmFyMDQ1a20yWk02bVNYQ0FJaEFNeTg1MGg0MDV1Y3B0S3ZVSTFLZm5KVlVBWHc4TGkrMmh3Y0ZFSk0wUStK"
was changing the cert while reading it. `echo $ZATCA_BINARY_SECURITY_TOKEN` was different: there was an issue with “j”, used online service this compare the text