PKCE
- tags
- Security
PKCE (Proof Key for Code Exchange) in OAuth2 #
Overview #
originally developed for mobile application
A
security extension to OAuth 2.0, primarily designed to enhance the security of public clients.Mitigates the risk of interception of the authorization code by malicious actors.
It is recommended even for Confidentials Client to avoid subtle attacks authorization code injection attack
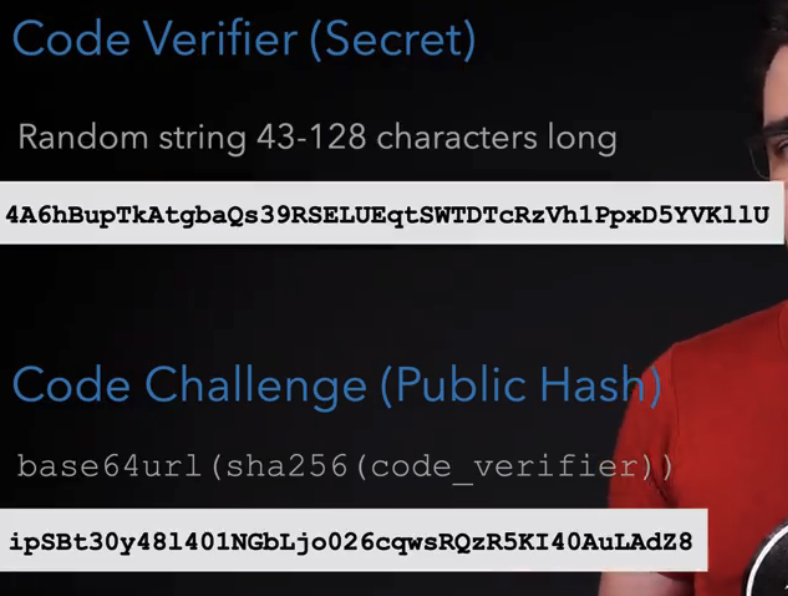
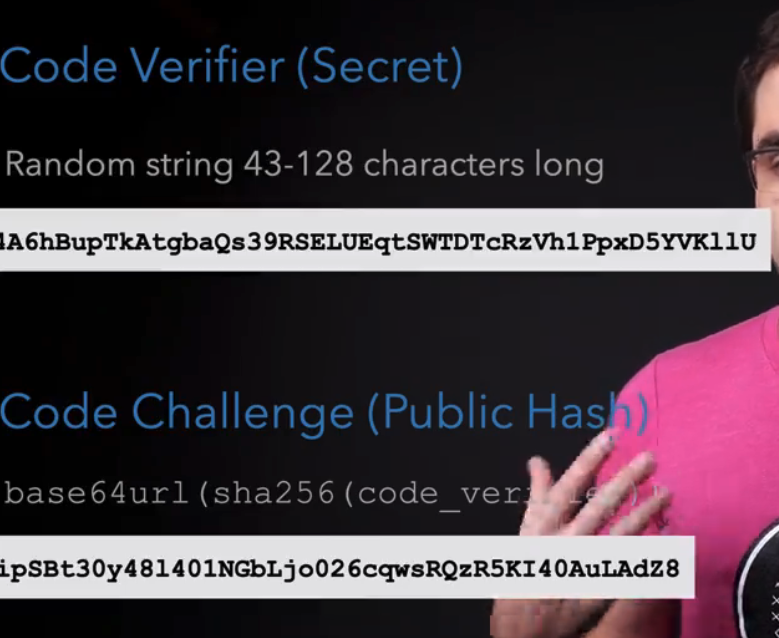
length should between 43-128
- state was used to provide CSRF Forgeries protection but PKCE can be used for that as well now
- state is used to store application state: which page or url to redirect to
- if oauth server does not support pkce then state should be random value
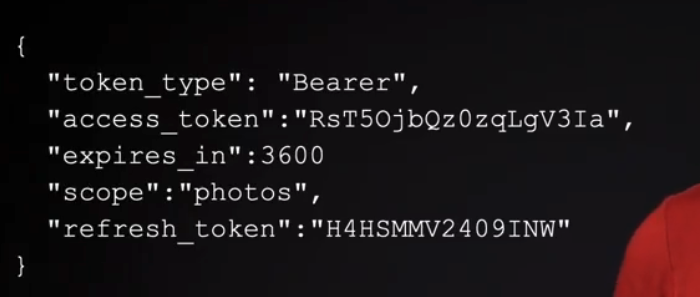
- refresh token are like Auth Code
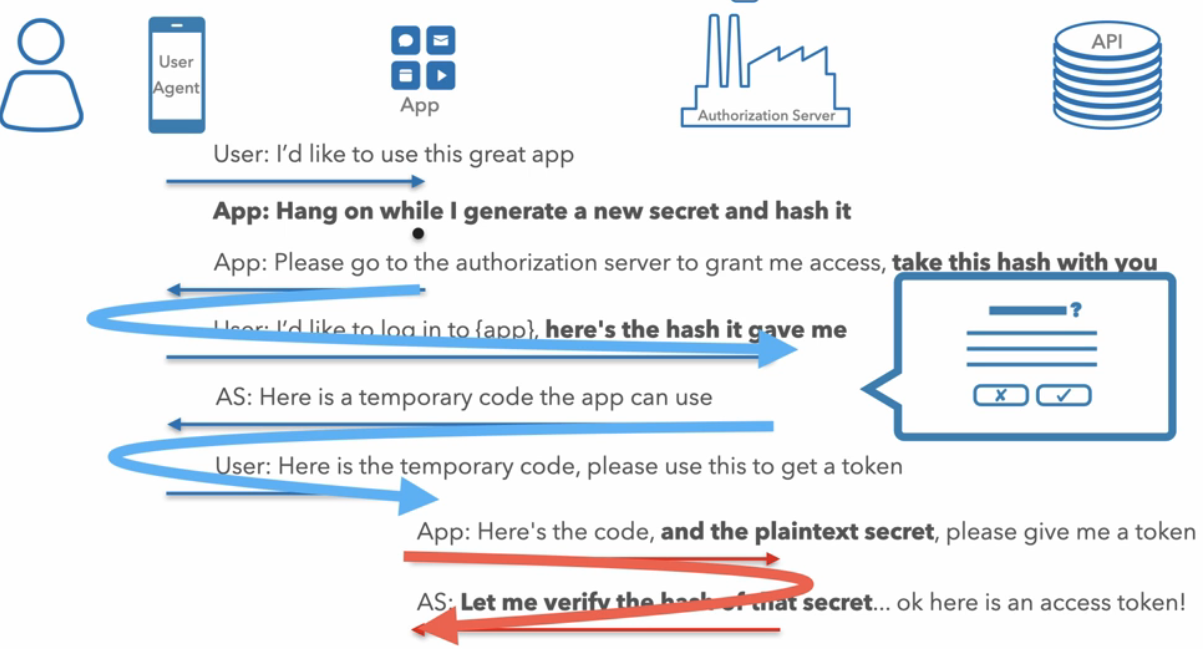
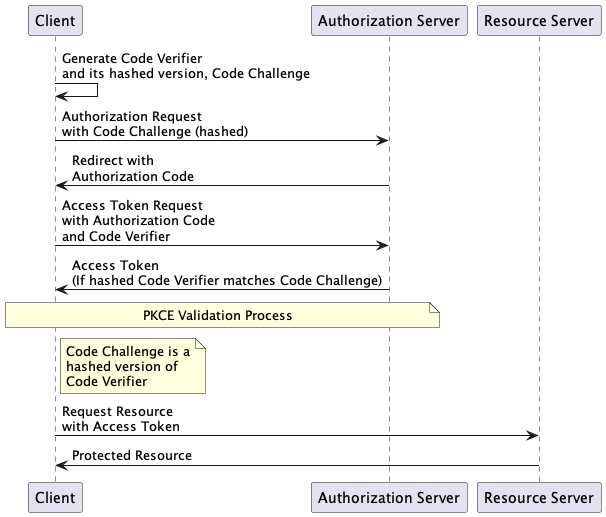
How It Works #
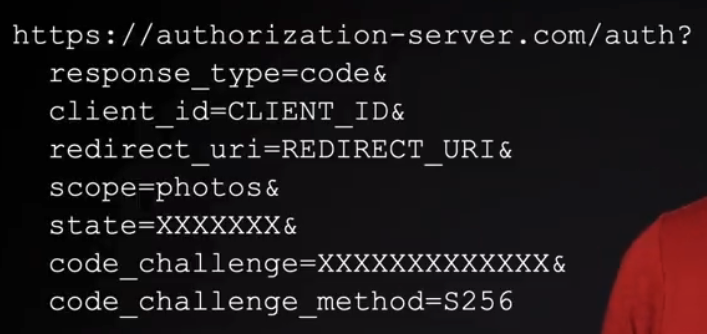
- The client generates a secret, known as the ‘Code Verifier’, and its transformed version, hash, the ‘Code Challenge’.
- The ‘Code Challenge’ is sent with the authorization request, while the ‘Code Verifier’ is stored by the client.
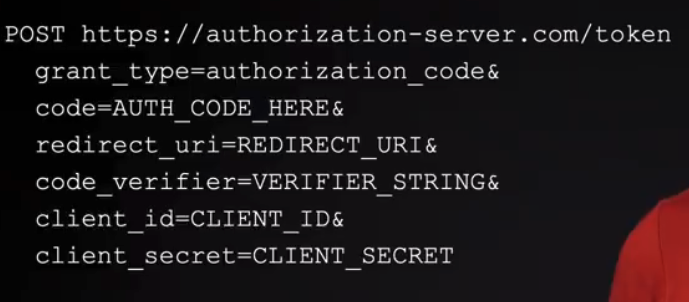
- Upon receiving the authorization code, the client sends it along with the ‘Code Verifier’ to the token endpoint.
- The server compares the transformed ‘Code Verifier’ with the ‘Code Challenge’ it received initially to ensure authenticity.
Purpose #
- Protects against authorization code interception attacks.
- Ensures that the token is only issued to the client that initiated the authorization request.
Use Cases #
- Ideal for public clients where the client secret cannot be securely stored.
- Commonly used in mobile and single-page applications.
Benefits #
- Enhances security in public client scenarios.
- Easy to implement and does not require client secret storage.