Networking in OCI
tags :
Networking in OCI #
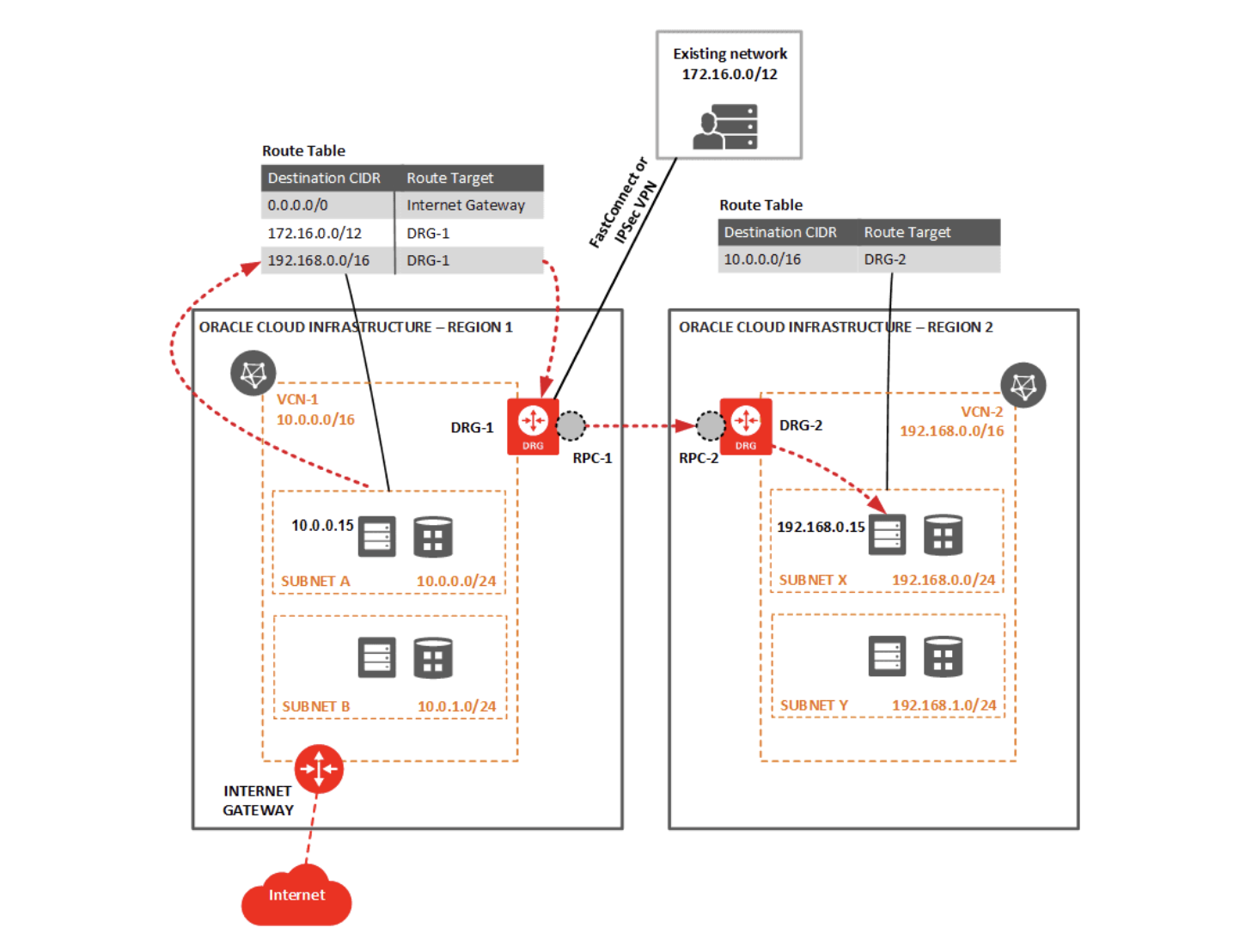
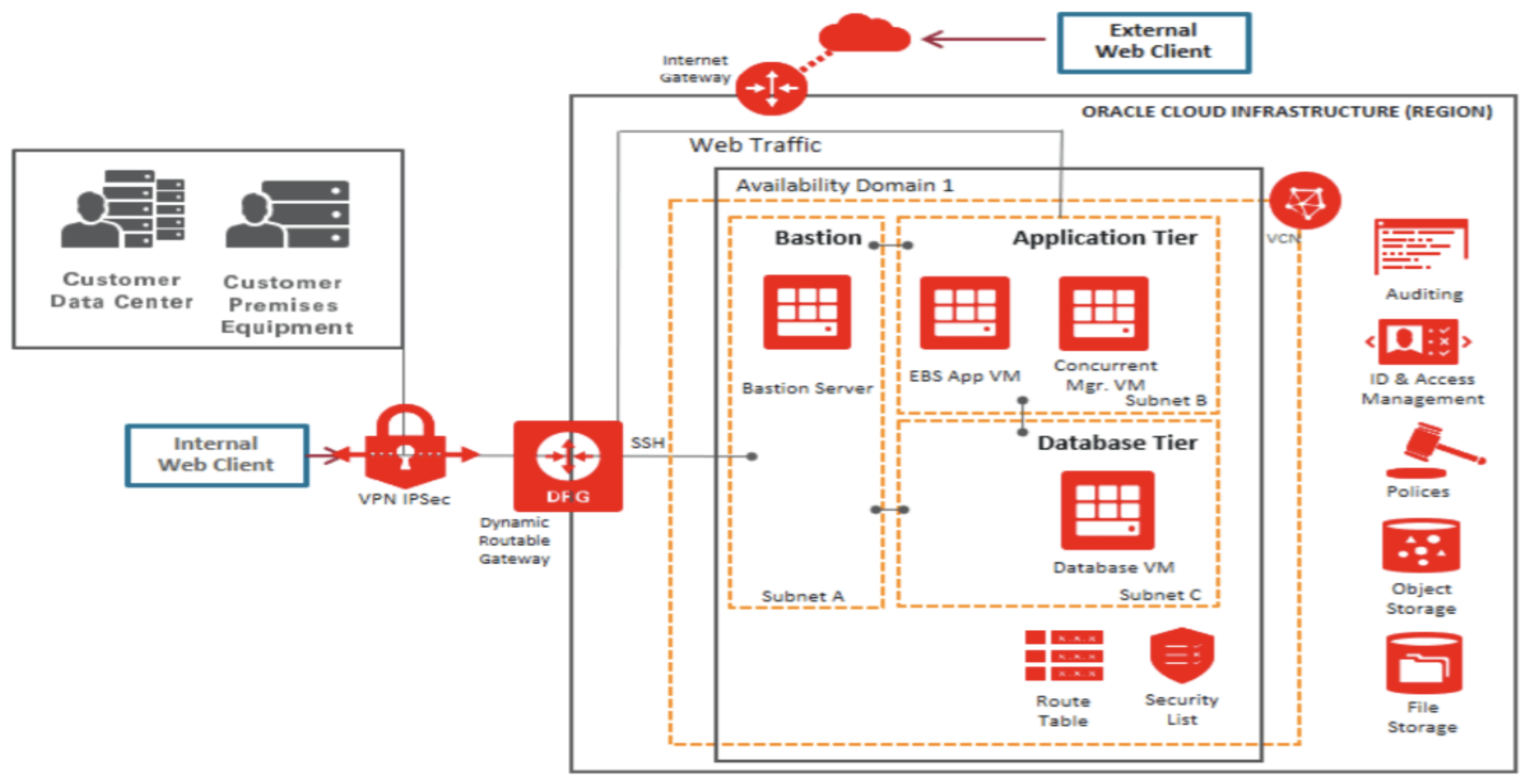
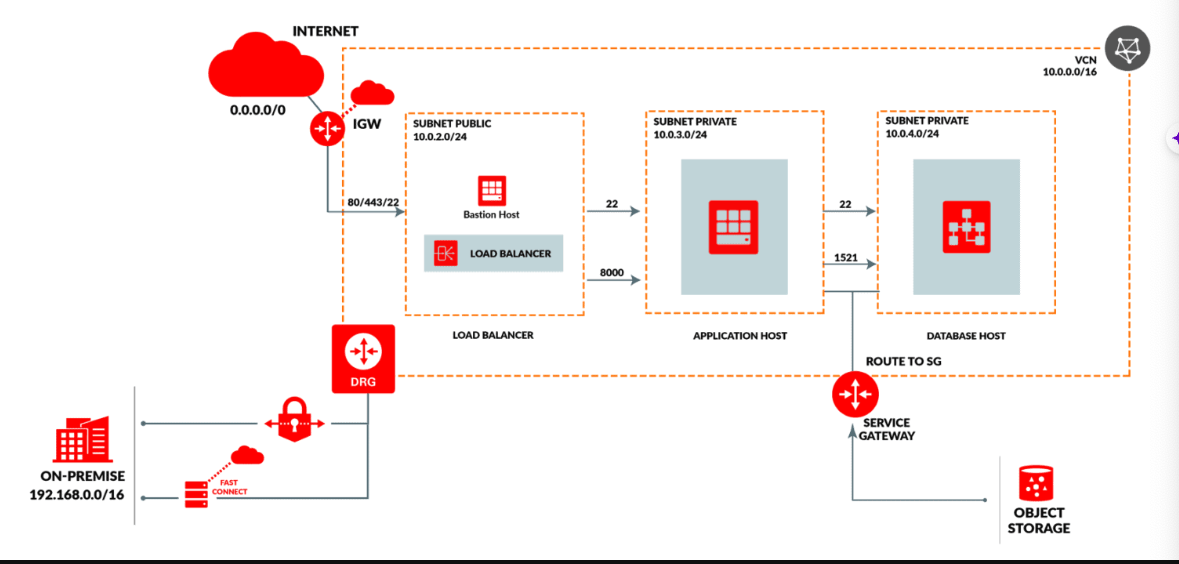
A typical OCI networking architecture has the following network components: #
Virtual Cloud Network (VCN) and inside this VCN, we have three subnets.
- One public subnet for Bastion Host and Load Balancer, and
- two private subnets, one for application host and one for database host.
- An Internet Gateway to connect to the internet from public subnet.
A Service Gateway to access OCI Object Storage and other OCI services.
A Dynamic Routing Gateway (DRG) for private access from an on-premises data center to OCI.
oci networking architecture
Components Of OCI Network #
VCN in OCI #
Subnet #
- Bigger Network divided into multiple smaller networks
- A subnet can be AD specific or regional
- You can have multiple subnets in an Availability Domain (AD)
There are two types of Subnets #
- Public Subnet: In which public-facing resources reside like instance, load balancer, object storage.
- Private Subnet: In which highly secured resources reside like Database.
Route Table #
- VCN uses virtual route tables to send traffic out of the VCN (for example, to the internet, to your on-premises network, or to a peered VCN).
- These route tables have route rules that provide mapping for traffic from subnet via gateways to other subnets or destinations outside VCN
- Each rule specifies a destination CIDR block and the target (the next hop) for any traffic that matches that CIDR.
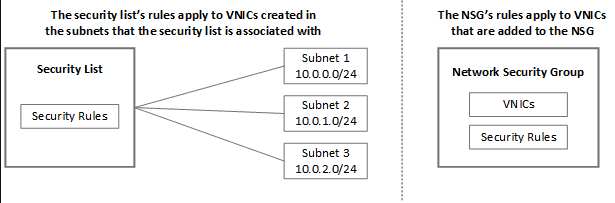
Security List #
- Security List is a common set of firewall rules associated with a subnet and applied to all compute instances in that subnet.
- Security List specifies two types of traffic allowed:
- Ingress: Incoming Traffic
- Egress: Outgoing Traffic
Firewall rules in OCI are defined at the subnet level and not at compute instance level.
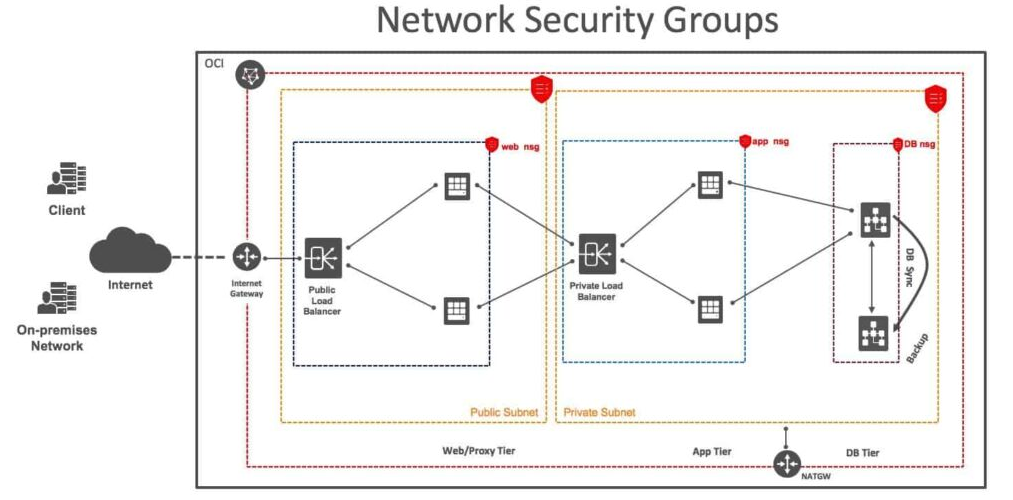
Network Security Group (NSG) #
- Network Security Groups are another method for implementing security rules.
- NSGs provides a virtual Firewall for a set of Cloud resources that have the same security postures.
Read our blog to know more about Network Security Groups Vs. Security List: When to use What?
Resources That Support Network Security Groups: #
- Compute instances
- Load balancers
- DB systems
- Autonomous Databases
Security list vs NSG #
A Security list lets you define a set of security rules that applies to all the VNICs in a subnet whereas Network Security Groups let you define a set of security rules that applies to a group of VNICs of your choice.
NSGs’ security rules apply only to the resources in that NSG. By contrast, Security Lists’ rules apply to all the resources in a subnet that uses the list.
NSGs consist of a set of ingress and egress security rules that apply only to a set of VNICs of your choice in a single VCN.
Unlike with Security List, the VCN does not have a default NSGs. Also, the NSGs you create are initially empty. They have no default security rules.
A Security List is used at the packet level.
NSGs are another way to implement security rules.
Security Lists have separate and different limits compared to the Network Security Groups.
When To Use What? #
- Security Lists provide comprehensive security to applications with security rules applied to every subnet.
- But if you have multiple resources that require different security postures security postures within a subnet, and you need to control the traffic at a more granular application level, then you can create those granular rules and add multiple resources to them using Network Security Groups.
Gateways #
There are 5 gateways in OCI Networking:
Internet Gateway (IG): It provides a path for network traffic between the internet and OCI VCN. Compute Instance in Public Subnet by default won’t be able to connect to the internet without IG.
NAT Gateway: It gives resources without public IP addresses access to the internet without allowing incoming traffic from the internet to that resources.
Service Gateway: It allows OCI resources to access public OCI services without the use of the Internet or NAT Gateway Eg: Object Storage.
Dynamic Routing Gateway (DRG): DRG provides a single point of entry for remote network paths coming into VCN. It provides a path for VCN to communicate across regions or outside the region to On-premise. Each VCN can have a single DRG.
Local Peering Gateway (LPG): Used to establish communication between resources of different VCNs within a Region.
Read our blog to know more in detail about Gateways in OCI: Internet Gateway, NAT Gateway, Service Gateway, Dynamic Routing Gateway
Load Balancer #
Load Balancer is used to distribute the traffic coming from a source to multiple backend servers. It improves resource utilization, scaling & high availability. We can create a public or private load balancer within a VCN.
Public load balancer has a public IP address that is accessible from the internet. Private load balancer has an IP address from the hosting subnet, which is visible only within your VCN. load balancer in oci
VCN Peering #
VCN Peering is the process of connecting multiple virtual cloud networks (VCN) With peering, instances in two VCNs communicate as if they are in the same network VCN Peering can be of two types Local VCN Peering (within Region) using LPG & Remote VCN Peering (across Regions) using DRG. Local VCN Peering(LPG): The process of creating a path between VCNs for communication in a single region. Remote Peering Connection: The process of creating a path between VCNs communication across regions. Local VCN Peering is supported in all OCI Regions.