Encryption
Summary #
Def 1 #
Encryption is a means of securing digital data using one or more mathematical techniques, along with a password or “key” used to decrypt the information. The encryption process translates information using an algorithm that makes the original information unreadable. ref
Def 2 #
Encryption is the process of using a to convert plain text messages to unreadable
Decryption: is the reverse of that process. mathematically encryption is: function(plain text) = ciphertext
Cipher #
A cryptographic Algorithm set of mathematical steps taken to secure a message.
Difference between Cipher and hash #
a cipher is a two-way operation, whereas hashing is a one-way operation. ref
Ciphertext #
(plain text) = ciphertext function(plain text) = ciphertext
cryptography messages, plain text message encrypted with .
Difference between Encryption and Signing? #
Encryption happens with public key, Signing is done with private key. ref
Encryption #
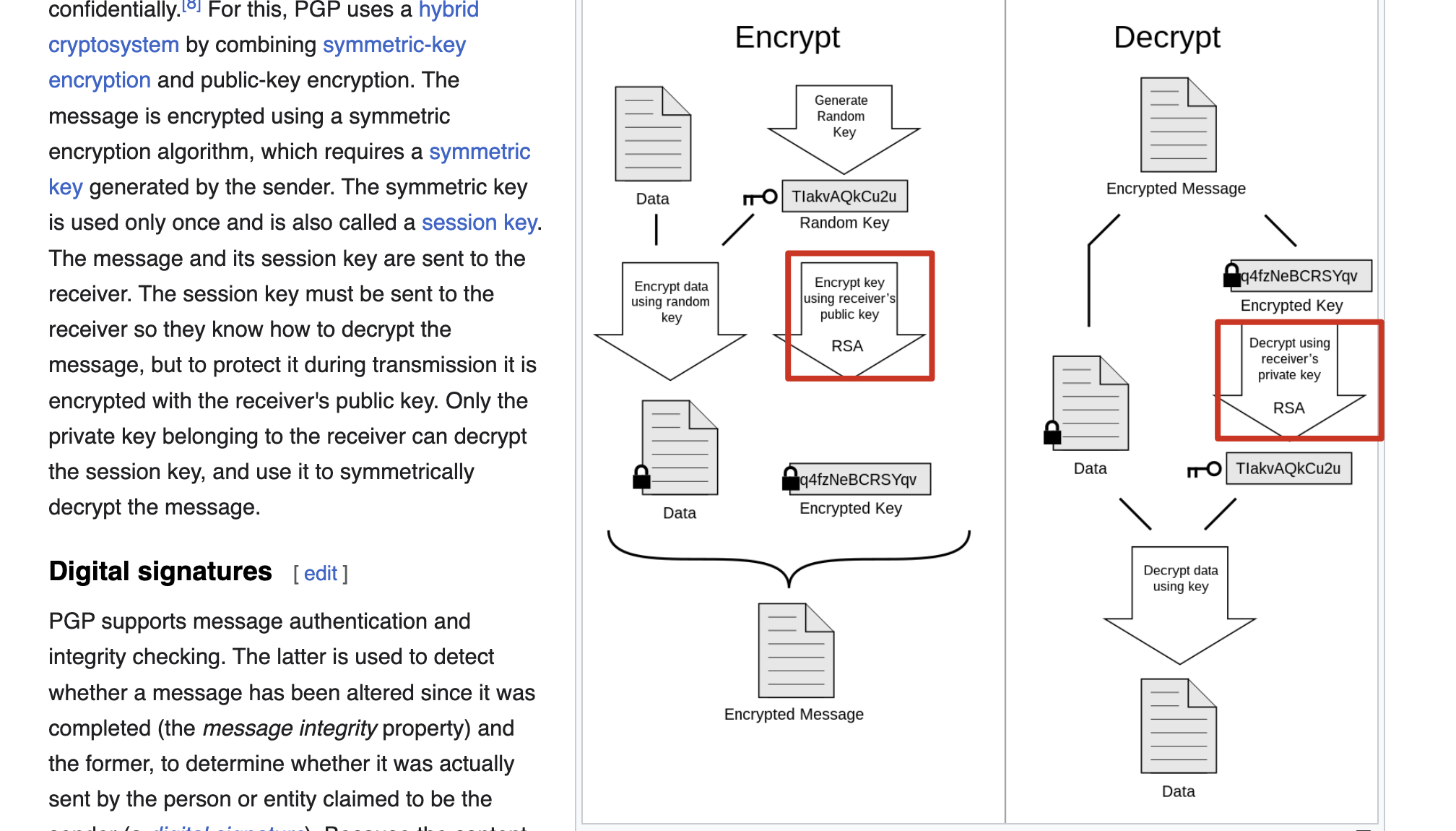
Threats loom ever present in our digital world, which is why methods of securing data are constantly advancing. Tactics like encryption are used every day on sensitive data-at-rest or in-motion. Encryption is the process of putting data in the form of plaintext into an encryption algorithm, and producing a ciphertext. Ciphertext is a form of data where all the patterns of letters that create words in the plaintext are scrambled into a new text that cannot be read without decrypting the data. Encryption uses a key to ensure the ciphertext cannot be deciphered by anyone but the authorized recipient.
Signing #
Signing of data works to authenticate the sender of the data and tends to implement a form of encryption in its process. The process of signing emails, sensitive data, and other information has become necessary, as it verifies the identity of the sender and ensures the data has not been altered in transit. If a Man in the Middle attack occurred and the data was altered or compromised by the attacker, the recipient of the information would know that this has occurred. The attacker could alter the data, but as they do not have the key used by the sender to sign the data, the recipient of the data will know not to trust the sent data when analyzing the key and data.