Authorization Code Grant
tags :
Grant Types or OAuth flow in OAuth2 #
Description #
- Involves an extra step of exchanging an Authorization Code for an Access Token, adding a layer of Security.
- Can be enhanced with PKCE (Proof Key for Code Exchange), where the client creates a code verifier and its hashed version, the code challenge, to protect against interception attacks.
Use Cases #
- Web applications
- Server-to-server communication
- Suitable for public clients like mobile apps and single-page applications when used with PKCE.
Security #
- Highly secure due to the extra authorization code exchange step.
- PKCE adds an additional layer of security for public clients by ensuring that the access token is only granted to the authentic requesting client.
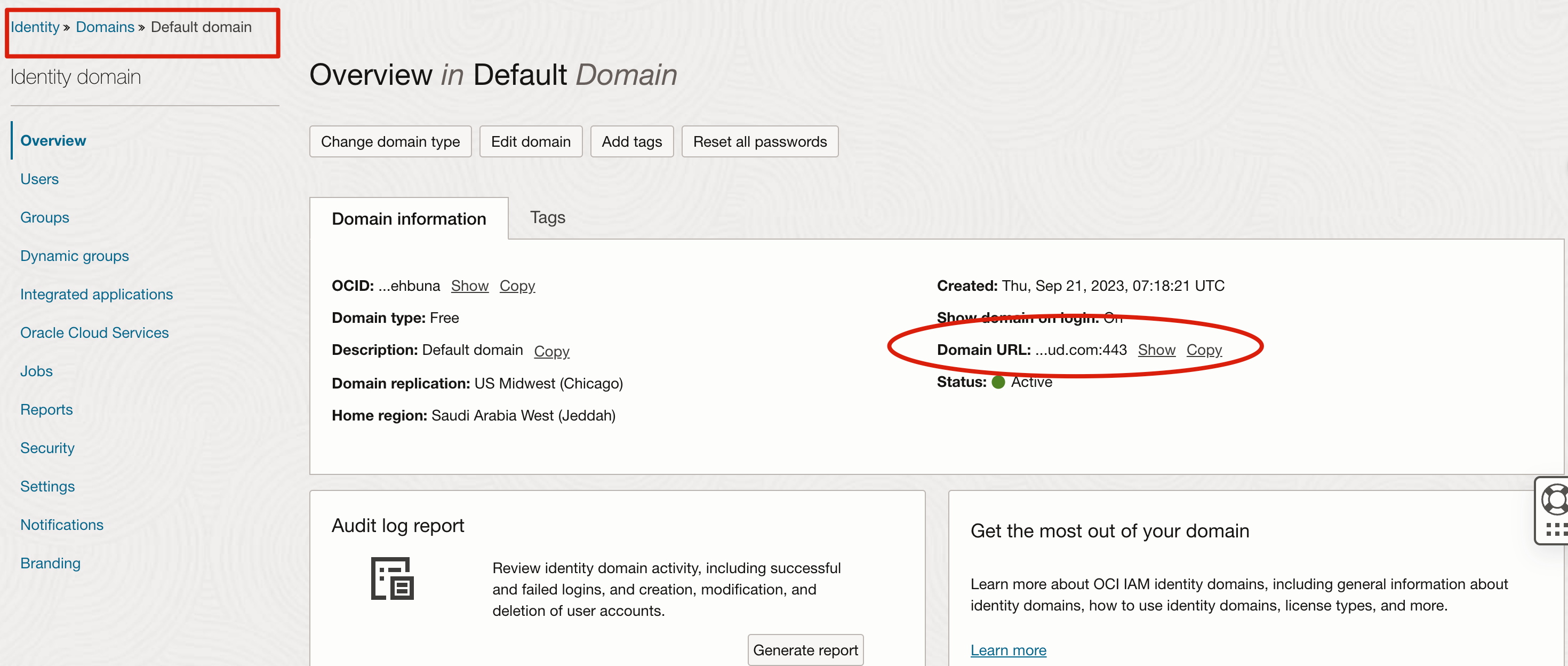
Implementing it in Identity Domain in OCI #
Get the domain URL #
append “oauth2/v1/authorize” to the URL #
https://domainurl:port/oauth2/v1/authorize
add query parameters #
- client_id
- response_type=token
- redirect_uri
- state (CSRF Forgeries)
enhance it with PKCE #
- state
- code_challenge
- cod_challengemethod
Scope #
scope=openid is needed because application needs to know who the user is.
- When a client application initiates the PKCE flow, it needs to specify that it wants to authenticate users and obtain identity-related information.
- The scope=openid indicates that the client application is interested in receiving OpenID Connect Claim or user attributes, such as user ID, name, email, etc.
- These claims are essential for identifying and verifying the user’s identity.