API Gateway in OCI
tags :
API Gateway in OCI #
The API Gateway service enables you to publish
- APIs with private endpoints that are accessible from within your network, and
- which you can expose with public IP addresses if you want them to accept internet traffic.
- The endpoints support
- API validation,
- request and response transformation,
- CORS,
- Authentication and Authorization, and
- request limiting.
Using the API Gateway service, you create one or more
API gateways in a regional subnet to process traffic from API clients and
route it to back-end services.
You can use a single API gateway to link multiple back-end services
- such as Load Balancer
- compute instances, and
- Functions in OCI into a single consolidated API endpoint.
Deployments #
- Base urls or backend endpoints can be configured here that gateway will redirect to
Basic information #
Routes #
- request Validations
- Header Transformation
select HTTP method and configure backend URL to redirect to.
- It is possible to add context variables
Authentication #
The gateway endpoint can be authenticated with JWT OAuth2 and there three options to validate the access token.
JWT Token Verification Methods in OCI Gateway #
OAuth2 Introspection
- Mechanism: Sends token to the introspection endpoint of the OAuth server, which returns token information.
- Security Considerations: Highly secure, real-time token status validation.
- Use Case: Best for scenarios requiring real-time token validation, especially when token revocation is a concern.
- Considerations: Introduces latency due to extra network call; relies on endpoint availability.
Remote JWKS
- Mechanism: Dynamically retrieves public keys from the JWKS endpoint of the authorization server.
- Security Considerations: Secure, adapts to key rotations.
- Use Case: Ideal for scenarios where the authorization server supports JWKS and key rotation is frequent.
- Considerations: Requires JWKS endpoint availability; minor latency in key retrieval.
Static Keys
- Mechanism: Uses pre-configured keys within the API Gateway for validation.
- Security Considerations: Secure but less flexible; vulnerable if keys are compromised and not updated promptly.
- Use Case: Suitable when the authorization server doesn’t provide JWKS or introspection, or when minimizing network calls is a priority.
- Considerations: Requires manual key updates; not ideal for dynamic environments.
Adding Authorization or access control to API Gateway in OCI #
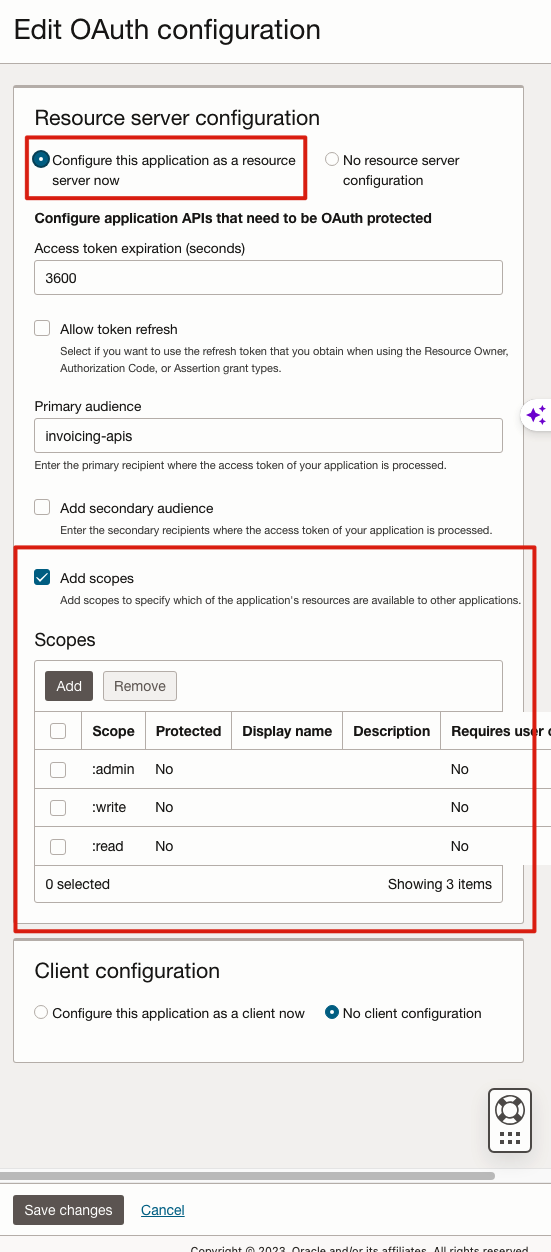
Create Integrated Application with “Confidential Application” type #
Add resource server configuration
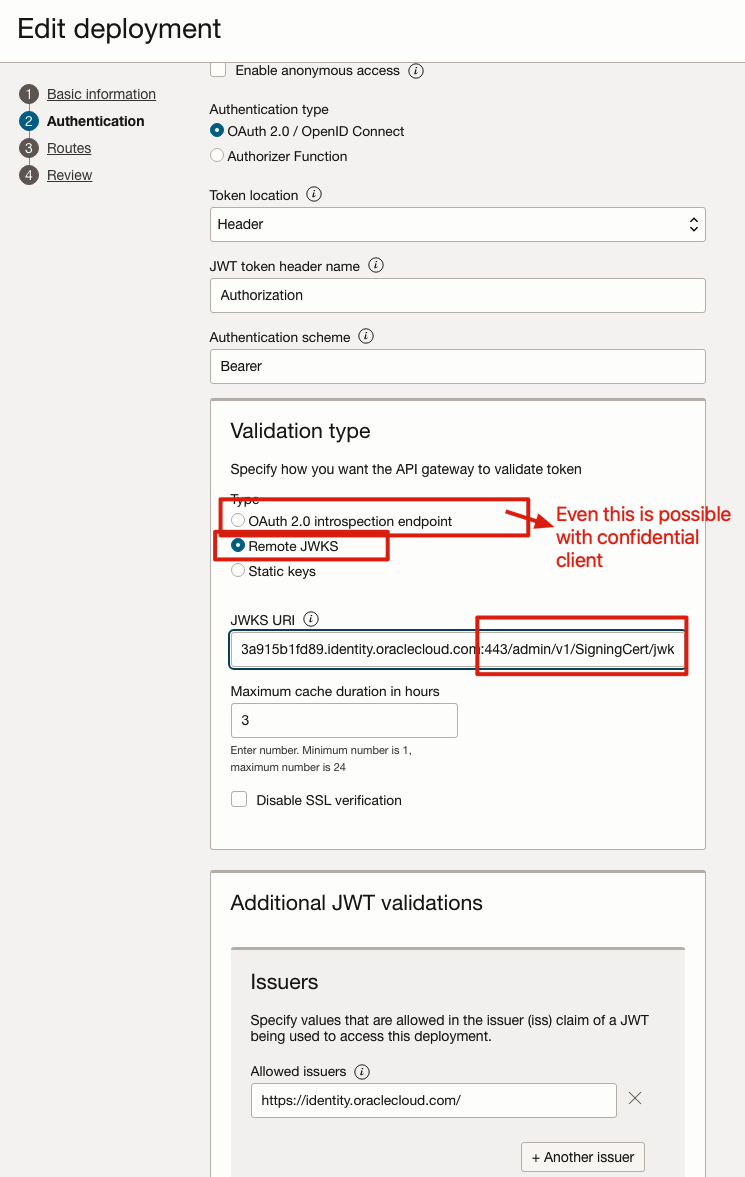
JWKS format: “$var.domain_url/admin/v1/SigningCert/jwk”
Adding dynamic route with ID #
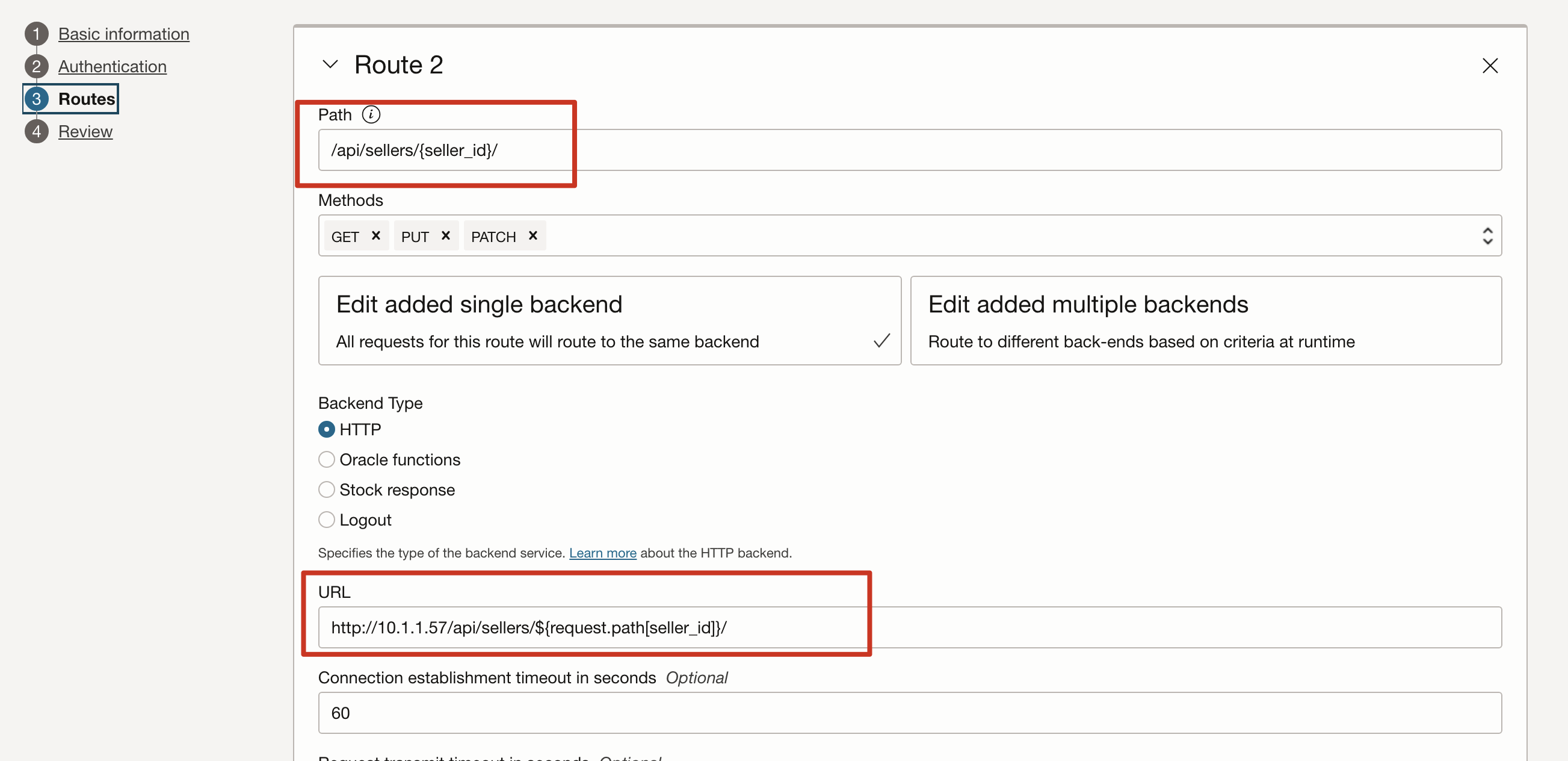 Path: api/sellers/seller_id
backend URL: http://10.1.1.57/api/sellers/$request.path[seller_id]/
Path: api/sellers/seller_id
backend URL: http://10.1.1.57/api/sellers/$request.path[seller_id]/